🚨 THREAT ALERT: The “Synthetic Trust” Exploit & The Illusion of Decentralized Escrow
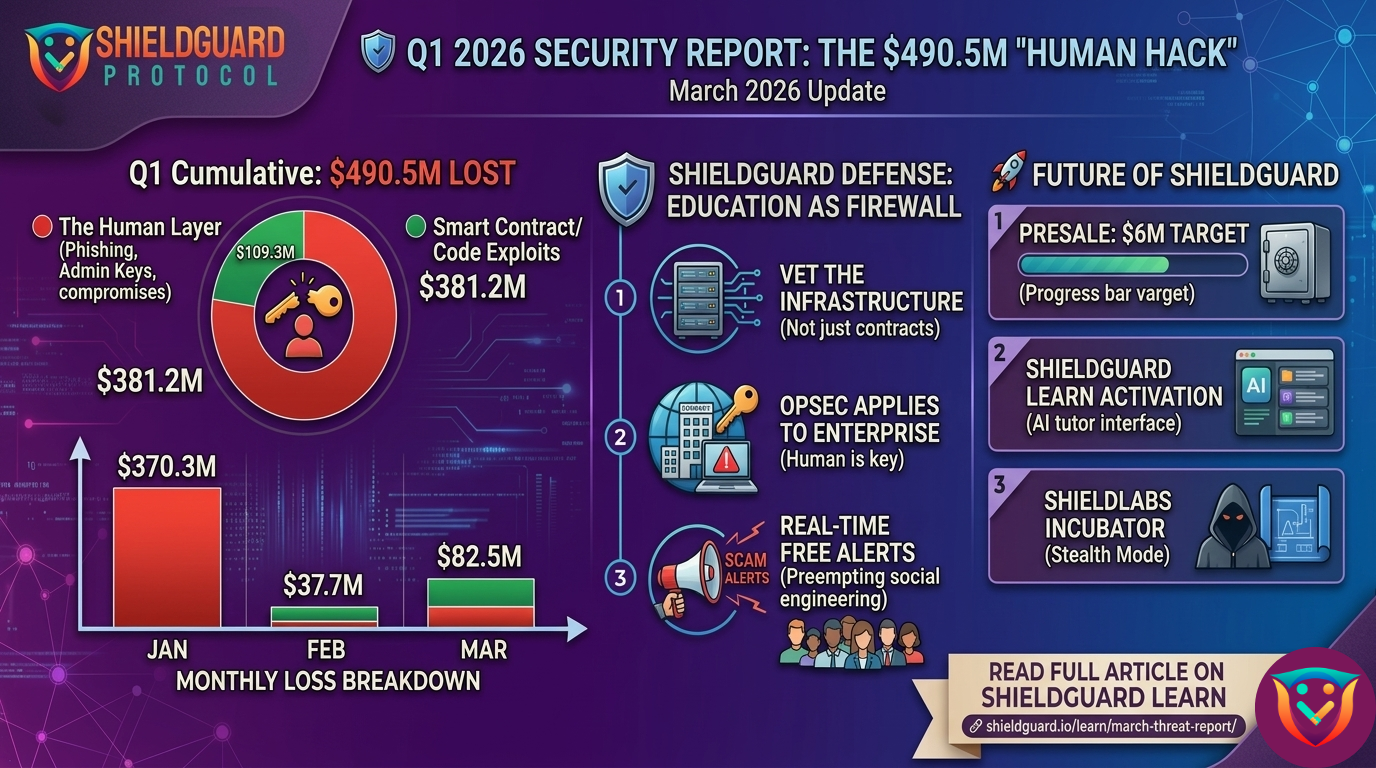
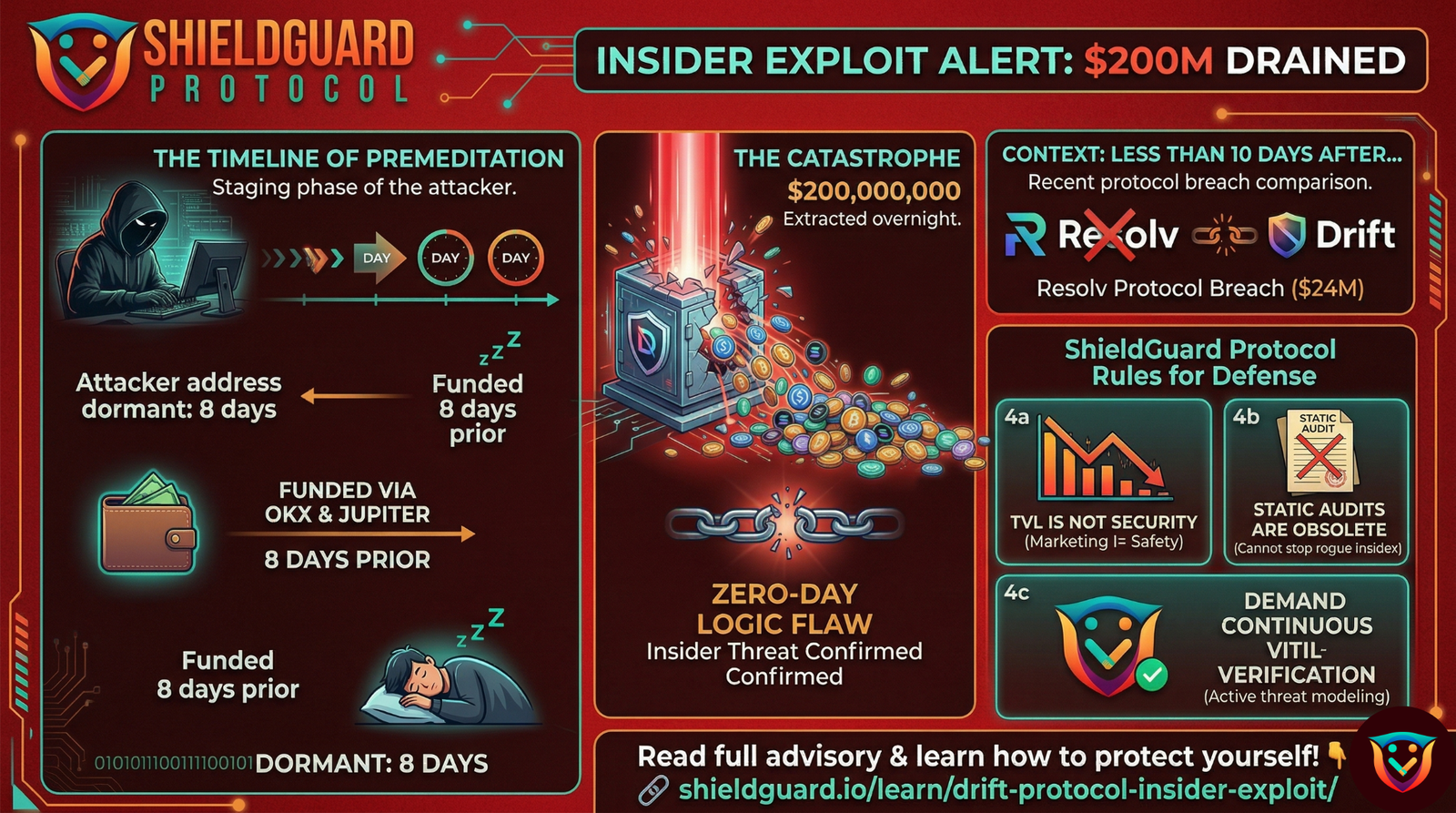
The most devastating exploits in Web3 do not always require million-dollar zero-day flaws or complex flash-loan attacks. A massive segment of stolen capital is drained through pure psychological manipulation. Threat syndicates are industrializing social engineering, using what we call the “Synthetic Trust” exploit to bypass logical skepticism and drain retail wallets directly.
Here is a breakdown of how these sophisticated, multi-layered social engineering traps work in the wild, and the operational security (OpSec) rules you need to defend yourself.
