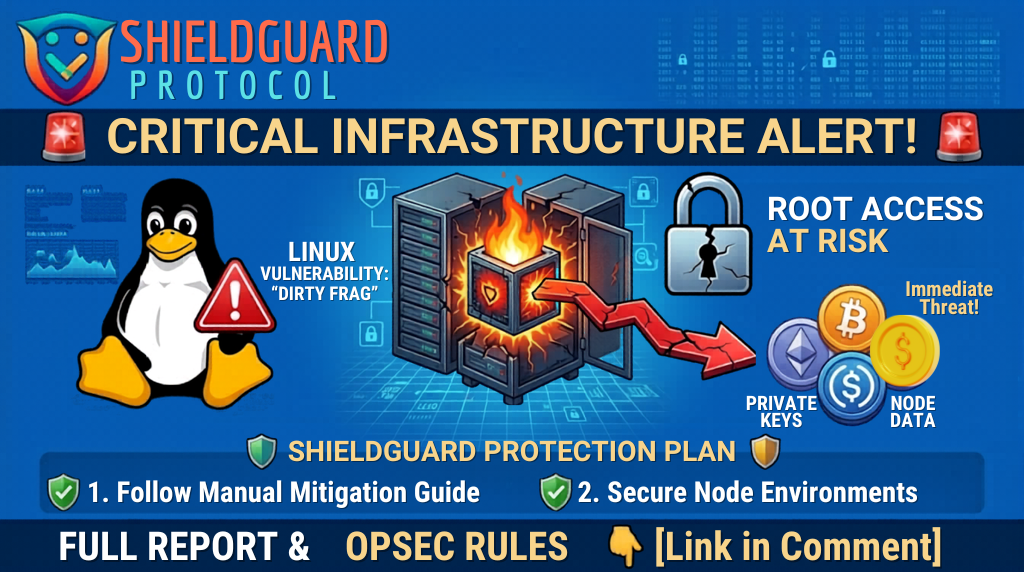
🚨 Critical Infrastructure Alert: The “Dirty Frag” Linux Kernel Exploit 🚨
🔍 Incident Overview
A major unpatched security vulnerability chain, dubbed “Dirty Frag” (CVE-2026-43284 & CVE-2026-43500), has been disclosed today. This is a Local Privilege Escalation (LPE) flaw in the Linux kernel that allows an attacker with low-level system access to instantly gain full root (administrative) control. 🛡️💻
Unlike many common exploits, “Dirty Frag” is a deterministic logic bug. It exploits how the kernel handles in-place cryptographic operations and memory fragments. Because it affects core kernel subsystems (IPsec ESP and RxRPC), it impacts nearly all major distributions, including Ubuntu, RHEL, Fedora, Debian, and CentOS Stream. ⚠️
🛡️ Why This is Critical for Crypto & Web3
For the ShieldGuard community and ecosystem, this vulnerability poses a specific set of high-stakes risks:
- 🔑 Private Key Theft: If you run a validator, a node, or a hot wallet on a Linux-based VPS or server, an attacker who gains basic access (via a separate app or service) can use “Dirty Frag” to escalate to root. Once they are root, they can access sensitive memory, extract private keys, and bypass local encryption.
- 🤖 Node Manipulation: Attackers can modify node software at the system level to redirect rewards, sign malicious blocks, or disrupt your participation in the network.
📦 Container Breaches: While hardened Kubernetes environments offer some protection, many standard container setups share the host kernel. A breach in one container could lead to a full takeover of the host machine. 📉
🛠️ How to Protect Your Setup: Preventive Education
Since official patches from all OS vendors are still rolling out today, you must take immediate manual action to secure your servers:
1.🚫 Blacklist Vulnerable Modules: Disable the affected kernel modules (esp4, esp6, and rxrpc) to close the attack vector. Run the following command as root:
sh -c "printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' > /etc/modprobe.d/dirtyfrag.conf; rmmod esp4 esp6 rxrpc"
2.Isolate Your Environment: Ensure your crypto nodes are not running on “shared” hosting where other users have SSH access. Use dedicated instances and minimize installed software to reduce the surface area for initial local access.
3.🕵️ Monitor for Escalation: Watch your system logs for unusual sudo attempts or processes suddenly gaining root privileges from non-root accounts.
🛡️ Join the ShieldGuard Movement Protecting the infrastructure that holds your assets is the core mission of ShieldGuard Protocol. We are building the tools and ecosystem to ensure your Web3 journey is secure. Join our mission and participate in the ongoing $SHPRO public sale at ShieldGuard.io to help us build a safer future for everyone. 🛡️✨