🚨 SECURITY ALERT: The Hyperbridge Cross-Chain Exploit & Fake Token Minting
Category: DeFi Security / Smart Contract Exploit
Threat Level: High 🔴
Target: Cross-Chain Bridge Users, Liquidity Providers (LPs), and Token Holders.
At ShieldGuard Protocol, we constantly emphasize that the Web3 frontier requires daily vigilance. While user-targeted scams (like phishing and malware) are rampant, protocol-level vulnerabilities pose massive systemic risks. Today, we are dissecting a critical vulnerability exposed in the Hyperbridge cross-chain protocol that resulted in a billion-dollar “paper” exploit.
Here is exactly what happened, the mechanics of the attack, and the OpSec strategies you need to navigate decentralized finance safely.
🔍 What is the Hyperbridge Exploit?
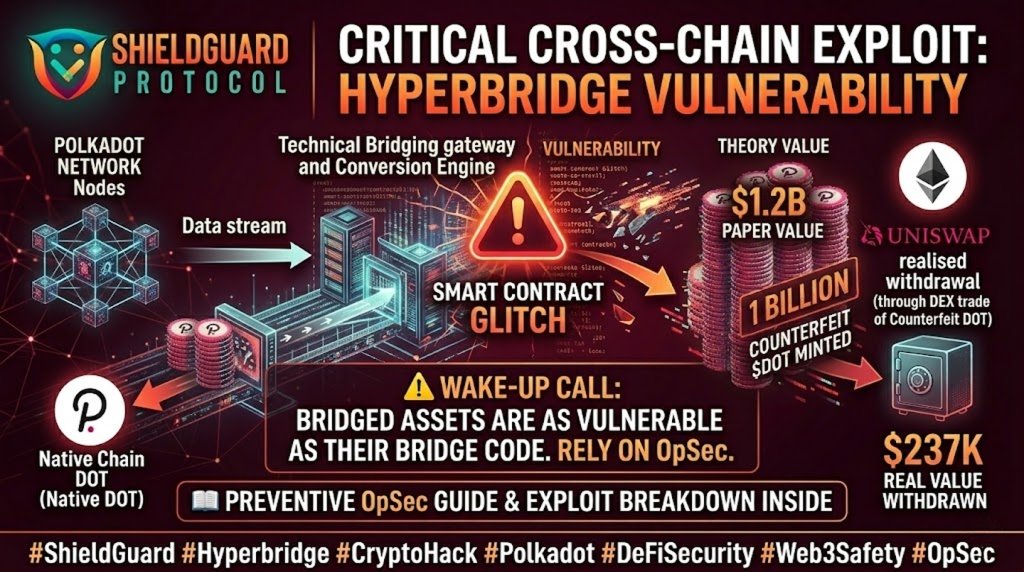
Hackers successfully exploited a severe code vulnerability within the Ethereum Token Gateway of Hyperbridge, a popular protocol designed to move assets between different blockchains.
Instead of stealing existing user funds directly, the attacker found a flaw in the bridge’s smart contract logic that allowed them to unilaterally “print” money.
⚙️ How the Attack Unfolded
This exploit highlights the inherent risks of cross-chain infrastructure:
- The Breach: The attacker targeted a vulnerability in the gateway’s validation process.
- The Counterfeit Mint: Bypassing security checks, the hacker tricked the bridge contract into minting an astronomical 1 billion counterfeit Polkadot (DOT) tokens directly onto the Ethereum blockchain.
- The Illusory Value: At current market rates, this massive supply of fake wrapped DOT carried a staggering “paper value” of $1.2 billion.
💥 The DEX Dump: Why it Wasn’t a Billion-Dollar Loss
You might wonder why the hacker didn’t walk away a billionaire. The answer lies in the mechanics of Decentralized Exchanges (DEXs) like Uniswap.
- The Liquidity Bottleneck: To convert fake tokens into real money (like ETH or stablecoins), the hacker had to sell them into existing Liquidity Pools on Uniswap.
- The Reality Check: There was simply not enough real liquidity in the DOT/ETH pools to absorb 1 billion tokens. As the hacker dumped the fake tokens, the price of the bridged asset immediately crashed to zero.
- The Final Tally: The attacker managed to siphon approximately $237,000 of real value from the liquidity pools before the Hyperbridge developer team detected the anomaly and hit the “pause” button on the protocol.
🛡️ ShieldGuard Preventive Defense: Navigating Bridge Risks
While protocol-level hacks are the fault of flawed code, your defense strategy must account for these inevitable Web3 realities.
1. Limit Exposure to “Wrapped” Assets
Bridged assets (like DOT on Ethereum or BTC on Solana) are only as secure as the bridge that holds the real assets backing them.
- Action: Whenever possible, hold the native asset on its native blockchain. Use bridges only for transit, not for long-term storage.
2. Revoke Unlimited Approvals
If a bridge contract you have interacted with is compromised, attackers can sometimes drain assets you previously approved.
- Action: Regularly use tools to audit your wallet and revoke token approvals for bridges and DEXs you are no longer actively using.
3. Understand Impermanent Loss & Pool Exploits
If you are a Liquidity Provider (LP), understand that if one asset in your pool gets artificially hyper-inflated (like the fake DOT), the automated market maker (AMM) will trade away all your valuable assets (like ETH) for the worthless fake tokens.
- Action: Only provide liquidity to battle-tested pools, and set up alerts for sudden, extreme price deviations.
💡 The ShieldGuard Verdict
The Hyperbridge incident is a textbook example of why code audits and continuous threat intelligence are non-negotiable in crypto. A $1.2 billion glitch was mitigated down to a $237,000 loss only by the physical constraints of DEX liquidity and a rapid protocol pause.
In the crypto ecosystem, assuming any smart contract is 100% impenetrable is a dangerous game. Your best defense is a diversified strategy, minimizing third-party contract exposure, and staying educated.
Stay Verified. Stay Updated. Stay Safe.