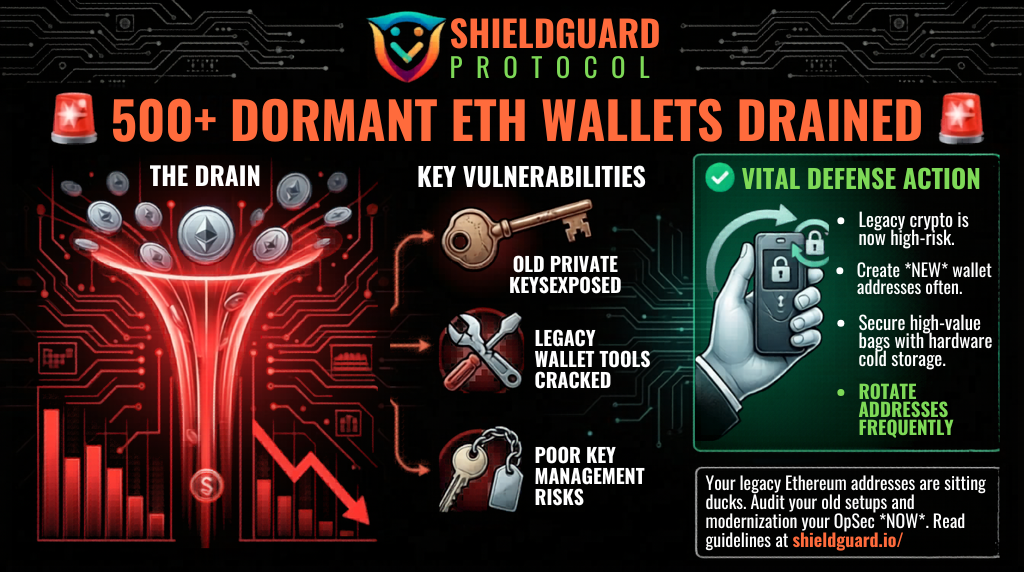
🚨 WALLET DRAIN ALERT: 500+ Dormant Ethereum Addresses Compromised
Category: Scam Alerts and Preventive Education
Threat Level: High 🔴
Target: Long-Term Holders, Early Ethereum Adopters, Legacy Wallet Users
The ShieldGuard Threat Intelligence team is issuing a critical warning regarding a massive, coordinated attack on legacy cryptocurrency wallets. If you are holding funds in an Ethereum address that was generated several years ago, your capital may be actively at risk.
Here is the complete intelligence breakdown of the dormant wallet drain and the operational security (OpSec) protocols you need to implement immediately.
🔍 Threat Intelligence: Anatomy of the Legacy Drain
Security researchers recently flagged a highly unusual and devastating attack pattern targeting old, quiet accounts. The attacker did not use fresh phishing links; instead, they targeted the foundational security of legacy wallets.
1. The Target: Forgotten Key Material
Hundreds of Ethereum wallets that had remained untouched for four to eight years were systematically drained. These were not hot wallets actively interacting with modern DeFi protocols; they were quiet accounts holding long-term investments.
2. The Execution: Centralizing the Stolen Funds
- The attacker compromised over 500 dormant wallets, resulting in collective losses of approximately $800,000.
- Over 260 ETH (worth roughly $600,000) was aggregated into a single Etherscan-labeled address known as
Fake_Phishing2831105. - To obscure the trail, 324.741 ETH was subsequently funneled through the THORChain Router v4.1.1.
3. The Vulnerability: Old Cryptography
While the exact compromise path remains unresolved, the evidence points strictly to historical vulnerabilities. This breach was likely caused by the exposure of old private keys, the cracking of legacy wallet generation tools, or poor key-management practices from an earlier era of Ethereum.
🛑 The Hard Truth: “Set and Forget” is Dangerous
A common misconception in Web3 is that an untouched wallet is a secure wallet. This incident proves that theory wrong.
Old Ethereum addresses—especially those generated years ago using outdated browser extensions, early legacy software, or obsolete key-generation mechanics—may contain underlying cryptographic vulnerabilities that modern hacking networks can now exploit at scale. If you are relying on a single private key that was generated years ago, you are trusting outdated armor to fight a modern war.
🛡️ Preventive Education: Securing Long-Term Wealth
To protect your capital against legacy exploits and long-tail key exposure, you must adopt an active defense strategy:
1. Rotate Your Addresses Frequently
Do not rely on a single legacy address indefinitely. We strongly advise users to rotate their holdings by creating new wallet addresses at frequent intervals using modern, audited, and secure generation methods. Retiring old private keys limits your exposure to historical vulnerabilities.
2. Upgrade to Hardware Cold Storage
When you rotate your addresses, move your high-value assets directly to a freshly generated address completely isolated on a modern hardware wallet. Hardware devices ensure your private keys are generated and stored offline, far away from internet-connected attack vectors.
3. Never “Test” Old Seed Phrases
If you are worried about an old wallet, do not type your old seed phrase into online checkers, scripts, or unfamiliar recovery tools. Doing so is a guaranteed way to hand your private keys directly to an attacker. Only use trusted, offline hardware environments to recover and transfer legacy funds.
💡 The ShieldGuard Verdict
The drain of 500+ dormant wallets is a massive wake-up call for diamond-hand investors. A system can look perfectly quiet while an old control failure waits in the background. Stop relying on the security standards of 2018 to protect your wealth in 2026. Audit your old setups, rotate your addresses, and modernize your defense.
Stay Verified. Stay Shielded.