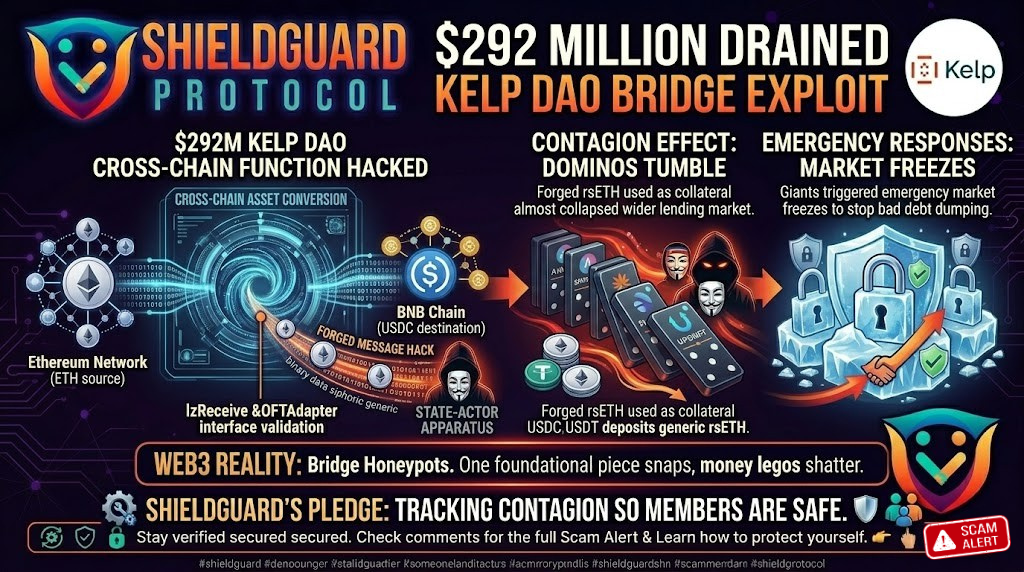
🚨 SECURITY ALERT: $292M DRAINED – The Kelp DAO Bridge Exploit & DeFi Contagion
Category: Cross-Chain Bridge Exploit / Smart Contract Vulnerability
Threat Level: Critical 🔴 (Largest DeFi Hack of 2026)
Total Loss: 116,500 rsETH (Approx. $292 Million)
The Web3 space has just witnessed the largest single DeFi exploit of 2026. Surpassing the devastating $285 million Drift Protocol hack from earlier this month, an attacker successfully compromised the Kelp DAO cross-chain bridge architecture, walking away with a staggering $292 million in liquid restaked Ethereum (rsETH).
The catastrophic fallout didn’t just hurt Kelp DAO; it triggered emergency market freezes across the biggest lending protocols in DeFi, including Aave, SparkLend, Fluid, and Upshift.
Here is the complete ShieldGuard Threat Intelligence breakdown of how the attacker forged their way into the vault, why this hack almost triggered a systemic collapse of the DeFi lending market, and how to protect your portfolio.
🏗️ The Target: Kelp DAO’s “Hub-and-Spoke” Architecture
To understand the hack, you have to understand how Kelp DAO moves money. Kelp issues rsETH, a Liquid Restaked Token (LRT). To allow users to trade rsETH across more than 20 different blockchain networks (Layer 2s), Kelp utilizes a “Hub-and-Spoke” model powered by the LayerZero messaging protocol.
- The Hub (Ethereum Mainnet): Holds the ultimate minting and redemption rights for real rsETH via a smart contract called the
OFTAdapter. - The Spokes (Layer 2s): Handle the standard “wrapped” versions.
- The Messenger: LayerZero acts as the communicator, telling the Mainnet Hub when to lock or release funds based on what happens on the Layer 2s.
⚙️ The Attack Mechanics: Forging the Message
On April 19, 2026, around 1:35 AM, a highly sophisticated attacker (funded 10 hours prior via Tornado Cash) executed a masterclass in cross-chain manipulation.
