🚨 SCAM ALERT: The Deceptive Evolution of DeFi & Cross-Chain Bridge Exploits
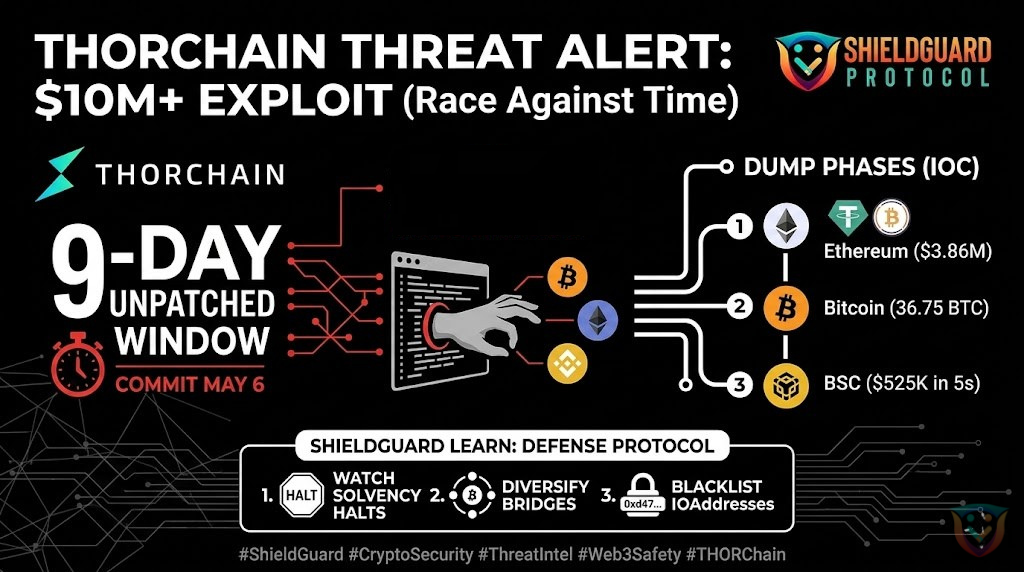
The Decentralized Finance (DeFi) and cross-chain bridge ecosystem is experiencing a massive wave of high-impact security breaches. Hackers are shifting away from basic coding blunders and deploying highly coordinated, long-term operational campaigns to drain protocol liquidity pools.
Our internal threat research team at ShieldGuard Protocol has been actively auditing and testing code structures across both prominent and emerging DeFi applications. The patterns we are uncovering confirm a dangerous trend: structural design vulnerabilities and off-chain infrastructure flaws are leaving billions of dollars exposed. With major protocol losses mounting rapidly, we urge all Web3 investors, liquidity providers, and project founders to exercise extreme caution when interacting with cross-chain routing systems.
🔍 Anatomy of Modern DeFi Exploits: The 2026 Attack Vectors
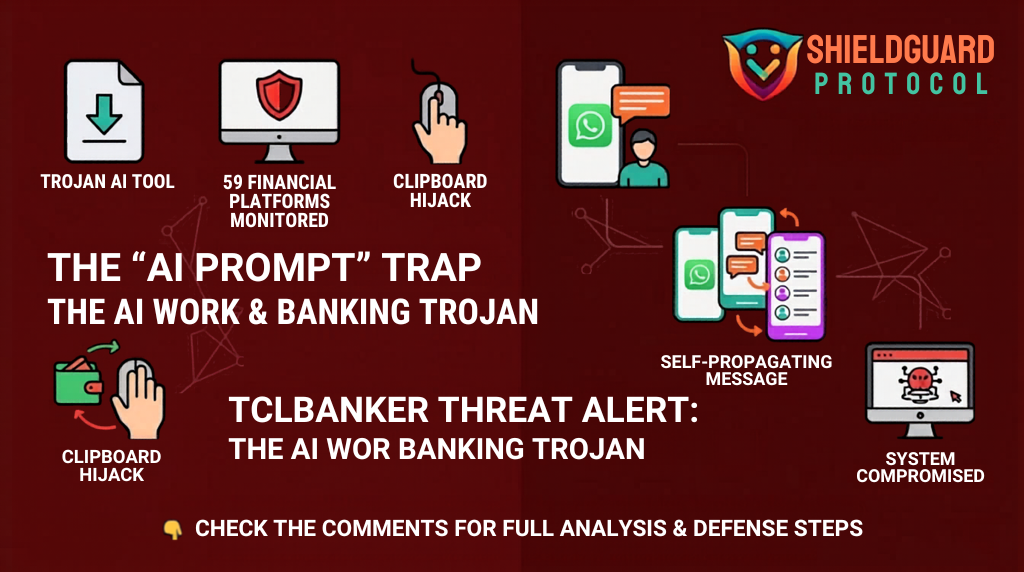
While traditional smart contract bugs (like reentrancy or integer overflows) still occur, the largest heists are successfully bypassing standard code audits altogether. Attackers are aggressively targeting the governance, infrastructure, and messaging layers that connect blockchains.
