🚨 SECURITY ALERT: The Curve LlamaLend Flash Loan Exploit (Oracle Manipulation)
Severity: High (Targeted Protocol Exploit)
Active Vector: Flash Loan / Price Oracle Manipulation
Target: DeFi Liquidity Providers, Borrowers, and Protocol Users
Executive Summary
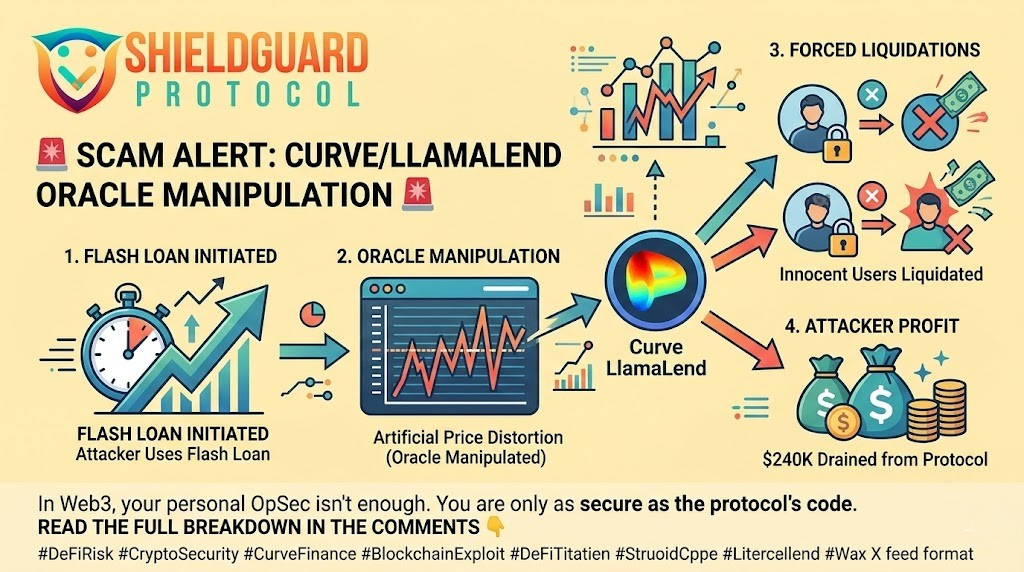
The DeFi ecosystem has just experienced another sophisticated, protocol-level exploit. Curve Finance has confirmed a targeted attack on its sDOLA-crvUSD LlamaLend pool, resulting in an estimated $240,000 drained from the protocol. Blockchain security firm BlockSec has analyzed the exploit, confirming it was executed via a highly technical flash loan attack.
What makes this exploit particularly dangerous is that the victims did not make a single operational security mistake. They did not click a phishing link, they did not connect to a malicious wallet drainer, and they did not expose their seed phrases. They were liquidated purely because the protocol’s oracle configuration was manipulated.
This incident serves as a stark reminder: In Web3, you are not just exposed to human error—you are exposed to the structural integrity of the smart contracts you interact with.
The Anatomy of the Attack: Weaponizing Price Feeds
To understand how innocent borrowers lost their funds, we have to look at how DeFi protocols determine the value of assets. They use “oracles” (price feeds). If an attacker can manipulate that feed, they control the reality of the protocol.
1. The Flash Loan Ignition
The attacker utilized a flash loan—a mechanism allowing them to borrow a massive amount of uncollateralized cryptocurrency, provided it is returned within the exact same transaction block. This gave the attacker the temporary, immense capital required to move the market.
2. Oracle Manipulation
Using the borrowed funds, the attacker aggressively traded within the targeted LlamaLend pool. This massive, sudden volume temporarily distorted the pool’s internal pricing mechanism (the oracle). For a brief moment, the protocol believed the price of the collateral assets was completely different from the actual broader market price.
3. Forced, Unfair Liquidations
Because the protocol’s internal price feed was artificially skewed, the smart contract logic determined that several legitimate borrowers’ positions were suddenly “undercollateralized.” This pushed them below their liquidation thresholds. The attacker then triggered the liquidation of these innocent users’ positions and collected the liquidation bounties for a clean profit before repaying the initial flash loan.
🛡️ ShieldGuard Preventive Education: The Defense Protocol
You cannot fix a protocol’s code yourself, but you can heavily mitigate your risk when interacting with complex DeFi lending markets. Implement these strategies immediately:
1. Maintain Extreme Health Factors
If you are borrowing against collateral in DeFi, do not run your “health factor” (the ratio of collateral to borrowed assets) close to the liquidation threshold. You must maintain a massive buffer to absorb sudden, artificial price shocks caused by flash loans.
2. Audit the Oracle Infrastructure
Before depositing collateral into a lending pool, verify how it calculates price. Does it rely purely on its own internal liquidity pool (highly vulnerable to manipulation), or does it use robust, decentralized oracle networks (like Chainlink or Pyth) that aggregate prices from multiple external exchanges?
3. Beware of Illiquid or Exotic Pools
Flash loan attacks are exponentially easier to execute on pools with lower total value locked (TVL) or exotic token pairings (like sDOLA-crvUSD). It takes significantly less capital to manipulate a shallow pool than a deep one.
4. Compartmentalize DeFi Exposure
Never concentrate your entire portfolio into a single lending protocol or a single liquidity pool. If a protocol-level bug or oracle manipulation occurs, your exposure should only ever be a fraction of your total holdings.
The blockchain executes code exactly as written—even when it’s manipulated. True Web3 security requires understanding not just how to protect your keys, but how to evaluate the protocols you trust.
– The ShieldGuard Security Team