🚨 SECURITY ALERT: The $7.6M Rhea Finance Exploit & The Danger of Oracle Manipulation
Category: DeFi Security / Smart Contract Exploit
Threat Level: Critical 🔴
Target: DeFi Liquidity Providers, NEAR Protocol Users, and Yield Farmers.
At ShieldGuard Protocol, we constantly track the evolving tactics of threat actors to ensure our community stays untouchable. While phishing and social engineering grab the headlines, the foundational layers of decentralized finance (DeFi) are under relentless attack from highly technical smart contract exploits.
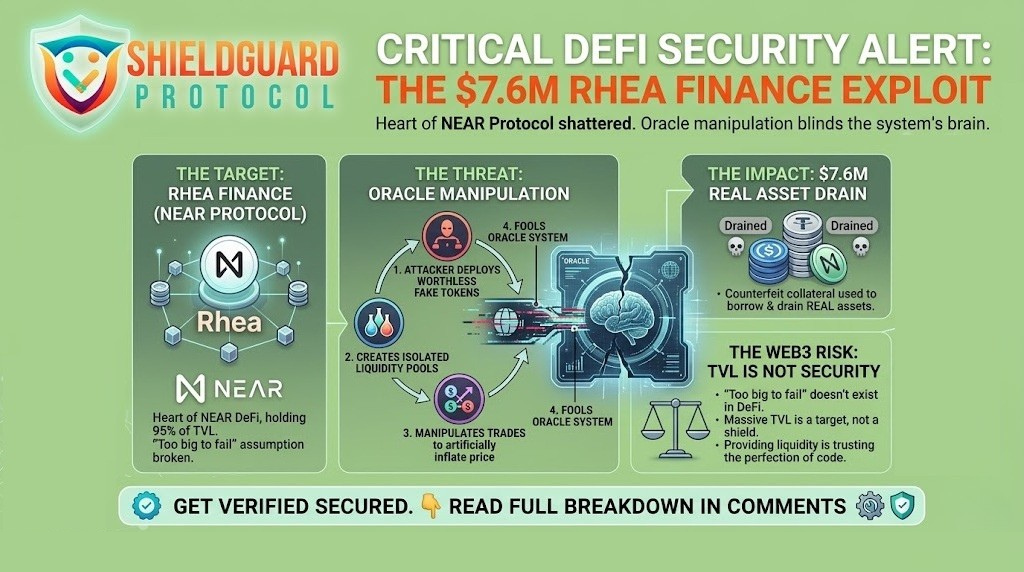
The recent $7.6 million drain of Rhea Finance—the absolute center of the NEAR Protocol ecosystem holding over 95% of its Total Value Locked (TVL)—is a catastrophic reminder that in Web3, a protocol is only as secure as the data feeding it.
Here is the exact breakdown of how this massive oracle manipulation attack unfolded, and the critical OpSec strategies you need to survive in the DeFi landscape.
🔍 The Threat Vector: Blinding the Oracle
This was not a case of stolen passwords or compromised private keys. The attacker weaponized the protocol’s own pricing mechanism against it through a method known as Oracle Manipulation.
Smart contracts cannot inherently know the real-world price of an asset; they rely on “Oracles” (data feeds) to tell them. If you can trick the Oracle, you can trick the protocol into giving you free money.
The Anatomy of the Hack:
- The Forgery: The attacker deployed fraudulent, custom-made token contracts onto the NEAR blockchain. These tokens had absolutely zero real-world value.
- The Illusion of Liquidity: They created fresh, isolated liquidity pools on Rhea Finance pairing these fake tokens with real assets.
- The Manipulation: By executing highly calculated trades within these thin, newly created pools, the attacker artificially inflated the price of their fake tokens. The protocol’s Oracle looked at this pool and was tricked into believing the fake tokens were highly valuable.
- The Drain: The attacker deposited their now “valuable” fake tokens as collateral into Rhea’s lending contracts. Because the protocol was blinded by the manipulated Oracle, it allowed the attacker to borrow $7.6 million in real assets (USDC, USDT, Zcash, and NEAR). The attacker walked away, leaving the protocol with worthless forged tokens.
(Note: In a rare centralized intervention, Tether was able to freeze approximately 3.29 million of the stolen USDT, but the structural damage to the protocol was already done).
🛡️ Preventive Education: Navigating DeFi Protocol Risks
When a flagship protocol gets drained, it proves a harsh reality: providing liquidity means you are trusting the absolute perfection of the protocol’s code. When the code breaks, it is the users’ liquidity that pays the price.
To protect your portfolio from protocol-level exploits, you must upgrade your risk management daily.
1. TVL is Not a Security Metric
Do not assume a protocol is “too big to fail” just because it has hundreds of millions in Total Value Locked. Rhea Finance held 95% of NEAR’s DeFi TVL and was still shattered by a single manipulated data feed. High TVL attracts highly skilled predators.
2. Scrutinize Oracle Dependencies
Before depositing significant capital into a lending protocol, check its documentation. Does it rely on a single, easily manipulated liquidity pool for its price feeds, or does it use decentralized, robust oracle networks like Chainlink that aggregate data from multiple premium sources?
3. The Danger of “Isolated” or “Permissionless” Pools
Protocols that allow anyone to spin up a new liquidity pool and immediately use those assets as collateral are extreme high-risk environments. The lack of vetting is exactly what allows attackers to introduce fake tokens into the ecosystem.
4. Diversification is Your Ultimate Hedge
Never park your entire portfolio in a single yield-farming protocol, regardless of the promised APY. If a smart contract glitch occurs, your exposure should be limited to a fraction of your net worth.
💡 The ShieldGuard Verdict
The scammers are finding new ways every day to prepare new attacks, and your today’s knowledge cannot protect your tomorrow. The Rhea Finance exploit shows that the predators aren’t just targeting individuals; they are targeting the bank vaults of the blockchain itself.
We are tracking these vulnerabilities so our ecosystem members are never caught off guard. Middle finger to the scammers—we see your tactics, we are dissecting your exploits, and we are destroying your traps through relentless education.
If you are too busy to monitor these technical threats yourself, join the ShieldGuard Protocol ecosystem today. Access our ShieldGuard Learn modules and let our threat intelligence team watch your back.
Stay Verified. Stay Shielded.