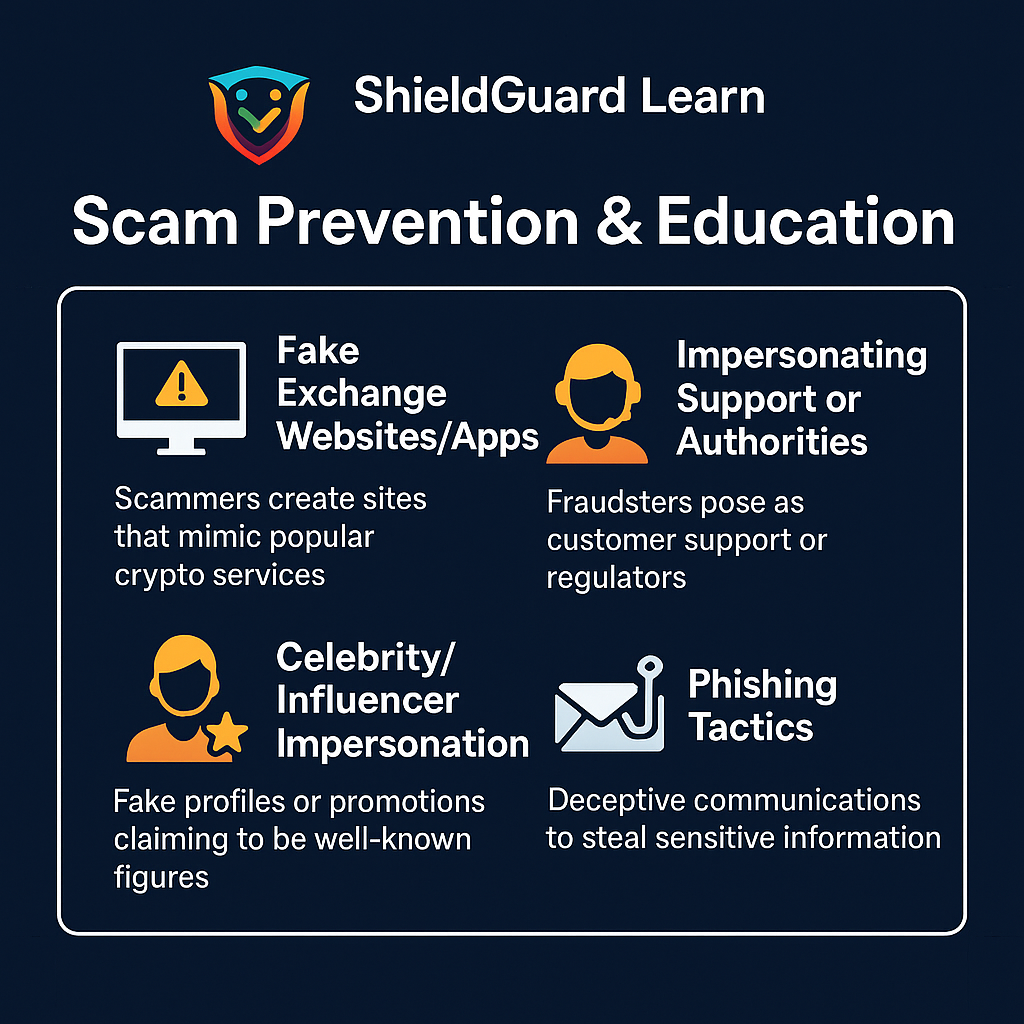
ShieldGuard Learn: Scam Prevention & Education
Topic: Impersonation & Fake Platforms / Phishing
Introduction:
In the rapidly evolving world of cryptocurrency, vigilance is paramount. Scammers are constantly developing sophisticated tactics to defraud investors. Among the most prevalent and dangerous are impersonation scams and phishing attempts, which leverage deception to gain unauthorized access to your assets or convince you to send money to fraudulent platforms. This report will detail these threats, drawing insights from observed industry trends and best practices in cybersecurity.
1. What are Impersonation & Fake Platform Scams?
Impersonation scams involve fraudsters pretending to be a trustworthy entity, such as a legitimate crypto exchange, a well-known project, a government agency, a celebrity, or even a friend or family member. The goal is to trick victims into believing they are interacting with a genuine source, thereby lowering their guard.
Fake platform scams are often a component of impersonation, where criminals create fraudulent websites or applications that mimic legitimate crypto services. These platforms are designed to steal your login credentials, personal information, or directly solicit funds.
