🚨 The Aeternum C2 Threat – When Malware Hides on the Blockchain
Severity: Critical (Decentralized Malware Command & Control)
Active Vector: Malicious Smart Contracts on Polygon, Phishing Downloads, and Clipboard Hijacking
Target: Crypto Wallet Users, Retail Investors, and Global Web3 Participants
Welcome to the latest security breakdown from ShieldGuard Learn. Our core mission at ShieldGuard Protocol is to actively combat scams, educate users, and protect the Web3 ecosystem. Today, we are analyzing a highly sophisticated new threat that turns the very technology we champion against us: the Aeternum C2 Botnet.
Our core team members have over 18 years of working experience in the financial industry, which gives us a sharp radar for detecting when traditional financial fraud tactics evolve into complex Web3 exploits. Aeternum C2 represents a dangerous evolution in cybercrime, moving away from vulnerable centralized servers and hiding its malicious operations in plain sight on the public Polygon blockchain.
Here is exactly how this threat works, why it matters, and how you can protect your assets.
🦠 What is a Command-and-Control (C2) Server?
To understand Aeternum, you first have to understand how standard malware operates. When a hacker infects a computer (turning it into a “bot”), that bot needs to receive instructions. It reaches out to a centralized Command-and-Control (C2) server owned by the hacker to ask, “What should I do next?”
Historically, law enforcement and cybersecurity firms defeat botnets by finding these centralized servers and shutting them down, effectively cutting off the head of the snake.
⛓️ How Aeternum C2 Changes the Game
Aeternum completely eliminates the centralized server. Instead, it uses the Polygon blockchain to store and distribute its malicious commands.
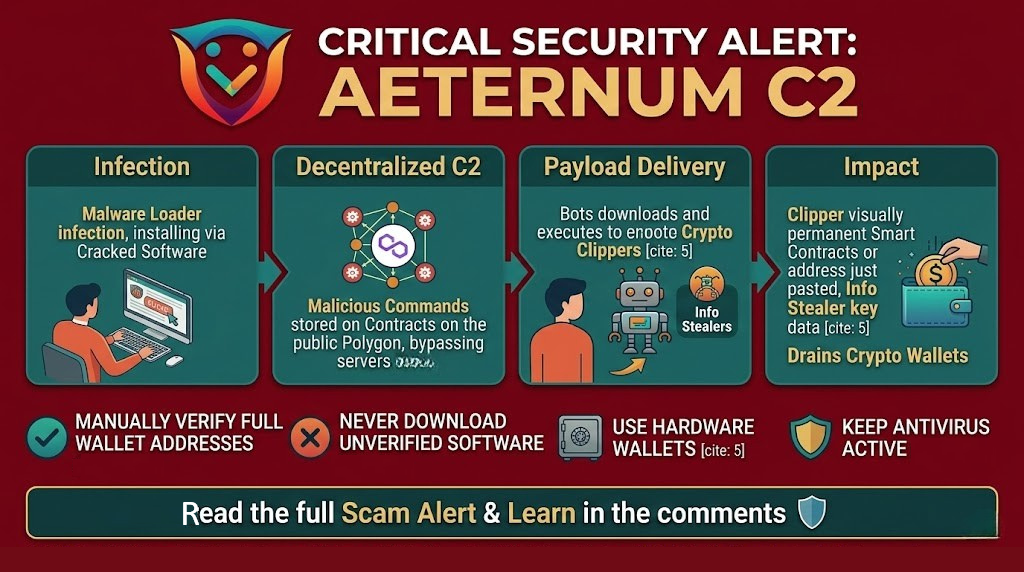
Here is the step-by-step breakdown of an Aeternum attack:
- The Infection: A user accidentally downloads the Aeternum loader (often disguised as cracked gaming tools, fake job assessment repositories, or malicious email attachments).
- The Smart Contract: The hacker, operating a secure web panel, writes an encrypted command into a smart contract and deploys it as a standard transaction on the Polygon network.
- The Retrieval: The infected computer silently queries public Polygon RPC (Remote Procedure Call) endpoints. It reads the smart contract, decrypts the command, and executes the attack.
⚠️ Why is this so Dangerous?
- Unstoppable Infrastructure: Because blockchains are decentralized and immutable, authorities cannot simply “take down” a smart contract. Once a command is on the Polygon ledger, it is permanent.
- Incredibly Cheap: The operational costs for the hacker are practically zero. Just $1 worth of MATIC can fund over 100 command transactions.
- Severe Payloads: Aeternum is a delivery mechanism. Hackers are using it to deploy “clippers” (malware that alters crypto wallet addresses when you copy and paste them), information stealers that drain your private keys, and Remote Access Trojans (RATs).
🛡️ How to Protect Yourself
Because the source of the attack (the blockchain) cannot be taken down, the only way to defend against Aeternum is at the endpoint—your own devices and wallets.
- Double-Check Every Download: Aeternum relies on social engineering and phishing to get onto your machine. Never download unverified software, open suspicious email attachments, or execute code from untrusted developer repositories.
- Beware the Clipboard: Because Aeternum frequently deploys crypto clippers, always manually verify the first and last five characters of a wallet address after pasting it into a transaction window.
- Use Hardware Wallets: Even if a botnet loader infects your computer, a hardware wallet keeps your private keys isolated offline. The malware cannot authorize a transaction without your physical confirmation on the device.
- Keep Antivirus Active: While Aeternum uses anti-evasion tactics, keeping your endpoint protection software updated is critical for catching the payloads it attempts to drop.
Stay vigilant, verify everything, and protect your keys.