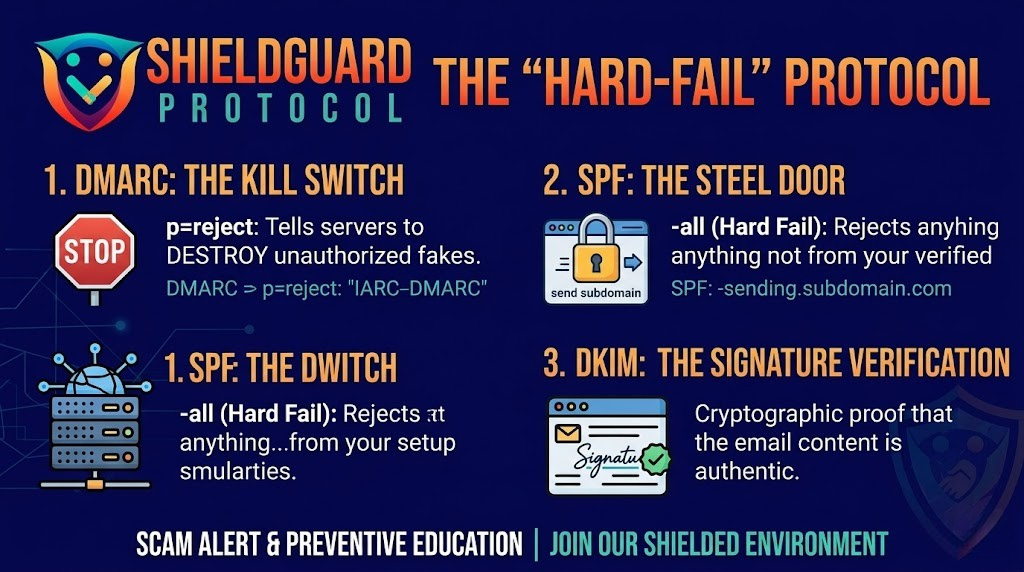
🛡️ ShieldGuard Learn: The “Hard-Fail” Protocol
Protecting Your Project’s Voice in a World of Spoofing
In the Web3 ecosystem, your domain name is more than just a website—it is your identity and your reputation. If a hacker can send emails using your voice, they don’t just steal data; they drain the trust you’ve spent years building.
At ShieldGuard, we recently detected a sophisticated “SES Hijacking” campaign where attackers tried to use unauthorized AWS accounts to impersonate our brand. We didn’t just stop it; we locked the gates. Today, we are open-sourcing our Domain Lockdown Protocol so every developer, founder, and project can secure their perimeter.
1. The “Kill Switch”: DMARC p=reject
Most projects use p=none (monitoring only). In the world of crypto, that isn’t enough. You need to tell global mail servers exactly what to do with a fake: Destroy it.
The Directive: Add this TXT record to your root domain (_dmarc):
v=DMARC1; p=reject; rua=mailto:dmarc@yourdomain.io
- Why it matters: This ensures that if a spoofed email fails authentication, it is instantly deleted by Google, Microsoft, and Yahoo before your user ever sees it.
2. The “API Fortress”: Subdomain Isolation
Never send automated emails (like alerts or newsletters) from your root domain. By using a dedicated send or mail subdomain, you isolate your reputation.
The Directive: Add a specific SPF record for your sending subdomain:
- Host:
send - Value:
v=spf1 include:amazonses.com -all - The “-all” Secret: Most people use
~all(Soft-fail), which is like a “Please don’t enter” sign. We use-all(Hard-fail). It’s a steel door. It tells servers: “If it’s not from our verified setup, it’s a fraud. Reject it.”
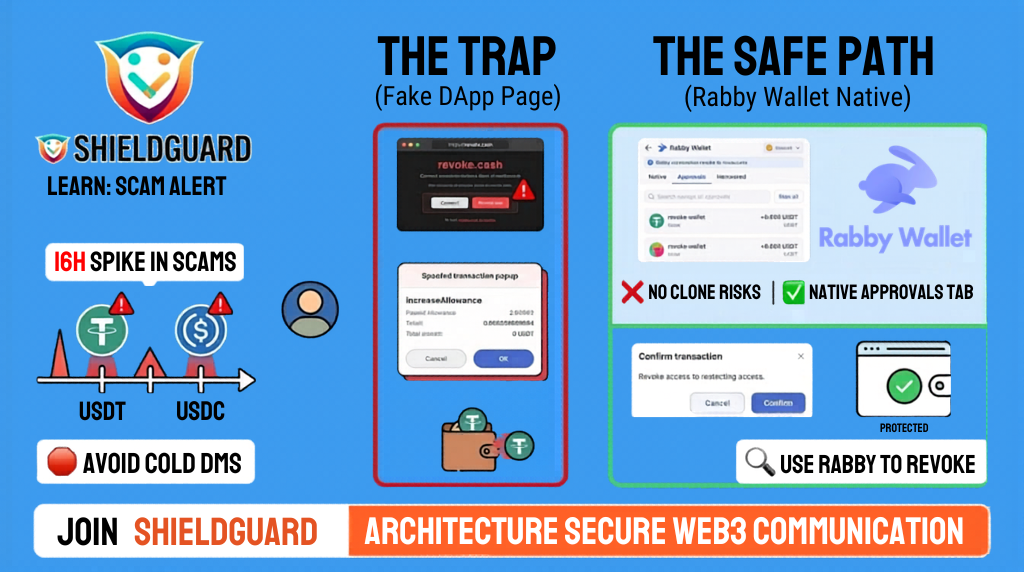
3. The User’s Shield: “View Original Message”
We want our community to be their own first line of defense. Before you ever click a link, take three seconds to check the “Source Code” or “View Original” in your email app.
The Red Flags to look for:
- Message ID: Does it match the service? A legitimate Resend email should end in
@resend.comor@amazonses.com. - SPF Status: If it says SPF: FAIL, the email is an impostor.
- DKIM: Ensure the “Signed By” domain matches the actual “From” address.
A Message to Our Peers
We’ve watched “SES Hijacking” become a trend where attackers cycle through AWS regions to find weak domains. We’ve hardened our system so these emails are deleted at the gate. Don’t leave your back window open. Move to Hard-Fail today.
Join the front lines of Web3 security. Become a ShieldGuard member today and stay protected within our shielded ecosystem where we stay one step ahead of the bad actors.