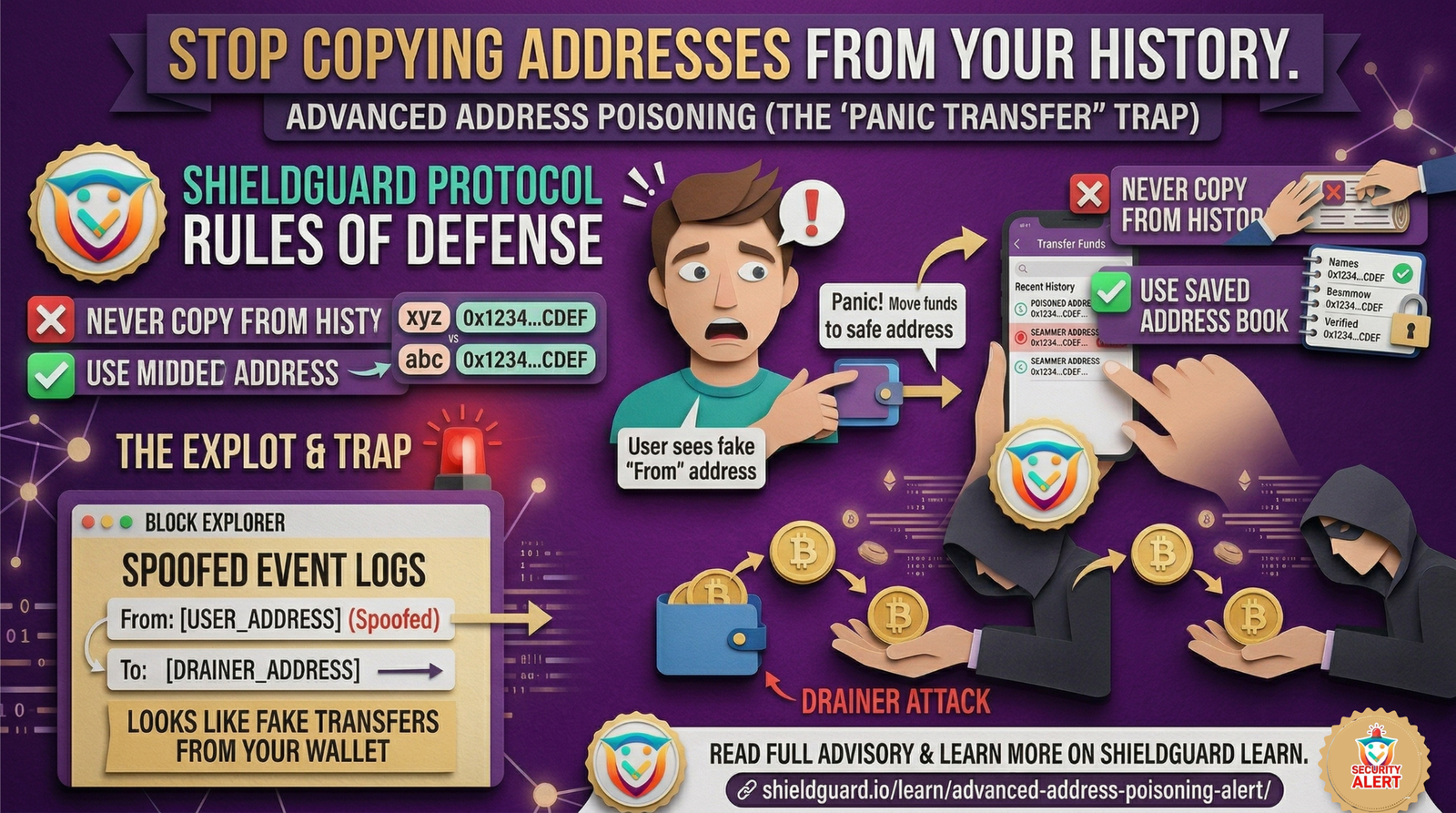
🚨 SCAM ALERT: Advanced Address Poisoning & The “Panic Transfer” Trap
Threat Level: 🔴 CRITICAL
Target: All Web3 Wallet Users (Hot Wallets & Hardware/Cold Storage)
The Incident: The Evolution of Address Poisoning
The classic “0-value” address poisoning scam has received a massive, highly deceptive upgrade.
