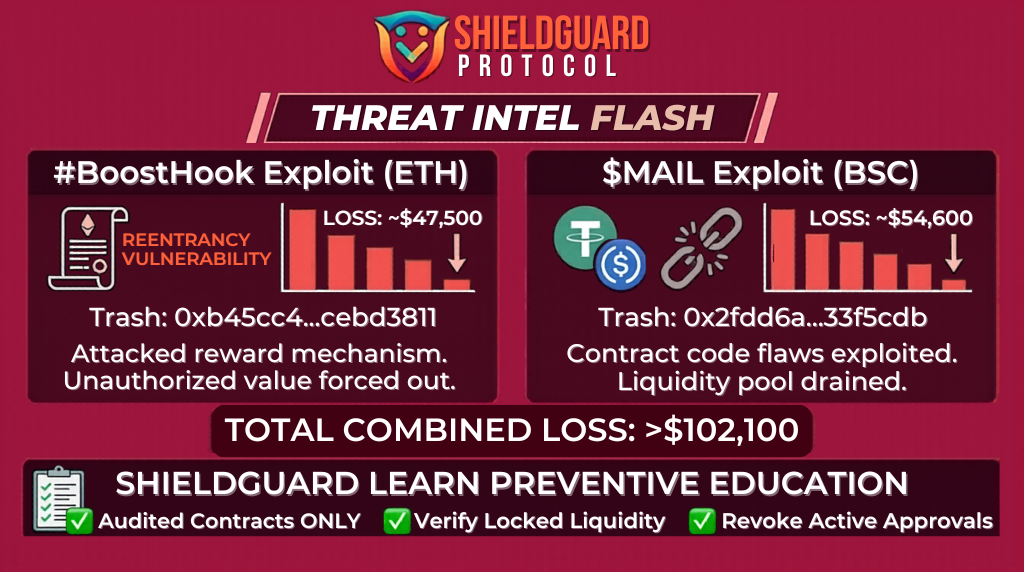
🚨 SHIELDGUARD THREAT INTEL: Contract-Level Exploits (BoostHook & MAIL)
Status: Exploit Confirmed
Total Loss: ~$102,100 Combined
Networks: Ethereum (ETH) & BNB Smart Chain (BSC)
🔍 Threat Analysis: What Happened?
Our intelligence team has deconstructed two distinct on-chain attacks targeting smaller token ecosystems. While the dollar amounts are lower than major protocol hacks, the tactics reveal a dangerous trend in Contract Logic Manipulation.
1. The BoostHook (ETH) Attack:
- Transaction:
0xb45cc4...cebd3811 - The Method: The attacker targeted a contract named BoostHook. This was likely a “Symmetry” or “Reentrancy” style vulnerability within the contract’s reward or hook mechanism. The attacker manipulated the contract to drain approximately $47,500 in value by forcing the contract to release funds it wasn’t supposed to.
2. The $MAIL (BSC) Exploit:
- Transaction:
0x2fdd6a...33f5cdb - The Method: This was an attack on the MAIL token liquidity. Attackers often exploit poorly written “burn” or “mint” functions in BSC tokens. In this case, the vulnerability allowed the attacker to extract $54,600 from the liquidity pool, effectively devaluing the token for all other holders.
🛡️ PREVENTIVE EDUCATION: The Forward Defense Mindset
These hacks weren’t “Social Engineering” scams; they were Smart Contract failures. To protect your capital from these “technical traps,” you must adopt the following defensive protocols:
1. The “Auditor’s Eye” Rule
Never provide liquidity or significant capital to a contract that hasn’t been audited by a top-tier security firm (like CertiK, OpenZeppelin, or PeckShield).
- Red Flag: If the project team says “Audit is coming soon,” your money is currently at 100% risk.
2. Liquidity Lock Verification
For tokens like $MAIL, always check if the developer’s liquidity is locked via a third-party service (like Unicrypt or PinkLock).
- The Risk: If liquidity is unlocked, a developer—or a hacker who gains access to the developer’s wallet—can “pull the rug” or manipulate the pool at any time.
3. Monitor “Approvals” and “Allowances”
If you interacted with these specific contracts (BoostHook or MAIL), your wallet may still have an active Approval granted to the malicious or compromised code.
- Action: Use a tool like Revoke.cash or the security dashboard in your Rabby Wallet to immediately revoke any permissions given to these contracts.
4. The Small-Cap Risk Framework
Recognize that “DeFi Gems” and small-cap tokens on BSC and ETH are high-reward but Extreme-Risk.
- Strategy: Only allocate “Play Money” to these projects. Your core wealth should remain in audited, battle-tested protocols that have survived years of attempted hacks.
🎓 The Goal of Sovereignty
Understanding how a contract fails is the first step toward true financial sovereignty. By mastering these fundamentals, you transform from a target into a hardened participant who can see the trap before it is sprung.
Verify Everything. Master the Foundations. Stay Shielded. 🛡️✨