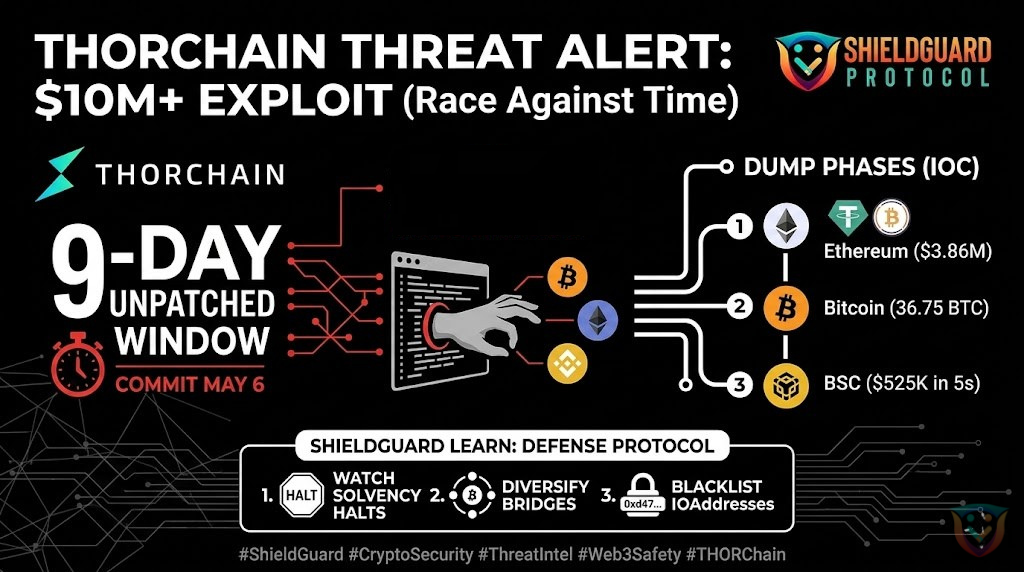
🚨 SHIELDGUARD THREAT INTEL: THORChain $10M+ Cross-Chain Exploit
Status: Exploit Confirmed / Network Halted
Total Loss: ~$10,200,000+
Networks Impacted: Bitcoin (BTC), Ethereum (ETH), BNB Chain (BSC), Base, Avalanche (AVAX)
🔍 Threat Analysis: What Happened?
Our intelligence team has analyzed the multi-chain drain of THORChain. This was a highly technical exploit targeting the core communication layer between different blockchains.
1. The Root Cause: Proposer-Forgery Bug
The vulnerability existed in the Bifrost Attestation Gossip protocol. Specifically, validator signatures did not cover the “inbound/outbound” bit of a transaction. This allowed a malicious proposer to intercept a legitimate observation of funds coming in and “flip” it into a forged command to send funds out to their own wallet.
2. The Execution (Drain Phases):
The attacker moved with extreme speed across multiple chains:
- Ethereum: Drained ~$3.86M in assets (USDT, USDC, WBTC, LINK) in just 30 minutes.
- BSC: Drained ~$525K in a single 5-second burst.
- Bitcoin: Extracted ~36.75 BTC.
3. The Tragic Timing:
A patch for this exact bug (commit af46db22) was authored on May 6th—9 days before the attack. However, due to a CI pipeline failure, the fix was not shipped to validators in time, leaving a 9-day window for the exploiter to strike.
🛡️ PREVENTIVE EDUCATION: The Forward Defense Mindset
This exploit highlights the unique risks of Cross-Chain Interoperability. When you move assets between chains, you are relying on the security of the “bridge” logic.
1. The “Protocol Health” Monitor
In decentralized finance, security is a moving target.
- Defense: Before committing large liquidity to a cross-chain protocol, check the project’s recent GitHub activity or developer “commits.” If you see critical security patches being discussed but not yet “merged” or “deployed,” reduce your exposure immediately.
2. Recognizing “Mimir” and Solvency Halts
THORChain stayed somewhat protected because of its Auto-Solvency Halt feature. This is a “Circuit Breaker” that stops the network if it detects more money leaving than coming in.
- Action: If you see a protocol “Halt Trading” or “Pause Signing,” do not attempt to force transactions through. These are emergency defensive measures designed to save the remaining 90% of user funds.
3. Cold Wallet Awareness (IOCs)
The attacker is currently holding over 3,156 ETH (~$7.1M) in a specific “Cold Wallet.”
- Action: Blacklist and monitor the following addresses in your own tracking tools. Never interact with funds originating from these sources:
- ETH/Base:
0xd477b695...8890Bd - BTC:
bc1ql4u94k...jhf6f37
4. The Bridge Risk Framework
Cross-chain protocols are the “Honey Pots” of Web3. They hold massive amounts of locked collateral.
- Rule: Never keep 100% of your assets in a single bridge or cross-chain provider. Diversify your holdings across native chains to ensure a single protocol bug doesn’t result in a total loss of your portfolio.
🎓 Sovereignty Through Awareness
Even “battle-tested” protocols like THORChain can fall victim to deployment delays. True sovereignty means realizing that code is law, but humans deploy the code. By staying informed on “Known but Unpatched” vulnerabilities, you put yourself ahead of the exploiters.
Be in a shielded environment for safe crypto growth.
ShieldGuard Protocol is your digital fortress against scams, built to empower investors and provide a foundation for the future of digital assets. $SHPRO is more than a token—it is your access key to an exclusive, secure ecosystem designed to eliminate fraud and provide passive income.
No more crypto scams. Join the Shielded movement. 🛡️
Verify Everything. Master the Foundations. Stay Shielded. 🛡️✨