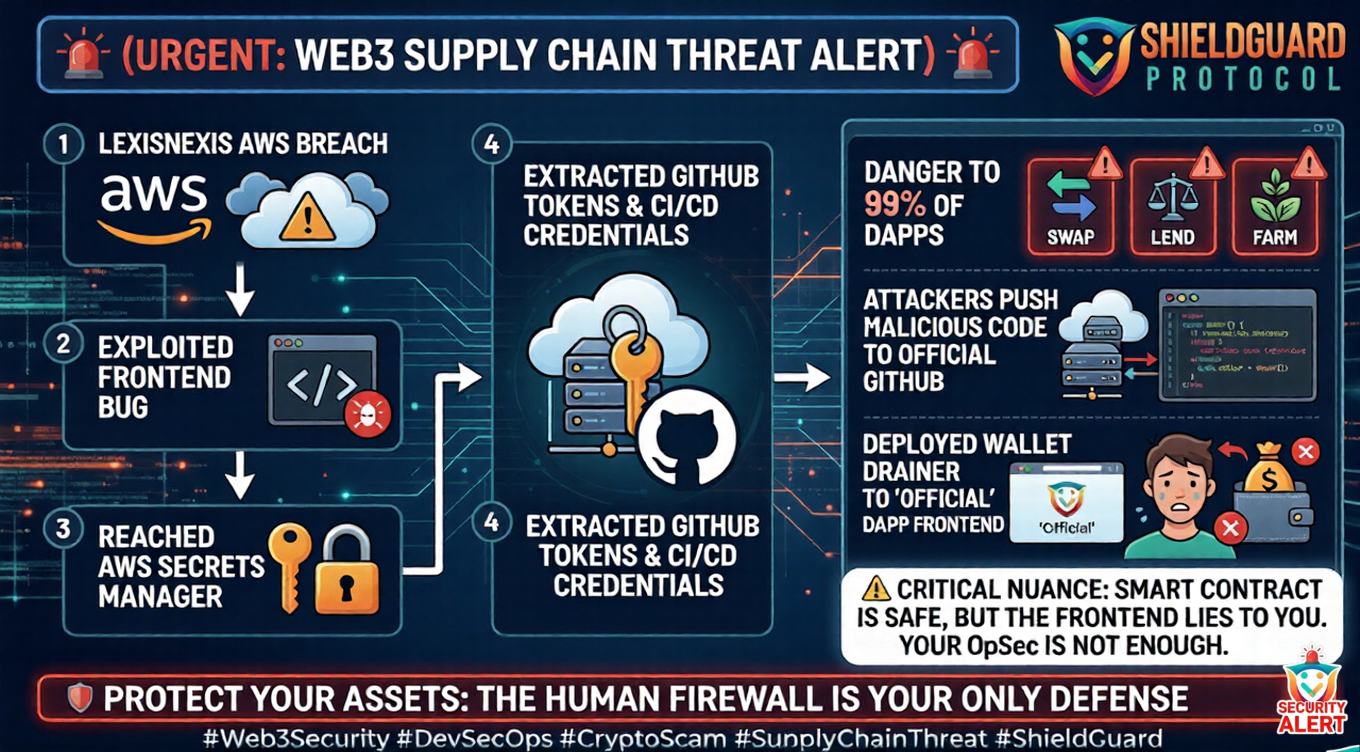
🚨 SCAM ALERT: The Supply Chain Threat – Why Web3 is Vulnerable to the LexisNexis AWS Breach
The most devastating attacks in Web3 often have nothing to do with the blockchain itself. They happen in the traditional Web2 infrastructure that hosts your favorite decentralized applications (dApps).
A massive breach of the LexisNexis AWS (Amazon Web Services) environment has just been confirmed, sending shockwaves through DevSecOps circles globally. While LexisNexis is not a crypto protocol, the exact attack vector used to breach them is the number one threat to Web3 frontends today.
Here is the ShieldGuard breakdown of the incident, the severe danger it poses to the crypto ecosystem, and how to protect yourself.
The Incident: Breaking the Secrets Manager
The LexisNexis breach was a textbook “Supply Chain and Infrastructure” compromise. Attackers did not break into the main database directly; they targeted the perimeter.
- The Entry Point: Attackers exploited a “React2Shell” vulnerability on an unpatched frontend application.
- The Escalation: This initial foothold gave them the keys to the kingdom: the AWS Secrets Manager.
- The Exfiltration: Once inside the Secrets Manager, the attackers successfully extracted highly sensitive infrastructure credentials, including GitHub tokens, Azure DevOps credentials, and internal service keys.
The ShieldGuard Angle: The Web3 Danger
Why does a traditional data broker’s breach matter to a Web3 investor? Because 99% of Web3 protocols host their frontends (the website UI you interact with) on the exact same AWS and GitHub infrastructure.
If a Web3 development team leaves an unpatched vulnerability on their server, attackers can execute the exact same playbook:
- Exploit the Web2 frontend vulnerability.
- Steal the team’s GitHub tokens from the AWS Secrets Manager.
- Use those tokens to push malicious code directly to the protocol’s official GitHub repository.
- The protocol’s website automatically updates with the attacker’s code—a hidden wallet drainer.
When this happens, the URL is correct. The official X account hasn’t been hacked. But the moment an innocent user connects their wallet and clicks “Approve,” their funds are sent directly to the attacker. The underlying smart contract was perfectly safe, but the Web2 supply chain was compromised.
The Defense Protocol: How to Stay Safe
Securing Web3 requires vigilance at both the protocol and user levels.
For Protocol Founders & Developers:
- Strict IAM Policies: Limit Identity and Access Management (IAM) roles. An exposed frontend should never have direct, unmitigated access to critical tokens in the AWS Secrets Manager.
- Patch Management: Vulnerabilities like React2Shell must be patched within hours of a zero-day alert, not days or weeks.
- Deployment Locks: Require manual approvals or multi-signature sign-offs for any code pushed from GitHub to the live production website.
For Retail Users & Investors:
- Stop Blind Signing: Never blindly approve a transaction just because you are on the “official” website. If a site is compromised, the UI will lie to you.
- Read the Contract: Always verify the contract address you are interacting with in your wallet prompt. If a simple “Swap” transaction suddenly asks for an “Infinite Approval” or interacts with a totally new, unverified address, reject it immediately.
- Use Hardware Wallets: Utilize cold storage devices and actively read the hardware display before physically pressing the buttons to confirm a transaction.
Empowering the Human Firewall At ShieldGuard Protocol, we are building the intelligence infrastructure to secure both the code and the human layer of the ecosystem. The only way to defeat supply chain attacks is through relentless operational security and education.