🚨 MALWARE EXPLOIT ALERT: AI Platforms Weaponized to Distribute Crypto Stealers
Category: Scam Alerts and Preventive Education
Threat Level: High 🔴
Target: Web3 Developers, AI Enthusiasts, Desktop Wallet Users (Windows & macOS)
The ShieldGuard Threat Intelligence team is tracking a sophisticated new attack vector targeting the intersection of Web3 and Artificial Intelligence. Cybercriminals are actively weaponizing highly trusted AI distribution hubs to deploy devastating malware designed specifically to drain cryptocurrency wallets.
Here is the complete intelligence breakdown of the AI platform malware campaign and the critical operational security (OpSec) needed to protect your digital assets.
🔍 Threat Intelligence: Anatomy of the Attack
Threat actors have shifted their focus from standard phishing sites to hijacking the supply chain of open-source AI development.
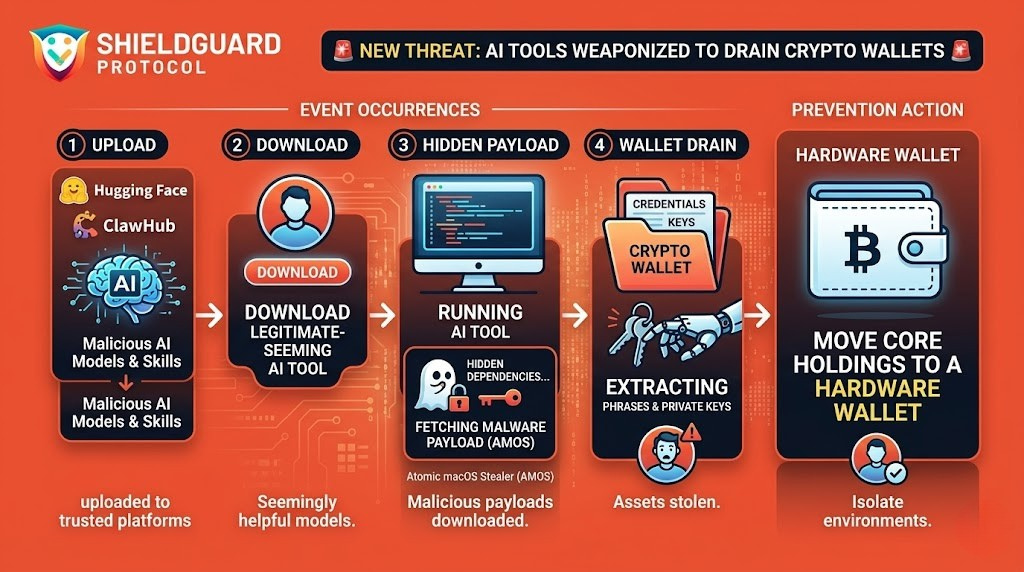
1. The Attack Vector: Trusted AI Hubs
Attackers are infiltrating popular AI collaborative platforms, specifically targeting Hugging Face and ClawHub. Because these platforms are widely trusted by developers and tech enthusiasts, users are far more likely to download files without executing their standard security checks.
2. The Execution: Social Engineering & Hidden Dependencies
The attackers do not rely on brute force; they rely on social engineering. They upload seemingly legitimate AI models, tools, or “skills.” However, these files contain hidden malicious code and compromised dependencies. On ClawHub alone, cybersecurity researchers recently identified nearly 600 malicious “skills” spread across 13 different developer accounts. When a user downloads and runs the AI tool, the malicious code quietly fetches its true payload in the background.
3. The Payload: The Atomic macOS Stealer (AMOS)
Once the hidden dependencies execute, they install severe malware payloads, including trojans and illicit cryptominers. Most critically for Web3 users, these payloads deploy specialized “info stealers” targeting both Windows and macOS operating systems.
A primary weapon in this campaign is the infamous Atomic macOS Stealer (AMOS). This malware is specifically engineered to hunt for, extract, and exfiltrate cryptocurrency wallet credentials, seed phrases, and private keys stored on the victim’s local machine.
🛑 The Hard Truth: Software Wallets Are Vulnerable
The rise of AI has created a massive rush to download and test new open-source models. Hackers are exploiting this gold rush. If you are using a desktop software wallet (like a browser extension or a local desktop app) on the same machine you use to download and run unverified third-party software, your entire portfolio is at risk.
Info stealers like AMOS bypass your passwords and 2FA by directly extracting the core wallet files from your computer’s directory. Once the malware is on your machine, your funds can be drained in seconds without you ever approving a transaction.
🛡️ Preventive Education: Securing Your Digital Environment
To protect your capital against supply-chain malware and advanced info stealers, you must implement strict compartmentalization:
1. Enforce Hardware Wallet Isolation
Never store significant crypto holdings on a software wallet (“hot wallet”) installed on your daily-use computer. Your core portfolio must be secured by an air-gapped hardware wallet. Even if an info stealer like AMOS infects your computer, it cannot extract the private keys stored offline inside a hardware device.
2. Sandbox Your AI Experiments
If you are downloading AI models, code repositories, or new software tools from platforms like Hugging Face or GitHub, do not run them on your primary machine containing sensitive financial data. Use an isolated virtual machine (VM) or a dedicated, separate device strictly for testing unverified code.
3. Audit Dependencies Before Execution
If you are a developer or power user, do not blindly execute installation commands (like npm install or pip install) from unknown repositories. Threat actors frequently use “typosquatting” or hidden commands in the documentation to install malware alongside the legitimate tool. Always verify the code and the publisher.
💡 The ShieldGuard Verdict
The weaponization of platforms like Hugging Face proves that threat actors are highly adaptable. As new technologies like AI emerge, scammers will immediately use them as a Trojan horse to target crypto wealth.
Protecting your portfolio requires constant vigilance and strict boundaries. Keep your investments isolated from your experimental software, rely on cold storage for your core assets, and never assume an open-source file is safe just because it is hosted on a popular platform.
Stay Verified. Stay Shielded.