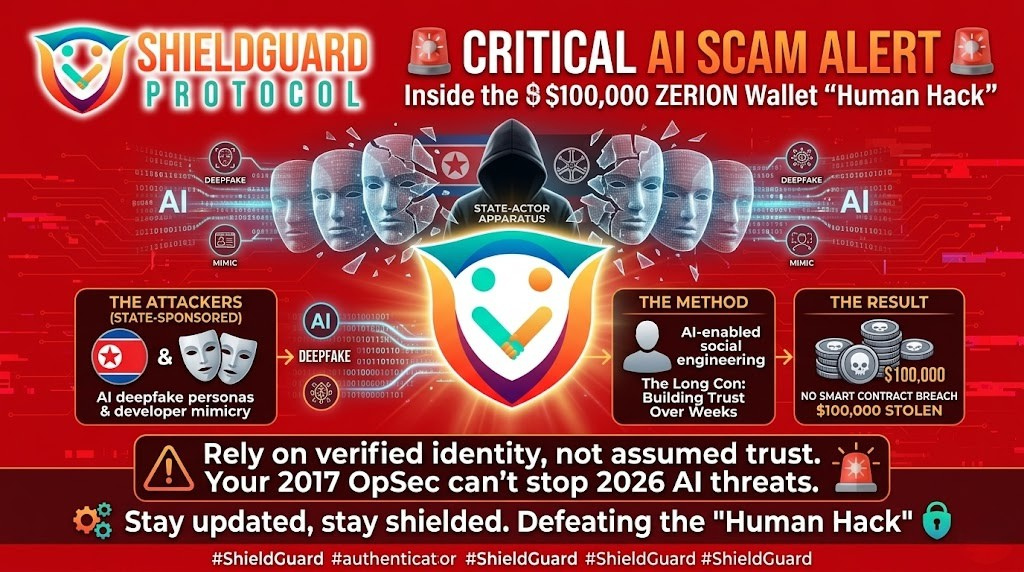
🚨 SECURITY ALERT: The AI-Powered “Human Hack” – Inside the Zerion Wallet Exploit
Category: Social Engineering / AI Threats
Threat Level: High 🔴
Target: Web3 Core Teams, Developers, Partners, and High-Net-Worth Individuals.
At ShieldGuard Protocol, we spend a vast amount of time analyzing smart contract vulnerabilities, malware, and code-level exploits. However, the most dangerous vulnerability in the Web3 ecosystem isn’t written in Solidity—it is human psychology.
We are currently tracking a severe escalation in what we call the “Human Hack.” Security researchers have confirmed that highly organized North Korean hacking syndicates successfully exploited the Zerion wallet ecosystem for approximately $100,000.
Crucially, this was not a smart contract failure or a technical breach. It was a masterclass in AI-enabled social engineering. Here is how the landscape of digital deception is evolving and the OpSec required to defend against it.
🔍 The Threat Vector: Weaponized Artificial Intelligence
In the past, social engineering in crypto looked like obvious phishing emails or poor-grammar DMs from “customer support.” The Zerion exploit proves those days are over.
The attackers utilized a highly sophisticated, long-running infiltration campaign powered by generative AI.
- Deepfake Personas: Attackers used AI to generate realistic profile images, video content, and audio to fabricate entire identities.
- Contextual Impersonation: Using AI language models, the hackers generated highly convincing, context-aware messages to flawlessly mimic the tone and technical jargon of legitimate developers and business partners.
- The “Long Con”: This was not a quick smash-and-grab. The attackers spent weeks—or even months—building genuine rapport and trust with the victims before finally introducing the malicious payload or extracting funds.
💥 The Takeaway: Trust is the New Attack Surface
When hackers use artificial intelligence to build long-term trust, they successfully bypass every traditional technical security layer you have in place. It does not matter if your smart contracts are audited by Coinsult or if your assets are behind a hardware wallet; if an attacker can socially engineer you into willingly handing over the keys or authorizing a transaction, the technical barriers become useless.
The scammers are finding new ways every day to prepare new attacks. This incident is a glaring reminder that your knowledge from yesterday cannot protect your assets tomorrow.
🛡️ Preventive Education: Defending Against the AI “Human Hack”
To survive in an ecosystem where video, audio, and text can be perfectly spoofed, you must adopt a strict Zero-Trust Identity Framework.
1. Implement Multi-Channel Verification
Never trust a single point of communication. If a “partner” or “developer” makes a sensitive request via Telegram or Discord, force a verification step through a completely separate, established channel (e.g., an official company email or a public X account).
2. Beware the “Long Con” Urgency
AI social engineering relies on building a long-term relationship, only to suddenly introduce an “urgent” or “time-sensitive” crisis that requires immediate financial or technical action. The moment a long-term contact creates artificial urgency, treat the entire relationship as compromised until verified.
3. Cryptographic Proof Over Visual Proof
In a world of deepfakes, seeing is no longer believing. For high-level partnerships, OTC deals, or protocol-level access, do not rely on video calls for identity verification. Require cryptographic proof, such as signing a message with a known, public wallet address or using PGP keys.
4. Continuous Team Education
Your project is only as secure as your most trusting team member. Ensure everyone in your organization understands that AI can now perfectly mimic the CEO, the lead developer, or your top investor.
💡 The ShieldGuard Verdict
The Zerion exploit is a warning shot for the entire Web3 space. Being educated in 2017 crypto tactics will not save you from 2026 AI-driven attacks. If you assume you are too smart to be socially engineered, you are exactly the type of target these state-sponsored groups are looking for.
Stay updated, implement Zero-Trust verification, and let the ShieldGuard Protocol ecosystem keep you one step ahead of the predators.
Stay Verified. Stay Shielded.