1. RPC Node Poisoning & Interception
Cross-chain bridges rely on Remote Procedure Call (RPC) nodes to transmit messages (such as deposit and withdrawal confirmations) between separate blockchains. If a protocol utilizes a single-path configuration or lacks node redundancy, it creates a fatal single point of failure.
- The Mechanism: Attackers gain unauthorized access to a protocol’s RPC server list. They launch distributed denial-of-service (DDoS) attacks to take clean, legitimate nodes offline, forcing the network to route traffic through a malicious node they control. This allows them to inject fraudulent cross-chain messages, creating unbacked tokens out of thin air to drain decentralized lending pools.
2. Advanced Multi-Sig & Social Engineering Sagas
Instead of looking for errors in automated immutable code, syndicates are spending months executing deep social engineering pipelines to compromise protocol signers and deployer private keys.
- The Mechanism: Operatives embed themselves within the Web3 community—sometimes posing as legitimate venture funds or quantitative trading desks, and depositing large amounts of capital to build long-term institutional trust. Once inside, they deploy targeted malware via shared repositories or developer testing applications to harvest administrative private keys, executing total vault drains in a matter of minutes.
3. Decentralized Oracle Manipulation
Protocols that rely heavily on automated market makers (AMMs) for real-time asset pricing remain vulnerable to sudden oracle manipulation.
- The Mechanism: Attackers execute highly precise trades or employ flash loans to artificially inflate the apparent value of a low-liquidity token asset. By tricking the protocol’s price feed oracle into recognizing the inflated value as valid collateral, they can borrow millions against worthless tokens, leaving the underlying lending platform with catastrophic, unrecoverable bad debt.
🛡️ Defensive Blueprint: How Investors Can Stay Safe
As we navigate a high-risk landscape with further protocol exploits anticipated in the near term, protecting your capital requires moving beyond a “set-and-forget” mentality. Implement these defensive steps immediately:
- Audit the Infrastructure, Not Just the Code: Before depositing assets into a liquidity pool or staking via a cross-chain aggregator, verify if the protocol has a strict, multi-signature timelock (at least 48 hours) on contract upgrades. If a platform can change its core logic instantly with zero delay, an attacker holding a compromised deployer key can lock everyone out.
- Diversify Your Bridge Allocations: Avoid funneling massive amounts of capital through a single bridge hub. Focus on using bridges that utilize decentralized validator sets, multi-path messaging redundancy, and active mempool front-running protections to isolate malicious traffic.
- Segregate Your Assets via Cold Storage: Never interact with experimental or high-yield DeFi platforms using your primary storage or governance wallets. Utilize clean, independent hardware wallets that have completely isolated approval histories to prevent an accidental contract interaction from compromising your entire portfolio.
- Track Real-Time Token Velocity: Sudden, massive outflows or anomalous spikes in the minting patterns of a specific wrapped asset are often the earliest on-chain signals of an ongoing exploit. Pay close attention to real-time security alert feeds to pull your assets before liquidity pools run dry.
📢 Community Notice
If you are tracking a suspicious transaction pattern or want our team to review a protocol’s public deployment, connect with us on our official communications channels. Stay alert, preserve your capital, and let’s build a secure Web3 perimeter together.