1. The Vulnerability Exploited: The attacker targeted the lzReceive function within the LayerZero EndpointV2 contract.
2. The Forgery:
Instead of actually depositing funds on a Layer 2 network, the attacker managed to successfully forge a cross-chain message. They tricked the LayerZero endpoint into confirming a massive, non-existent deposit.
3. The Drain:
The forged message hit the Ethereum Mainnet OFTAdapter. Believing the message was legitimate, the Adapter unlocked and released 116,500 rsETH directly to the attacker’s wallet. In a single transaction, the attacker drained 18% of the entire circulating supply of rsETH.
🛑 The Containment: The $100M Save
Approximately 46 minutes after the initial drain, the Kelp DAO team detected the anomaly and triggered an emergency multi-sig pauseAll function. This froze the entire system: the LRT Deposit Pool, the Withdrawal contracts, the Oracle, and the rsETH token contract itself.
This rapid response saved the protocol from total annihilation. On-chain forensics show the attacker attempted two subsequent transactions to drain an additional 40,000 rsETH each (another $100+ million), but the network freeze caused both transactions to fail.
🦠 The Contagion: Why Aave & SparkLend Hit the Brakes
The true danger of this exploit was not just the theft; it was the contagion effect.
In DeFi, rsETH is heavily utilized as “high-quality collateral” to borrow other assets on major lending platforms. When the hacker minted $292 million in fake-backed rsETH, they gained the ability to deposit that stolen rsETH into platforms like Aave and borrow real USDC, USDT, and standard ETH against it.
Realizing the attacker was holding millions in compromised collateral, Aave (V3 and V4), SparkLend, Fluid, and Upshift triggered emergency market freezes on their rsETH pools to prevent the hacker from offloading the bad debt onto their protocols.
🛡️ Preventive Education: Surviving Bridge Exploits & DeFi Contagion
When a $292 million bridge collapses, the everyday user cannot step in and patch the smart contract. However, you have absolute control over your risk exposure. This exploit proves that the “money legos” of DeFi can shatter if one foundational piece is compromised.
Here is your OpSec survival guide for navigating cross-chain bridges and Liquid Restaked Tokens (LRTs):
1. Prioritize Native Assets Over Bridged Tokens
Every time an asset crosses a bridge, it inherits a massive layer of smart contract risk. Holding native ETH on the Ethereum Mainnet is fundamentally safer than holding a wrapped, bridged, or restaked derivative of ETH on a Layer 2 network. If you are holding bridged tokens long-term, you are betting your money that the bridge’s code will never break.
2. Beware the “Contagion Risk” in Lending
DeFi protocols are deeply interconnected. As we saw today, a hack on Kelp DAO almost triggered a crisis on Aave and SparkLend. If you are using LRTs (like rsETH) as collateral to borrow stables or other assets, a protocol-level hack will cause your collateral to crash to zero, triggering an immediate liquidation of your position. Never use highly complex, bridged tokens as your primary collateral for borrowing.
3. Isolate Your Vaults (Diversification)
Do not put your entire net worth into a single yield-farming strategy or a single bridge ecosystem. If you are chasing high APY in the restaking narrative, restrict it to a completely isolated wallet containing only the funds you are willing to risk on experimental smart contracts.
4. Monitor the Emergency Brakes
When major lending protocols like Aave or Fluid suddenly hit the “Pause” button on a specific asset, it is the ultimate red flag. This is why staying plugged into real-time threat intelligence is non-negotiable. If you see the ecosystem freezing a token, do not try to “buy the dip” on a decentralized exchange—get out of the blast radius.
💡 The ShieldGuard Verdict
The Kelp DAO exploit is a brutal reminder of the core vulnerability in modern DeFi: Interoperability relies on absolute truth. When bridges can be manipulated into broadcasting “fake news” to mainnet vaults, the entire house of cards collapses.
Cross-chain bridges remain the single biggest target for elite hackers because they hold the largest honeypots of liquidity. We are actively tracking the fallout of this exploit and its impact on the wider lending ecosystem to ensure our community never gets caught in the contagion.
Take control of your risk exposure today. Join the ShieldGuard Protocol ecosystem, access our premium ShieldGuard Learn modules, and let our threat intelligence team watch your back.
Stay Verified. Stay Shielded.