Historically, scammers would send 0-value transactions to your wallet from an address that looks very similar to yours (matching the first and last few characters) hoping you would accidentally copy it for a future transfer.
Today, attackers have bypassed the need to send you anything at all. They are now actively manipulating smart contract event logs to spoof the “From” address directly on block explorers like Etherscan, making it look exactly like your own cold wallet initiated an unauthorized transfer.
The Exploit: How Event Log Spoofing Works
To understand how to protect yourself, you must understand the mechanics of the illusion:
- The Malicious Contract: The scammer deploys a fake, counterfeit token contract.
- The Spoofed Event: The scammer triggers a function within their own fake contract that emits a standard
Transferevent to the blockchain. - The Illusion: Because the scammer controls the fake contract, they can program the event to declare your wallet as the “Sender” and their lookalike wallet as the “Receiver.”
- The Explorer Trap: Block explorers (like Etherscan, Solscan, etc.) automatically index these events. When you check your wallet address, the explorer displays an outgoing transaction that looks 100% legitimate, even though your actual assets never moved and your private keys are completely safe.
The Trap: Weaponizing Your Panic
This attack relies entirely on psychological manipulation rather than cryptographic hacking. Here is the exact sequence of the “Panic Transfer” trap:
- The Shock: You check your wallet or block explorer and see an unauthorized outgoing transfer that you did not sign.
- The Panic: Assuming your private keys have been compromised and a drainer is actively emptying your wallet, your fight-or-flight response kicks in.
- The Fatal Mistake: In a rush to “save” your remaining funds, you quickly try to transfer your assets to a backup or exchange wallet. To do this fast, you go to your transaction history and copy the address you thought was your safe backup.
- The Drain: In reality, you just copied the scammer’s spoofed, lookalike address from the poisoned event log. You authorize the transfer, and your real assets are sent directly to the attacker.
🛡️ Preventive Education: The ShieldGuard Rules of Defense
Your wallet cannot be hacked through an event log. The scammer needs you to authorize the final transaction. Protect your capital by strictly enforcing these security habits:
1. NEVER Copy from Transaction History
Treat your wallet’s transaction history as a public, unverified bulletin board. Anyone can write to it. Never use it as an address book.
2. Use the “Whitelist” or “Address Book” Feature
Most major wallets (MetaMask, Phantom, Rabby) allow you to save frequently used addresses to an internal address book. Only initiate transfers to addresses saved and named in this verified list.
3. Stop Relying on “Prefix/Suffix” Checking
Scammers use vanity address generators to ensure the first 5 and last 5 characters of their poisoned address match yours perfectly. If you must manually verify an address, check characters in the middle of the string.
4. Hide Spam on Block Explorers
Take advantage of the “Hide” or “Ignore” features on your wallet interface and block explorers. If you see a random 0-value token or an unverified transaction, hide it immediately so you cannot accidentally interact with it later.
5. Don’t Let Panic Dictate Your Actions
If you see a suspicious transaction, stop and breathe. Check your actual asset balances. If your Ethereum, USDC, or SHPRO balances haven’t changed, your wallet is not breached. The transaction is just a visual illusion created by a fake token contract.
The ShieldGuard Perspective
At ShieldGuard Protocol, we believe that true Web3 security requires more than just smart contract audits—it requires empowering the user. Scammers are exploiting the gaps in how blockchain data is displayed to the public. By understanding these deep technical manipulations, you transform yourself from a target into a hardened Web3 native.
Stay vigilant. Verify every character. Protect your portfolio.