🚨 SCAM ALERT: The “Fake Safeguard” Telegram Hijack & Drainer
Threat Level: 🔴 CRITICAL
Target: Crypto Traders, Telegram Bot Users (e.g., Polymarket, Kreopolybot), and Support Seekers.
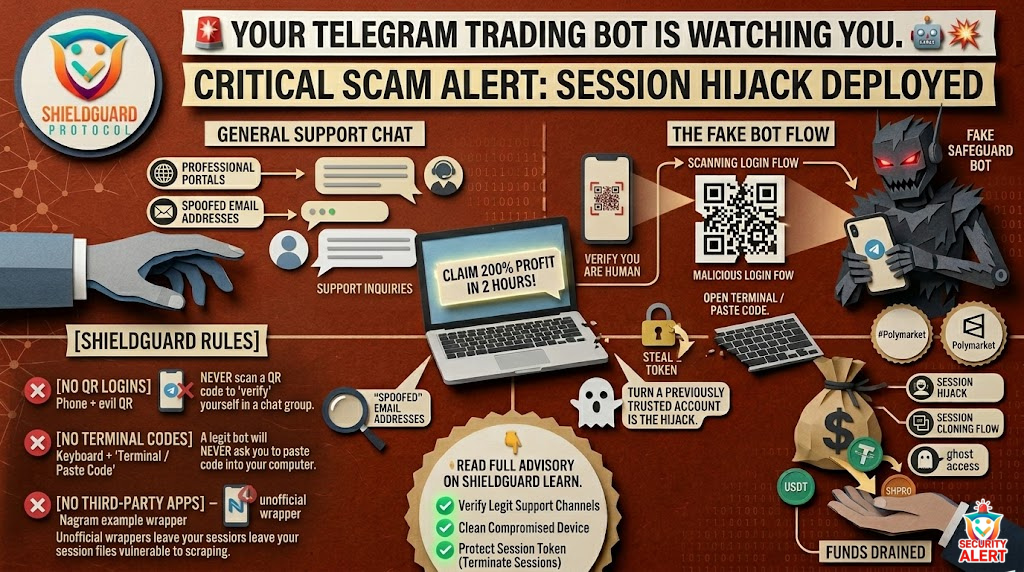
The Incident: The “Fake Safeguard” Hijack
A highly sophisticated attack vector is currently devastating retail traders who use automated Telegram trading bots. Scammers are lurking in official or general support channels, waiting for users to seek help. When a user joins the group or asks a question, they are prompted to “verify” their identity using what appears to be a standard “Safeguard bot.”
This is not a security check—it is a deceptive trap designed to execute a complete session hijack, take over the user’s communications, and drain their associated crypto wallets.
The Anatomy of the Scam
- The Support Trap: Users seeking assistance are redirected to a fake verification bot designed to mimic legitimate anti-spam tools.
- The Verification Exploit: The bot creates a false sense of urgency, instructing the user to either scan a QR code to log in or prompting them to copy and paste a “verification code” directly into their computer’s Terminal or Windows Run dialog.
- Session Theft & Drain: Scanning the malicious QR code instantly grants the attacker full access to the victim’s Telegram session token. If the user was tricked into pasting code, it executes a silent script (often a Powershell command) that installs malware, steals local session files, and hunts for browser extensions and wallet private keys.
- The Silent Takeover: The attacker assumes control of the Telegram account to spam the victim’s contacts. More critically, they monitor the account for any funds deposited to legitimate trading bots. Once the funds arrive, they are instantly drained to the scammer’s wallet.
Security Briefing: Post-Breach Realities
When an attack like this occurs, victims are left with critical questions about their digital safety and the possibility of recovery. Here are the absolute technical truths regarding session hijacking:
- Ghost Access & Session Tokens: If an attacker captures a session token, they have full access without needing a password. However, navigating to the app’s privacy settings to select “Terminate all other sessions,” followed by permanently deleting the account via the official portal, successfully invalidates the hijacked token on the attacker’s end. Re-registering afterward does not typically trigger a shadowban.
- Third-Party Clients: Using unofficial, third-party messaging clients (like Nagram) introduces severe vulnerabilities. Unofficial apps may not sandbox data properly, making it easier for token stealers to scrape session files across multiple accounts.
- The “Recovery” Myth: Once funds are sent to a scammer’s wallet, they are gone. There is no technical or legal “undo” button on the blockchain. Anyone sliding into direct messages offering “recovery services” or claiming to be a hacker who can retrieve the stolen funds is executing a secondary advance-fee scam.
- Device Integrity: If a user only scanned a QR code or clicked a malicious login link, terminating the active session secures the account. However, if any code was copied and pasted into a computer terminal, the device is compromised at the root level. A standard mobile or desktop security scan is insufficient; backing up essential files and performing a full factory reset (OS reinstall) is the only way to guarantee a clean environment.
🛡️ Preventive Education: Protecting Your Assets
Our dedicated security sections have already been active for weeks, providing continuous threat intelligence to prevent these exact scenarios. To ensure your trading environment remains secure, strictly adhere to these protocols:
- Never Paste Code: A legitimate verification bot or website will never ask you to open your computer’s Terminal, Command Prompt, or Run dialog to paste commands. If you see this instruction, you are being targeted by malware.
- Beware of QR Logins: Be extremely wary of scanning QR codes to “verify your humanity” in a chat group. This is the primary method for bypassing passwords and stealing session tokens.
- Stick to Official Apps: Delete third-party wrappers and only use the official desktop and mobile applications downloaded directly from verified app stores.
- Isolate Your Trading: Never seek support for financial tools in public “General” chat groups where scammers deploy these fake Safeguard bots. Always use the official, verified channels provided by the protocol.
Stay vigilant, verify every interaction, and protect your digital footprint.