The Anatomy of the Attack: Realistic Threat Scenarios
The core of this exploit is manufacturing a fake environment where the victim feels secure. Attackers prey on the desire for discounted assets, exclusive allocations, or peer-to-peer (P2P) trades, pulling users into tightly controlled environments like Telegram or Discord.
Scenario A: The “Verified” P2P Middleman Trap A user wants to execute an over-the-counter (OTC) trade—perhaps buying discounted stablecoins, gift cards, or pre-sale allocations. To “ensure safety,” the seller insists on using a trusted community middleman or escrow agent.
- The Setup: The user is invited to a Telegram group boasting 10,000+ members. The channel is flooded with daily “vouches,” screenshots of successful trades, and positive reviews praising the middleman.
- The Trap: A 3-way chat is created. The “middleman” acts highly professional, laying out the terms. The victim feels secure because of the overwhelming social proof.
- The Execution: The victim transfers the cryptocurrency to the escrow wallet. Immediately, the seller and the middleman delete their accounts and wipe the chat history.
Scenario B: The “Alpha Group” Admin Spoof Users in a legitimate crypto community are direct-messaged by an account that looks exactly like the group’s founder or lead developer (copied profile picture, slightly altered username).
- The Setup: The fake admin offers to act as a secure bridge for a highly anticipated, “invite-only” token round, bypassing network congestion.
- The Trap: The attacker points to the public trust the real admin has built. They provide a wallet address for a direct, “gas-free” OTC allocation.
- The Execution: The user sends funds, assuming they are dealing with a known entity. The crypto is instantly routed through a mixer, and the user is blocked.
The Mechanics of the Trap: Why the “Human Hack” Works
These syndicates rely on three specific psychological overrides:
1. Synthetic Social Proof (The Bot Farm Illusion) Humans are wired to trust the herd. Scammers know this. 10,000 group members and hundreds of positive “vouches” are completely fabricated. Bot farms are incredibly cheap; an attacker can populate a channel and generate an endless loop of fake transactional praise in minutes, creating a powerful illusion of legitimacy.
2. The Manufactured Authority By introducing an “impartial” third party (the middleman) or impersonating a figure of authority (the admin), the attacker removes the friction of a direct 1-on-1 transaction. The victim lets their guard down, believing an established entity is overseeing the deal. In reality, a single attacker often controls the seller, the buyer, the escrow, and the bots.
3. The Point of No Return (Crypto Finality) These traps are designed specifically to end in a cryptocurrency transfer. Traditional bank transfers or credit cards offer fraud protection and chargebacks. By convincing the user to settle the transaction on-chain, the attacker ensures the execution is cryptographically final. Once the blockchain confirms the transaction, centralized banks cannot intervene.
🛡️ The ShieldGuard Defense: Building Your Human Firewall
Software and smart contract audits cannot protect you if you willingly hand over the keys. To immunize yourself against Synthetic Trust exploits, you must adopt these strict OpSec rules:
- Rule #1: Telegram/Discord “Vouches” Are Mathematically Worthless. Never trust follower counts, screenshots of successful trades, or comment sections in messaging apps. Assume every metric and review in an unverified group is automated by scripts. Social proof on anonymous platforms is a red flag, not a safety net.
- Rule #2: Reject Unofficial Escrow & P2P Middlemen. Never use a human middleman on Telegram, X, or Discord. If a transaction requires escrow, it must be executed through a legally compliant, centralized exchange (like Binance or Kraken P2P) or a verified, audited smart contract designed strictly for trustless atomic swaps.
- Rule #3: The “Too Good to Be True” Baseline. If an anonymous entity is offering a massive discount on a liquid asset, you are not finding alpha—you are the exit liquidity. Legitimate actors do not sell capital at a loss through private messaging apps.
- Rule #4: Treat Crypto as Irreversible Cash. The moment you sign a transaction or broadcast funds to an unverified address, that capital is gone. Treat every crypto transfer with the exact same finality as handing physical cash to a stranger. There is no customer service desk on the blockchain.
Education is the ultimate firewall. Do not let artificial authority bypass your security.