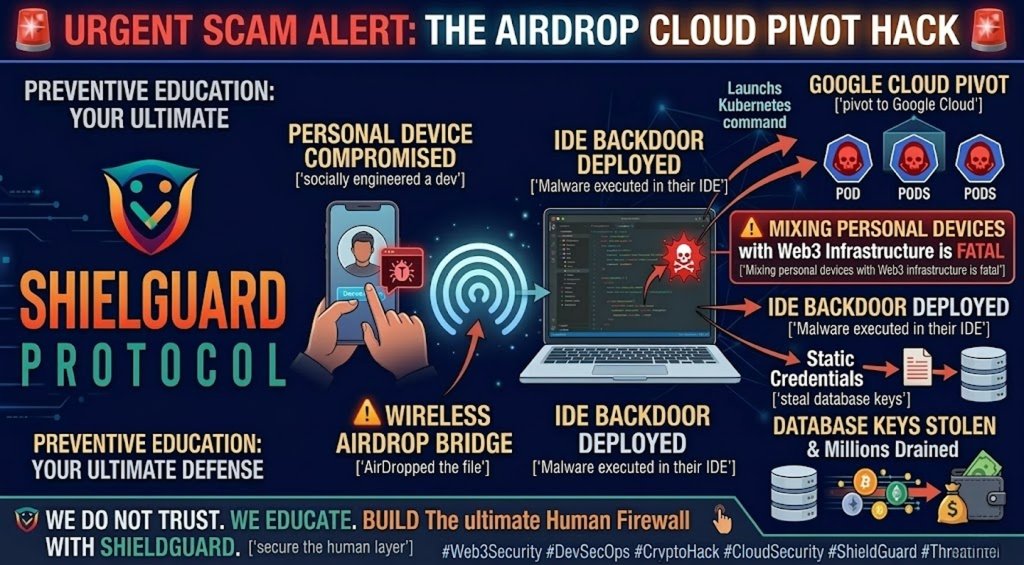
🚨 SCAM ALERT & EDUCATION: The AirDrop Exploit – How State-Sponsored Hackers Breached a Crypto Firm
In Web3 security, the perimeter is rarely breached through a direct brute-force attack on a smart contract. Instead, attackers target the human operators managing the infrastructure.
Cybersecurity researchers at Google Cloud have just published a bombshell report detailing how a North Korean state-sponsored threat group (UNC4899) stole millions from a cryptocurrency organization using a shocking vector: Apple AirDrop and personal device exploitation.
Here is the ShieldGuard Protocol breakdown of this complex “Living-off-the-Cloud” attack, how the air-gap between personal and corporate devices was compromised, and how to defend your protocol’s infrastructure.
The Incident: The AirDrop Trojan
The attack did not begin on the company’s servers; it began on a developer’s personal device via social engineering.
- The Infiltration: Attackers posed as collaborators on a fake open-source project, convincing a developer to download a ZIP archive to their personal device.
- The Bridge: Needing to work on the files, the developer used Apple AirDrop to transfer the archive from their compromised personal device directly to their highly secure corporate workstation.
- The Execution: When the developer opened the archive inside an AI-assisted IDE (Integrated Development Environment), embedded malicious Python code quietly executed in the background. It spawned a backdoor masquerading as a standard Kubernetes command-line tool.
The Escalation: The Cloud Pivot
Once the attackers had a backdoor on the corporate workstation, they executed a devastating “Cloud Pivot.”
- Harvesting Credentials: The malware stole authenticated session tokens, allowing the attackers to pivot directly into the firm’s Google Cloud environment.
- Container Breakout: They hijacked a high-privileged CI/CD (Continuous Integration/Continuous Deployment) service account, deploying backdoors into sensitive Kubernetes pods.
- The Final Drain: The attackers extracted static database credentials stored insecurely in environment variables. With these keys, they accessed the production Cloud SQL database, reset user passwords, disabled Multi-Factor Authentication (MFA) on high-value accounts, and withdrew millions of dollars in digital assets.
The ShieldGuard Angle: The Illusion of the Air-Gap
This attack proves that millions of dollars in Web3 infrastructure can be compromised simply because a developer wanted the convenience of wirelessly transferring a file from their iPhone to their Mac.
Peer-to-peer data transfer mechanisms like AirDrop, Bluetooth, and personal cloud syncing completely bypass corporate network firewalls and email security scanners. When developers mix personal activities with corporate infrastructure, they create an invisible bridge for state-sponsored actors to cross directly into the production environment.
The Defense Protocol: Hardening the DevSecOps Layer
To prevent a cloud pivot attack, Web3 organizations must enforce strict device isolation and secrets management.
1. Disable Peer-to-Peer Transfers
Corporate workstations handling Web3 infrastructure or cloud deployments must have AirDrop, personal Bluetooth sharing, and unauthorized USB access completely disabled via Mobile Device Management (MDM) policies.
2. Isolate Cloud Environments
Adopt strict “Zero Trust” architecture. A developer’s workstation should never have standing, unmitigated access to production cloud environments. Implement context-aware access and require hardware security keys (like YubiKeys) for all cloud authentication.
3. Never Hardcode Secrets
The attackers succeeded because database credentials were left sitting in environment variables. Never hardcode API keys, database passwords, or wallet seed phrases in source code or container environments. Use dedicated, encrypted secret management vaults (like HashiCorp Vault or AWS Secrets Manager).
Empowering the Human Firewall
At ShieldGuard Protocol, we secure the human layer. The most sophisticated cloud security architecture in the world can be defeated by a single compromised file transfer. Trust nothing, isolate everything.