2. Common Impersonation & Fake Platform Tactics:
Fake Exchange Websites/Apps: Scammers create highly convincing replicas of popular cryptocurrency exchanges or wallet providers. These sites often have very similar URLs (e.g., “binanc.com” instead of “binance.com“). They might look identical to the real platform, complete with login pages, market data, and portfolio displays. The Trap: Users unknowingly enter their login credentials, seed phrases, or private keys into these fake platforms, giving scammers direct access to their real accounts.
Impersonating Support or Authorities: Fraudsters may contact you via email, social media, or even phone, posing as customer support from an exchange, a blockchain security team, or even a regulatory body. They might claim there’s an issue with your account, suspicious activity, or a “necessary” security upgrade. The Trap: They ask for sensitive information (passwords, 2FA codes), remote access to your device, or instruct you to transfer funds to a “secure” wallet, which is, in fact, theirs.
“Pig Butchering” Scams (Romance/Investment Scams): These are sophisticated, long-term scams where fraudsters build a relationship with the victim (often romantic) over weeks or months, eventually convincing them to invest in a fake crypto platform controlled by the scammer. The initial returns may seem legitimate, but the victim’s funds are ultimately stolen.
Celebrity/Influencer Impersonation: Scammers create fake social media profiles or websites impersonating well-known figures in the crypto space. They might promote fake giveaways or investment opportunities, promising exorbitant returns.
3. What is Phishing?
Phishing is a broader term for attacks that attempt to trick individuals into revealing sensitive information or performing actions by masquerading as a trustworthy entity. While often linked to impersonation, phishing specifically refers to the method of deception—usually through deceptive communications.
4. Common Phishing Tactics:
Email Phishing: Scammers send emails that appear to be from legitimate sources (e.g., your crypto exchange, a popular DeFi project, or a service you use). These emails often contain urgent warnings (“Your account has been compromised!”) or enticing offers (“Claim your free tokens!”). The Trap: The email contains malicious links that lead to fake login pages (fake platforms) or download malware.
SMS Phishing (Smishing): Similar to email phishing but delivered via text messages. These messages might contain links to fake websites or urge you to call a fraudulent number.
Social Media Phishing: This includes direct messages on platforms like X (formerly Twitter), Discord, or Telegram, pretending to be from project admins, customer support, or other users. They often share malicious links or ask for sensitive information.
“Dusting” Attacks: While not directly a phishing attempt, dusting involves sending tiny amounts of crypto (“dust”) to thousands of wallets. The hope is that a user might accidentally transact with the dust, allowing scammers to de-anonymize the wallet owner and target them with more personalized phishing attacks.
5. How to Spot & Avoid Impersonation/Phishing Scams (Key Takeaways from ShieldGuard):
Verify URLs Carefully: Always manually type the website address or use a trusted bookmark. Never click on links in suspicious emails, texts, or social media messages. Look for “HTTPS” and the padlock icon. Check for subtle misspellings in the domain name (e.g., coibase.com instead of coinbase.com).
Question Unsolicited Communications: Be highly skeptical of any unexpected messages, emails, or calls, especially those asking for personal information, login details, or instructing you to transfer funds.
Don’t Share Sensitive Information: Legitimate entities will never ask for your private keys, seed phrases, or two-factor authentication (2FA) codes. Never share these with anyone.
Use Strong, Unique Passwords and 2FA: Enable two-factor authentication on all your crypto accounts and use strong, unique passwords.
Be Wary of “Too Good to Be True” Offers: If an investment promises unusually high, guaranteed returns with little to no risk, it’s almost certainly a scam. Free crypto giveaways are almost always fraudulent.
Research Thoroughly: Before investing in any new platform or project, conduct extensive due diligence. Check official channels, read whitepapers, and look for independent reviews.
Install Antivirus/Anti-Malware: Keep your devices protected with up-to-date security software.
Educate Yourself Continuously: Stay informed about the latest scam tactics. Resources like ShieldGuard Learn are designed to equip you with the knowledge to protect yourself.
Conclusion:
Impersonation and phishing scams are insidious threats in the crypto space. By understanding their mechanics and diligently applying preventative measures, you can significantly reduce your risk of falling victim. ShieldGuard Protocol is committed to providing our community with the knowledge and tools needed to navigate the digital asset landscape safely and confidently.