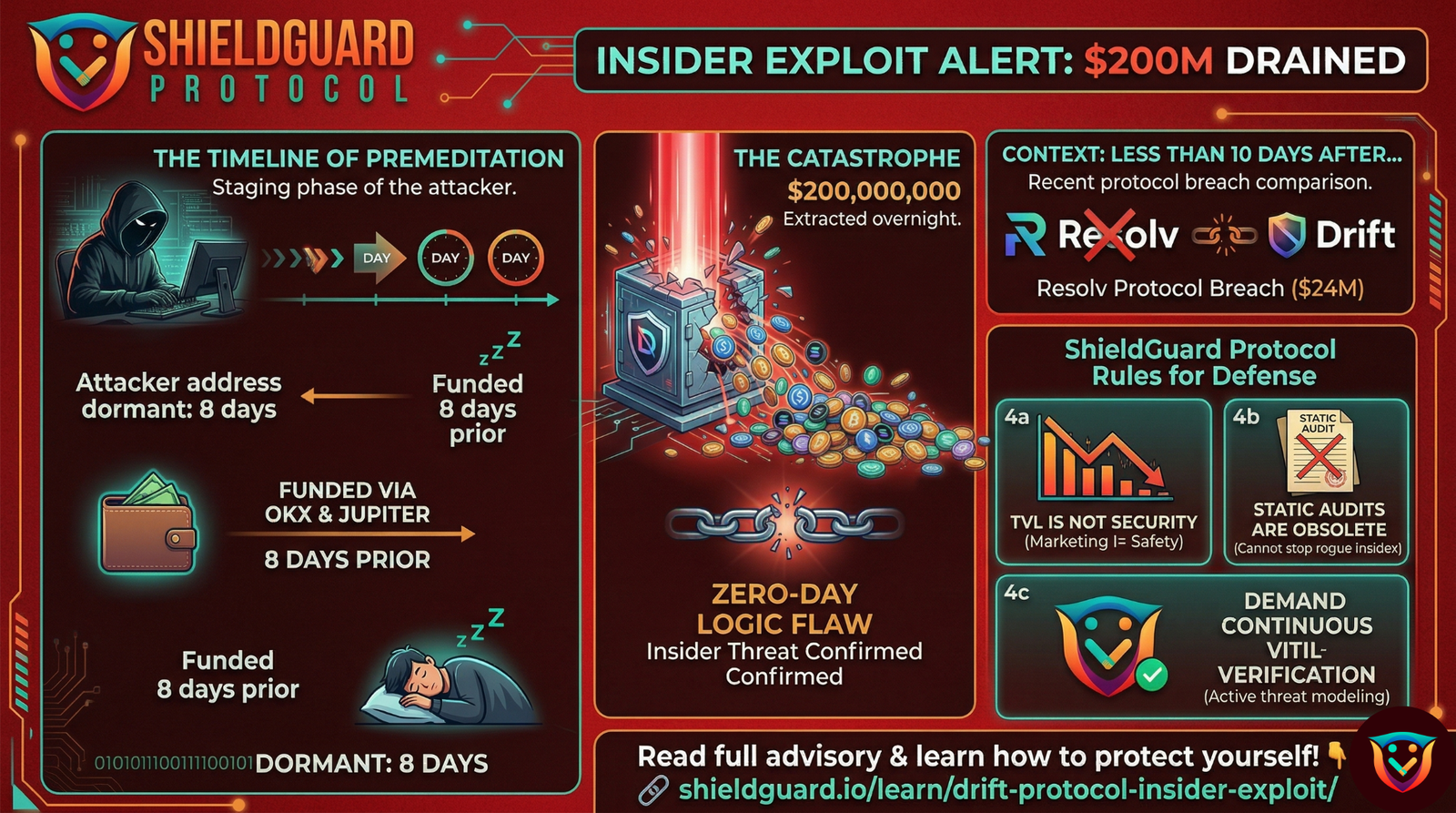
🚨 SECURITY ADVISORY: The $200M Drift Protocol Exploit & Insider Threat Reality
Threat Level: 🔴 CRITICAL
Target: DeFi Protocol Users, Liquidity Providers, and Solana Ecosystem Investors.
The Incident: Catastrophic Liquidity Drain
Within the last 12 hours, the Solana-based trading platform Drift suffered a catastrophic smart contract exploit, resulting in an estimated $200 million total loss. This represents one of the most severe liquidity drains of the current quarter, occurring less than 10 days after the highly publicized Resolv Protocol breach.
The Vector: Premeditated On-Chain Execution
On-chain forensics indicate that this was not a chaotic or opportunistic hack, but rather a highly calculated, staged extraction.
- The Staging Phase: The primary exploiter address was generated and funded 8 days prior to the attack via OKX and Jupiter DEXs.
- The Dormancy Period: Following the initial funding, the wallet remained completely dormant. This deliberate inactivity successfully bypassed standard early-warning heuristics and on-chain monitoring bots.
- The Extraction: The attacker waited for optimal liquidity conditions before striking a highly complex smart contract vulnerability overnight, executing the drain with maximum efficiency.
The Threat Reality: Insider Exploitation
Given the extreme precision required to execute an attack of this magnitude, it must be explicitly stated: drains of this nature are orchestrated by insiders. The attacker possessed an intimate, behind-the-scenes understanding of the protocol’s architecture. Knowing exactly where an unpatched zero-day vulnerability resides, how to bypass internal risk monitors, and the exact timing required to maximize the extraction points directly to threat actors with internal access to the code floor plan.
🛡️ Preventive Education: The ShieldGuard Rules of Defense
This event shatters one of the most dangerous misconceptions in the cryptocurrency space: the assumption that a high Total Value Locked (TVL) and massive popularity equate to technical security. To protect your capital in an environment where even tier-1 protocols are compromised from within, strictly adhere to these defense protocols:
1. The “TVL Fallacy”
Do not use Total Value Locked as a metric for security. Billions of dollars in deposited capital do not insulate a smart contract against the developers who wrote it. Hype and high yield often mask critical administrative and architectural vulnerabilities.
2. Static Audits Are Obsolete
A static security audit conducted months prior to an event cannot predict or stop an insider who decides to exploit a logic flaw today. Investors must transition from trusting static PDF badges to demanding active, dynamic threat modeling and continuous code verification.
3. Multi-Sig & Admin Key Verification
When vetting a protocol, the most critical factor is identifying who controls the treasury. If a project lacks strict, decentralized multi-signature key management, a single compromised (or rogue) insider can drain the liquidity pool instantly.
4. Risk Compartmentalization
Never allocate capital you cannot afford to lose into a single smart contract, regardless of its reputation. If an insider initiates a catastrophic drain, decentralized protocols do not have a recovery mechanism or customer support desk to reverse the transaction.
The ShieldGuard Perspective
At ShieldGuard Protocol, we recognize that the most severe threats facing retail investors today are not just external phishing links, but structural vulnerabilities and internal actors. Security requires continuous, raw technical verification. We are committed to building an ecosystem that models these deep technical layers, ensuring our community has the intelligence required to navigate Web3 safely.